漏洞概要 关注数(24) 关注此漏洞
>
漏洞详情
披露状态:
2015-05-21: 细节已通知厂商并且等待厂商处理中
2015-05-25: 厂商已经确认,细节仅向厂商公开
2015-06-04: 细节向核心白帽子及相关领域专家公开
2015-06-14: 细节向普通白帽子公开
2015-06-24: 细节向实习白帽子公开
2015-07-09: 细节向公众公开
简要描述:
文件遍历
详细说明:
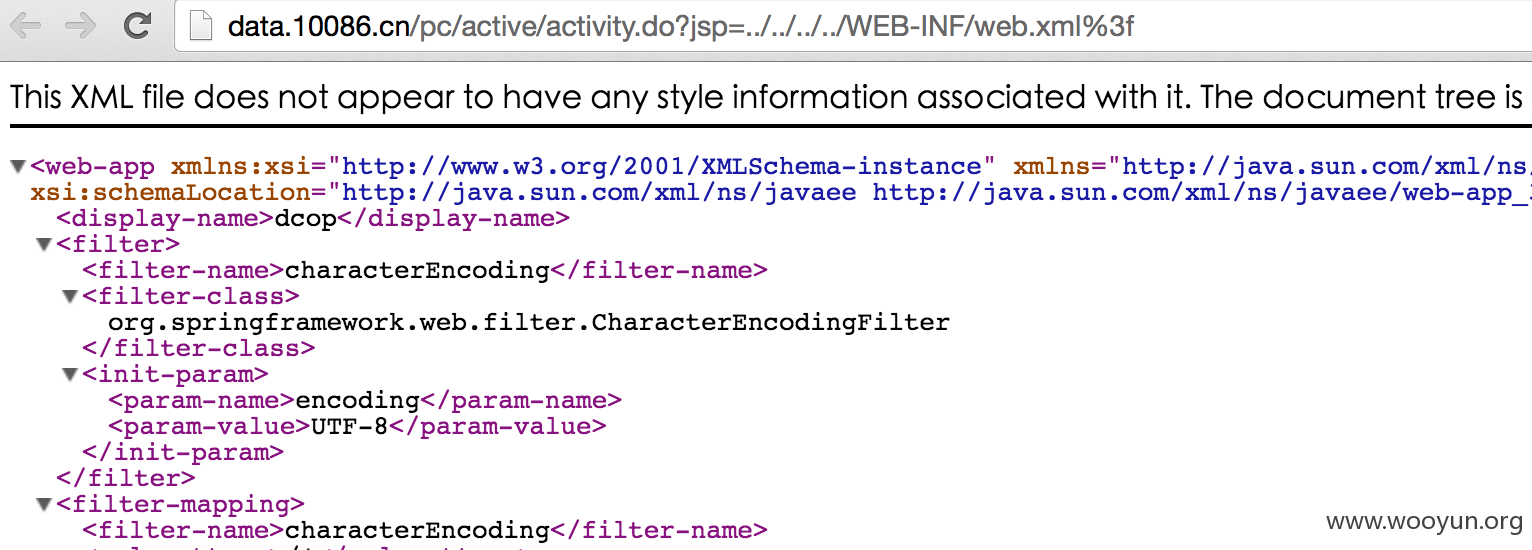
参数存在任意文件读取。poc:
漏洞证明:
文件信息证明
This XML file does not appear to have any style information associated with it. The document tree is shown below.
<web-app xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance" xmlns="http://java.sun.com/xml/ns/javaee" xmlns:web="http://java.sun.com/xml/ns/javaee/web-app_2_5.xsd" xsi:schemaLocation="http://java.sun.com/xml/ns/javaee http://java.sun.com/xml/ns/javaee/web-app_3_0.xsd" id="WebApp_ID" version="3.0">
<display-name>dcop</display-name>
<filter>
<filter-name>characterEncoding</filter-name>
<filter-class>
org.springframework.web.filter.CharacterEncodingFilter
</filter-class>
<init-param>
<param-name>encoding</param-name>
<param-value>UTF-8</param-value>
</init-param>
</filter>
<filter-mapping>
<filter-name>characterEncoding</filter-name>
<url-pattern>/*</url-pattern>
</filter-mapping>
<context-param>
<param-name>contextConfigLocation</param-name>
<param-value>classpath:/spring-core-context.xml</param-value>
</context-param>
<listener>
<listener-class>
org.springframework.web.context.ContextLoaderListener
</listener-class>
</listener>
<listener>
<listener-class>
com.aspire.dcop.core.common.DcopPlatformLogListener
</listener-class>
</listener>
<servlet>
<servlet-name>spring</servlet-name>
<servlet-class>org.springframework.web.servlet.DispatcherServlet</servlet-class>
<load-on-startup>1</load-on-startup>
</servlet>
<servlet-mapping>
<servlet-name>spring</servlet-name>
<url-pattern>*.do</url-pattern>
</servlet-mapping>
<welcome-file-list>
<welcome-file>/index.do</welcome-file>
</welcome-file-list>
修复方案:
检查传入的参数,对传入的参数做白名单
版权声明:转载请注明来源 路人甲@乌云
>
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:6
确认时间:2015-05-25 14:01
厂商回复:
CNVD确认并复现所述情况,已经转由CNCERT向中国移动集团公司通报,由其后续协调网站管理部门处置.
最新状态:
暂无