漏洞概要
关注数(24)
关注此漏洞
>
漏洞详情
披露状态:
2016-03-01: 细节已通知厂商并且等待厂商处理中
2016-03-06: 厂商已经主动忽略漏洞,细节向公众公开
简要描述:
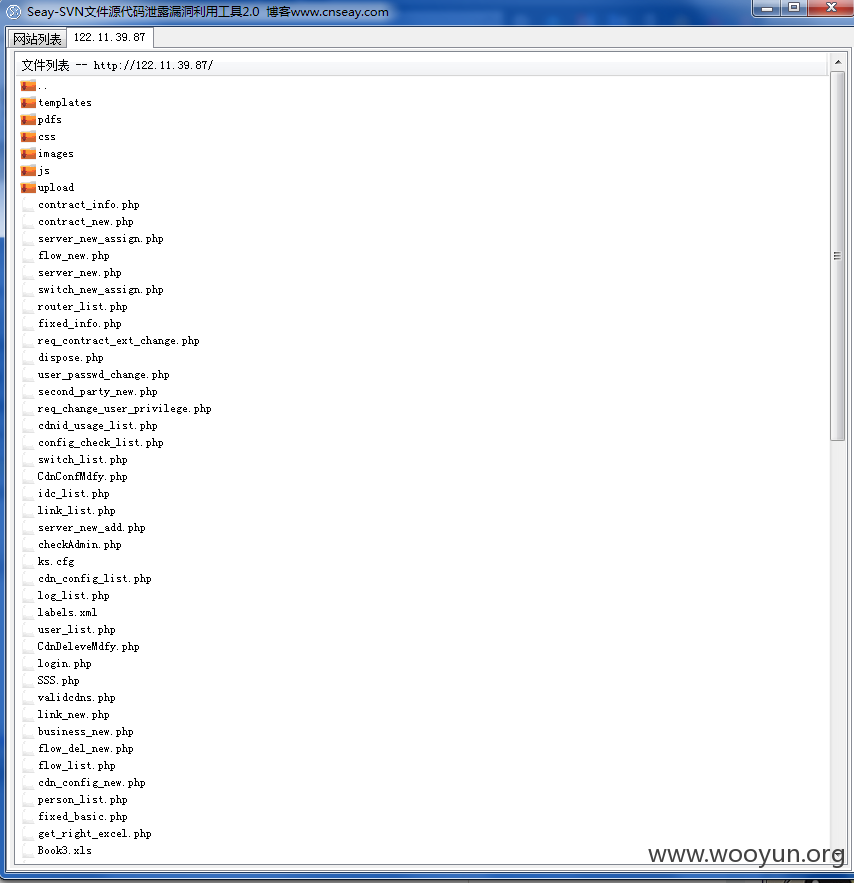
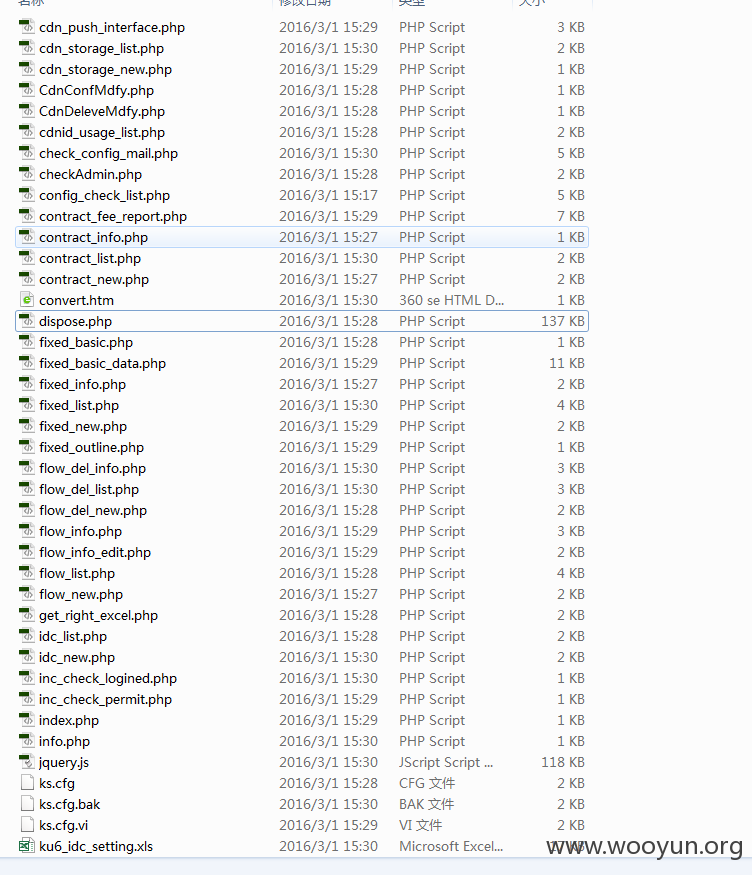
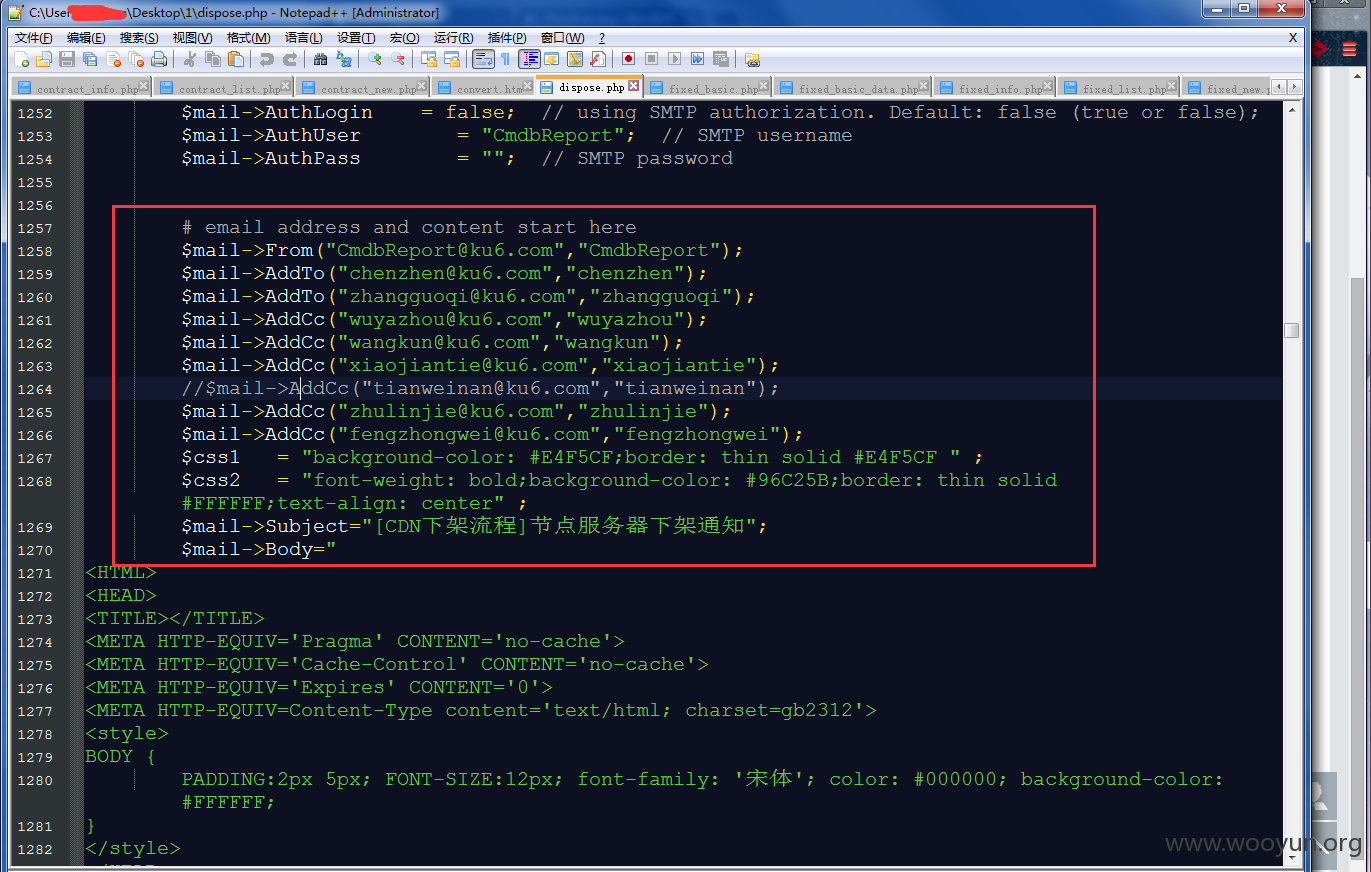
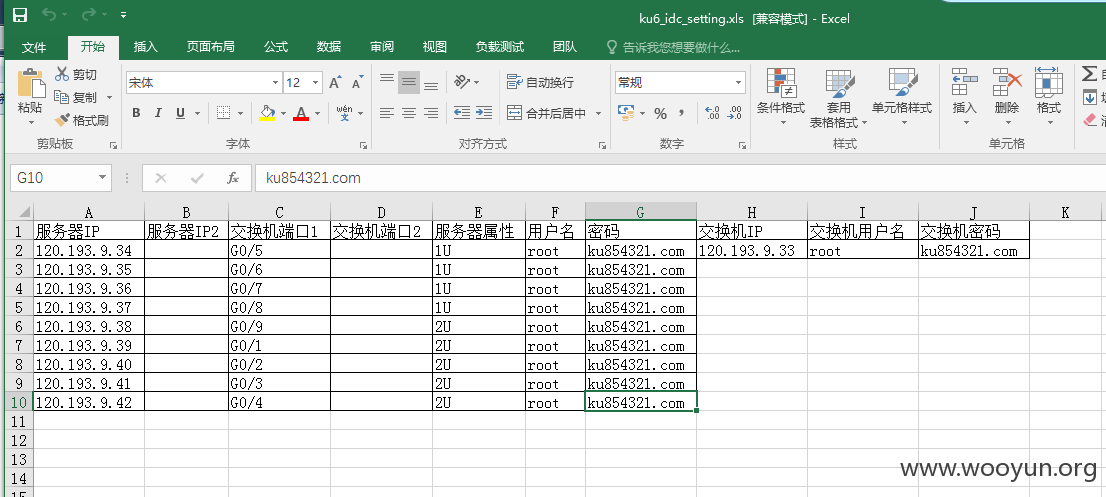
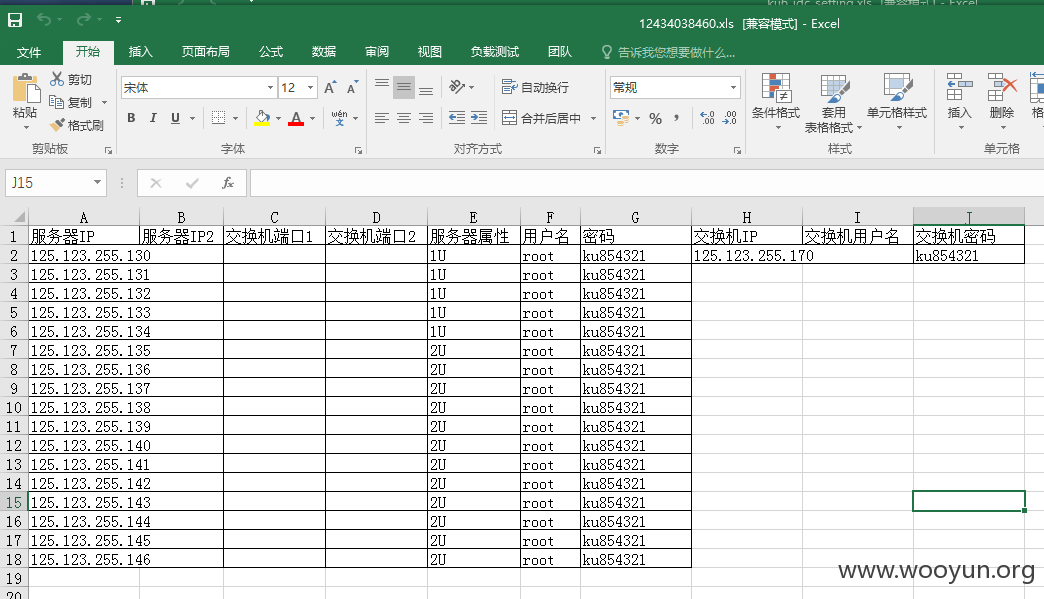
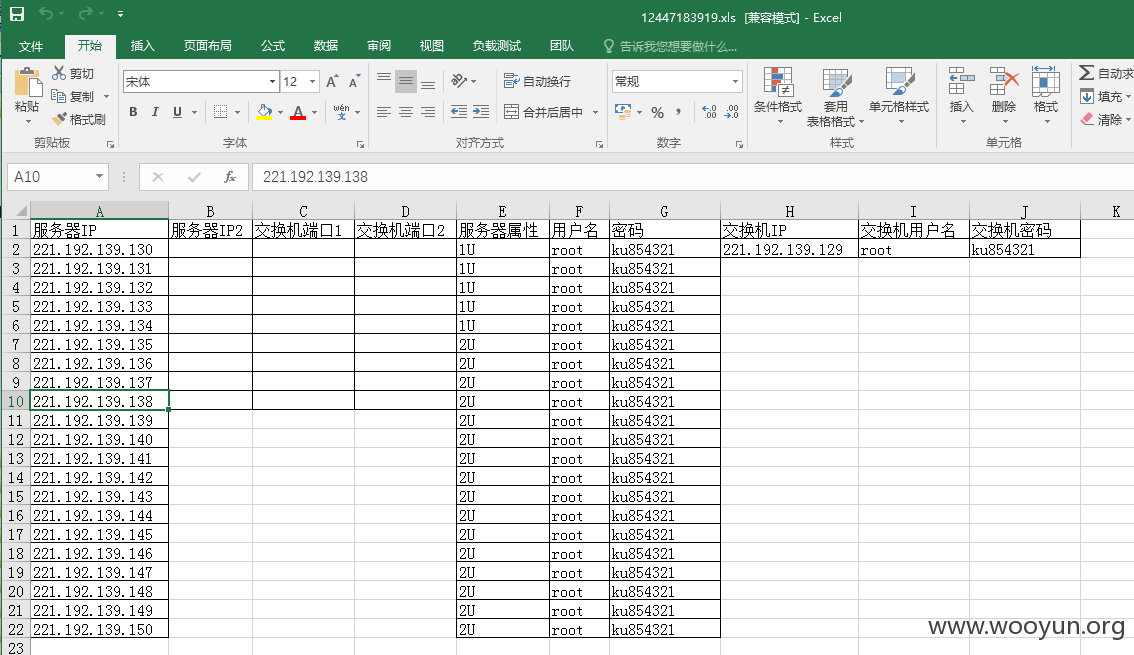
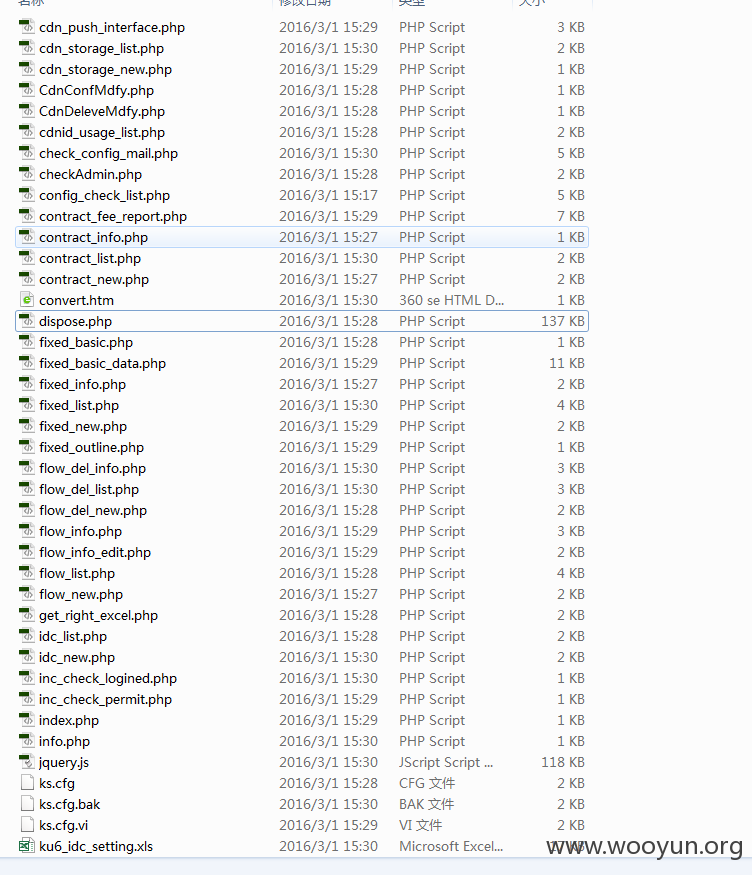
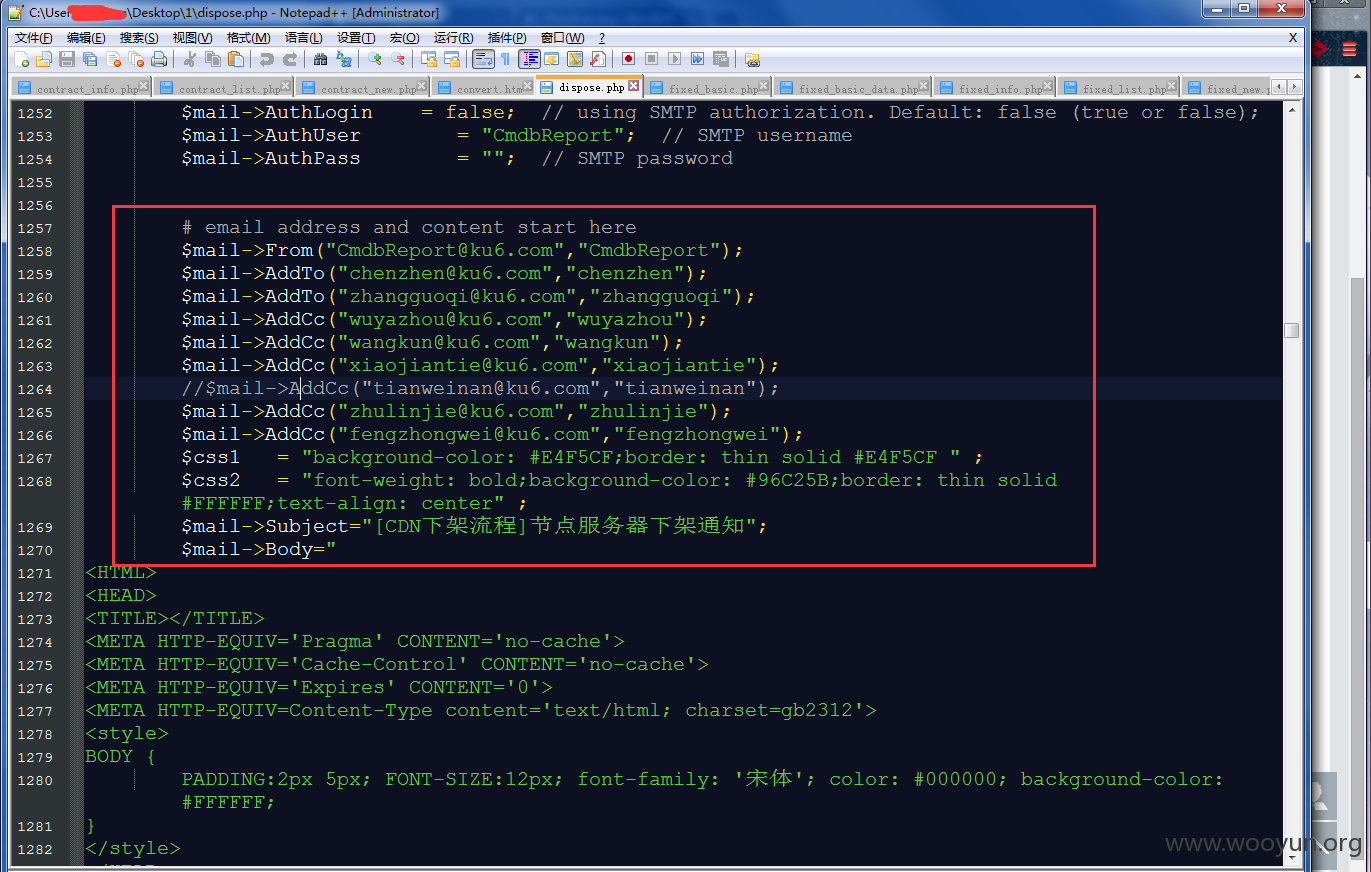
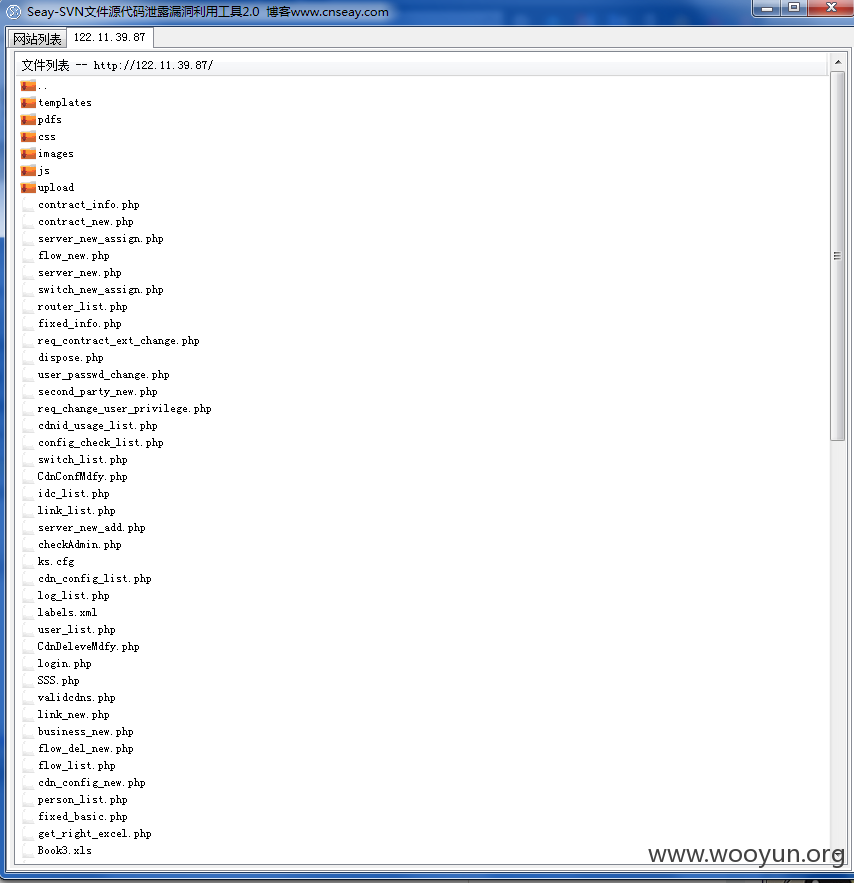
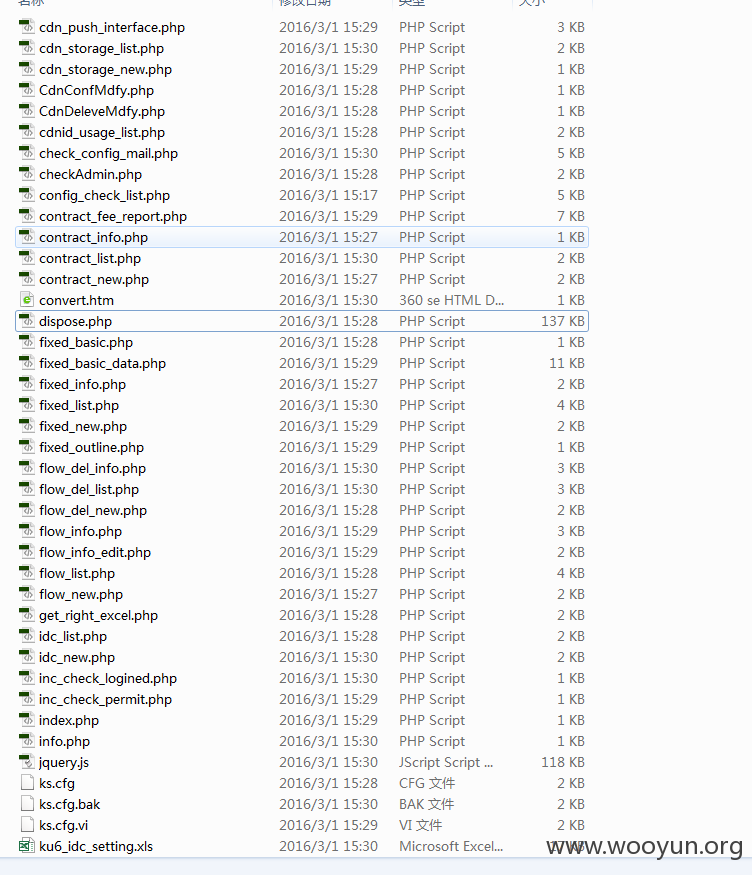
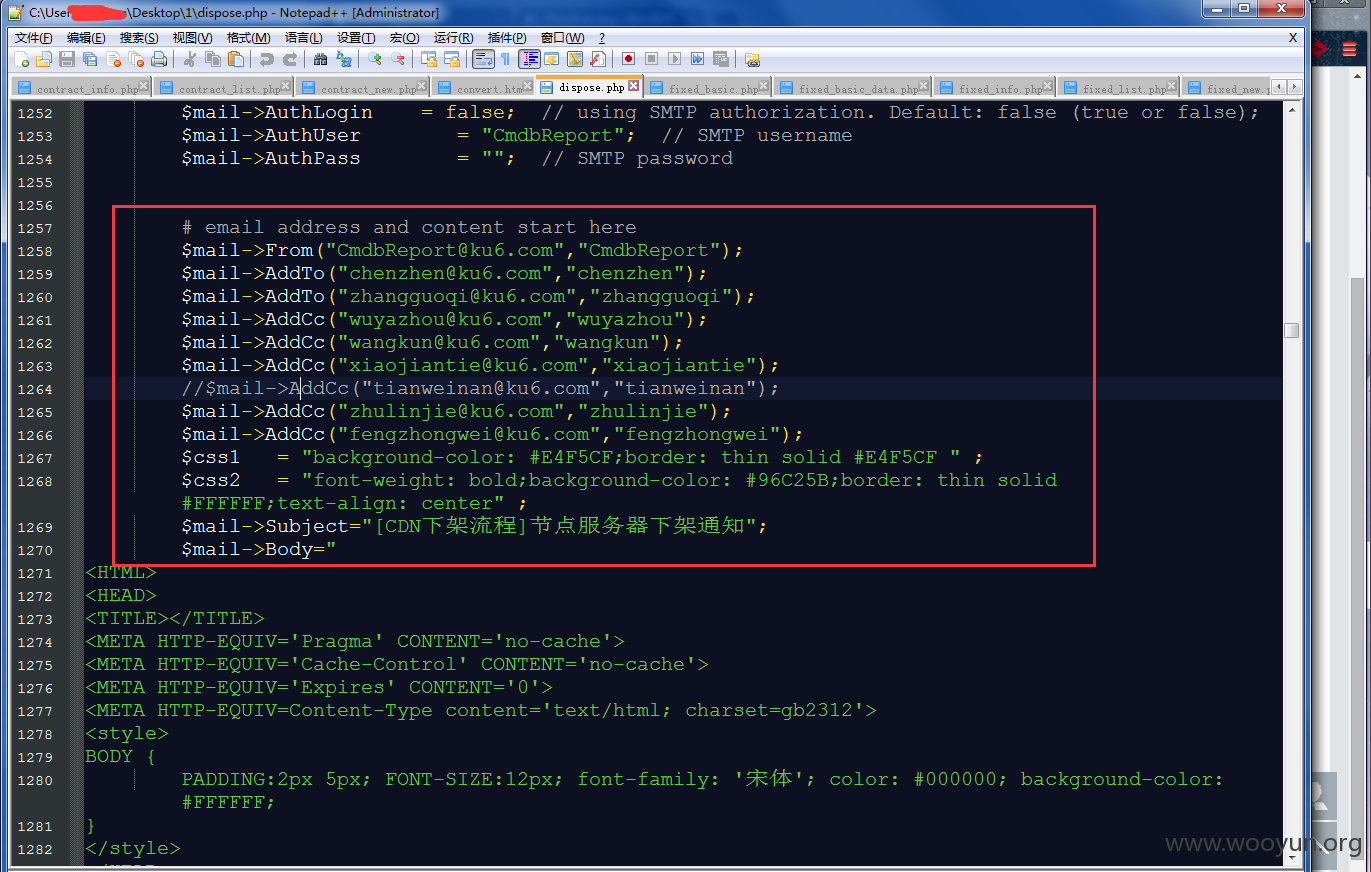
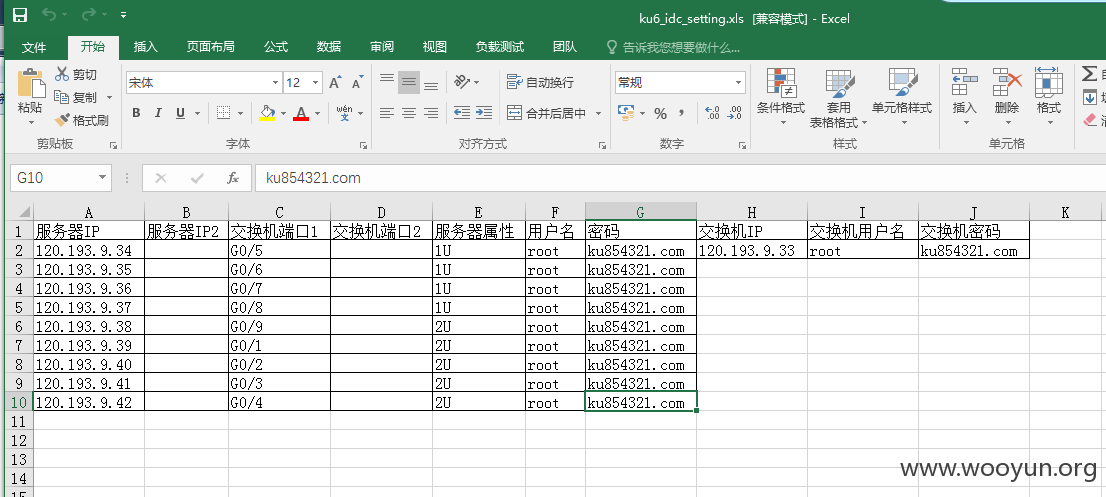
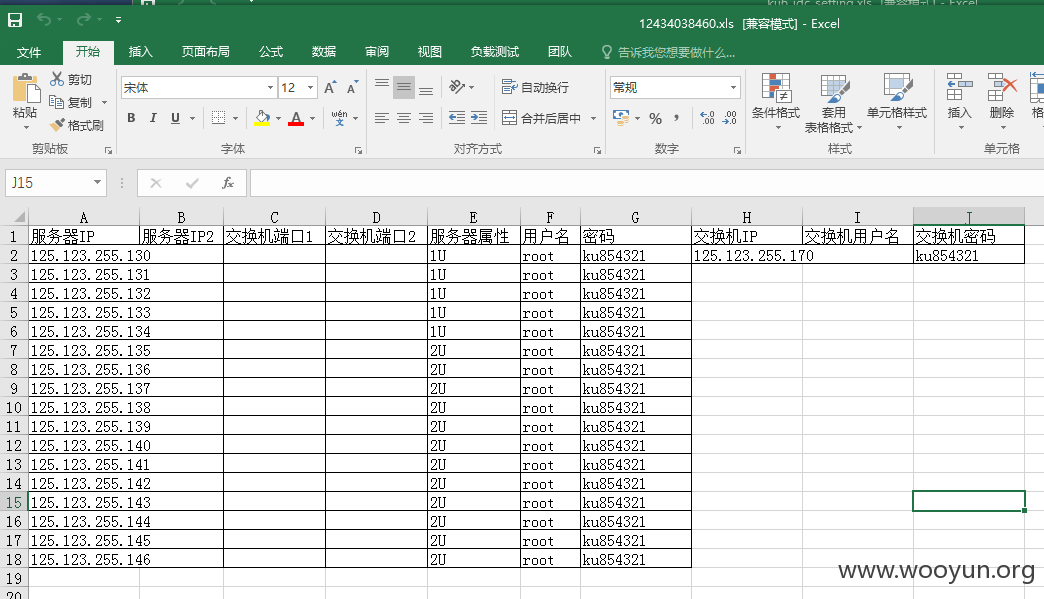
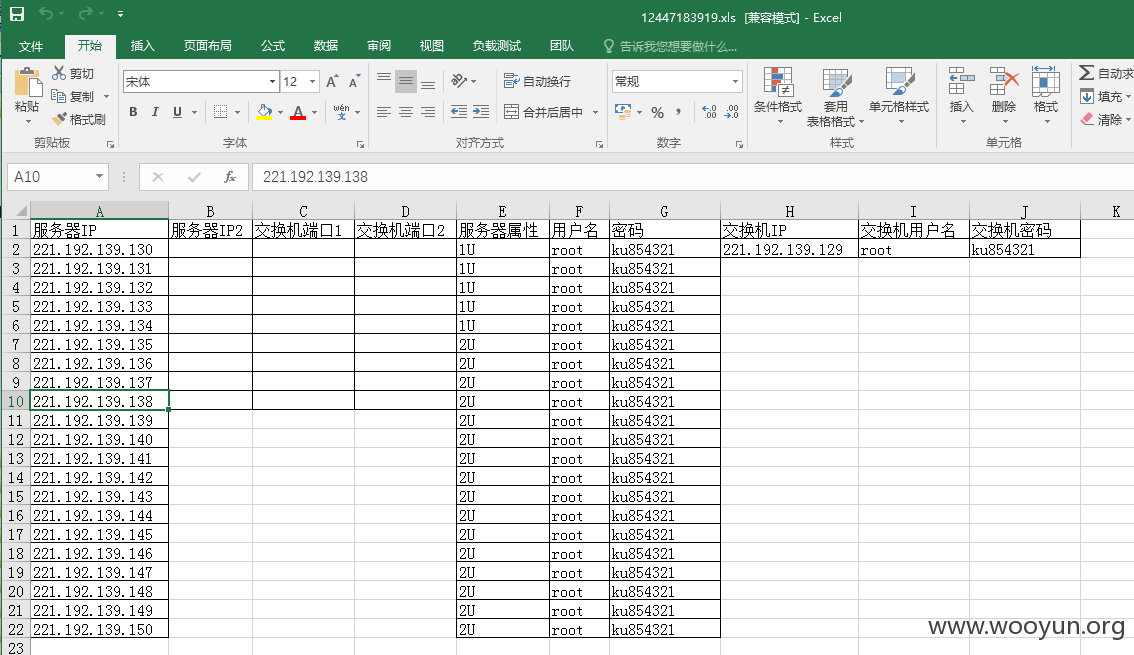
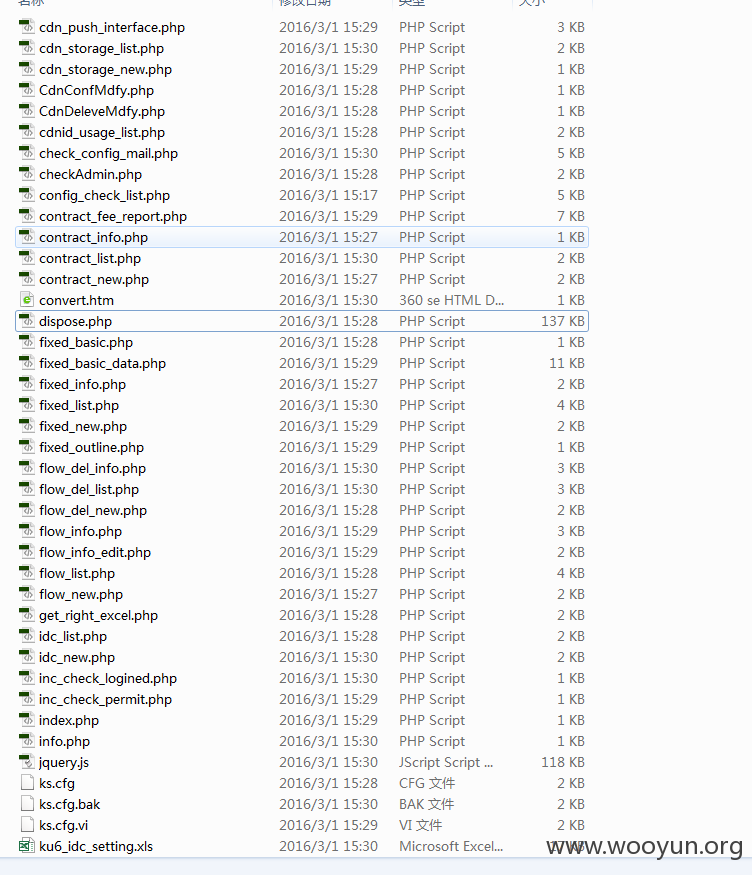
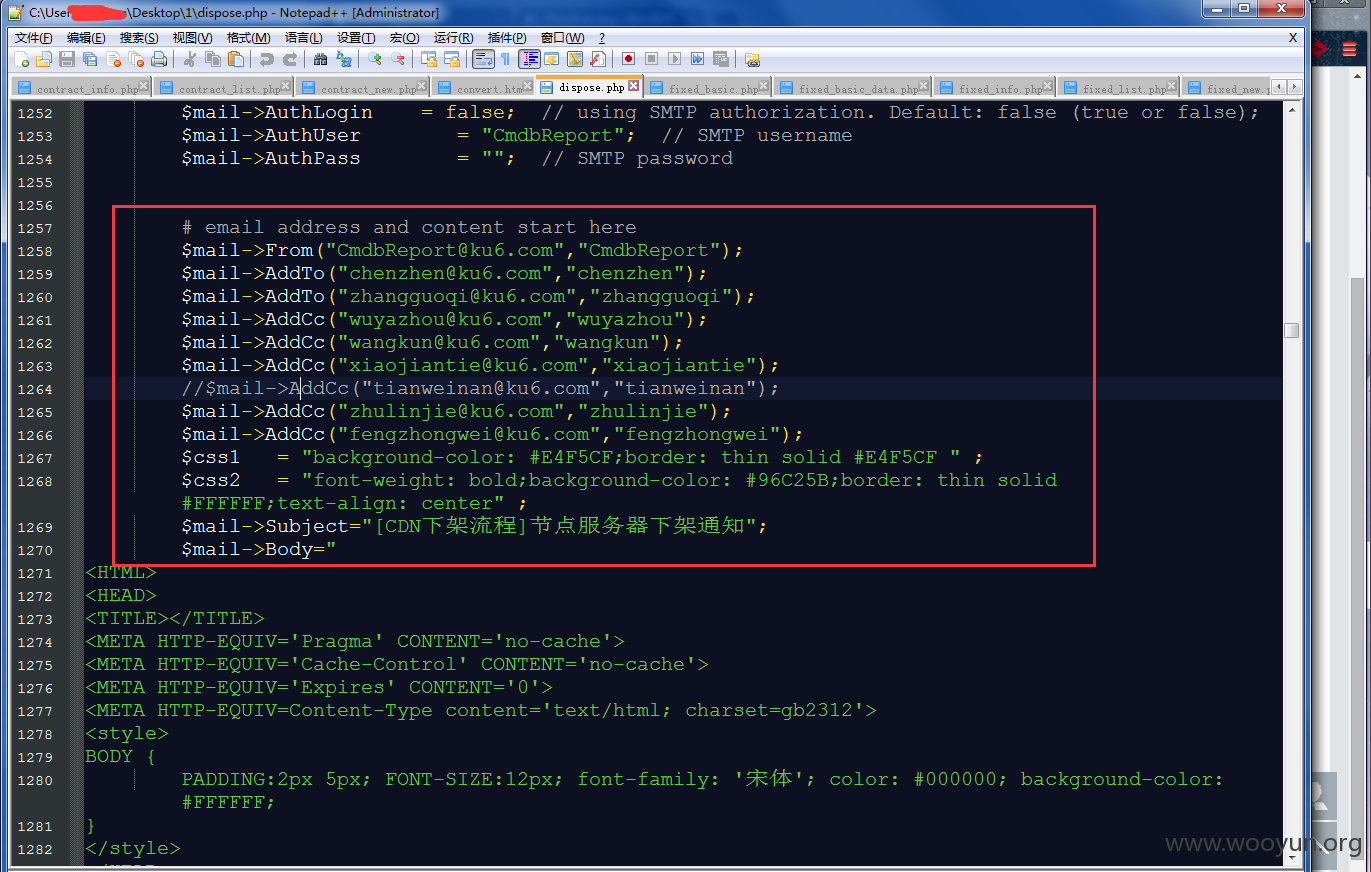
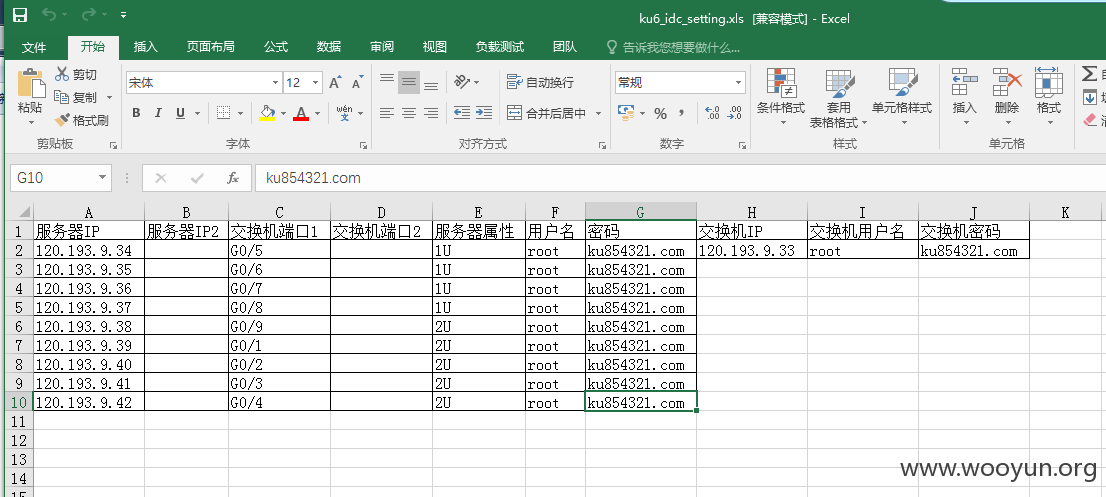
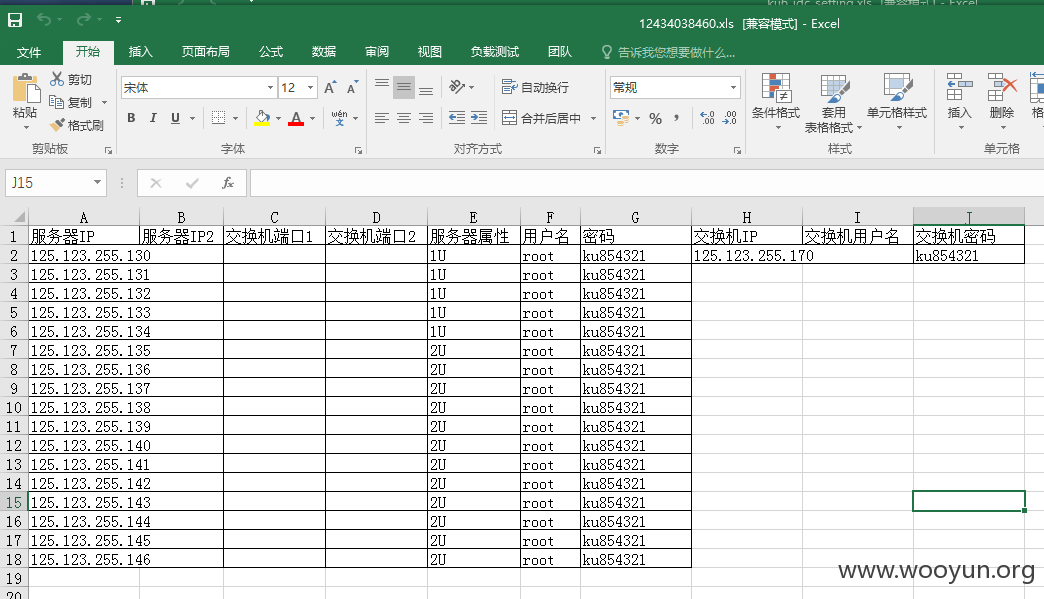
酷6网某ip存在svn信息泄露
详细说明:
http://122.11.39.87/.svn/entries
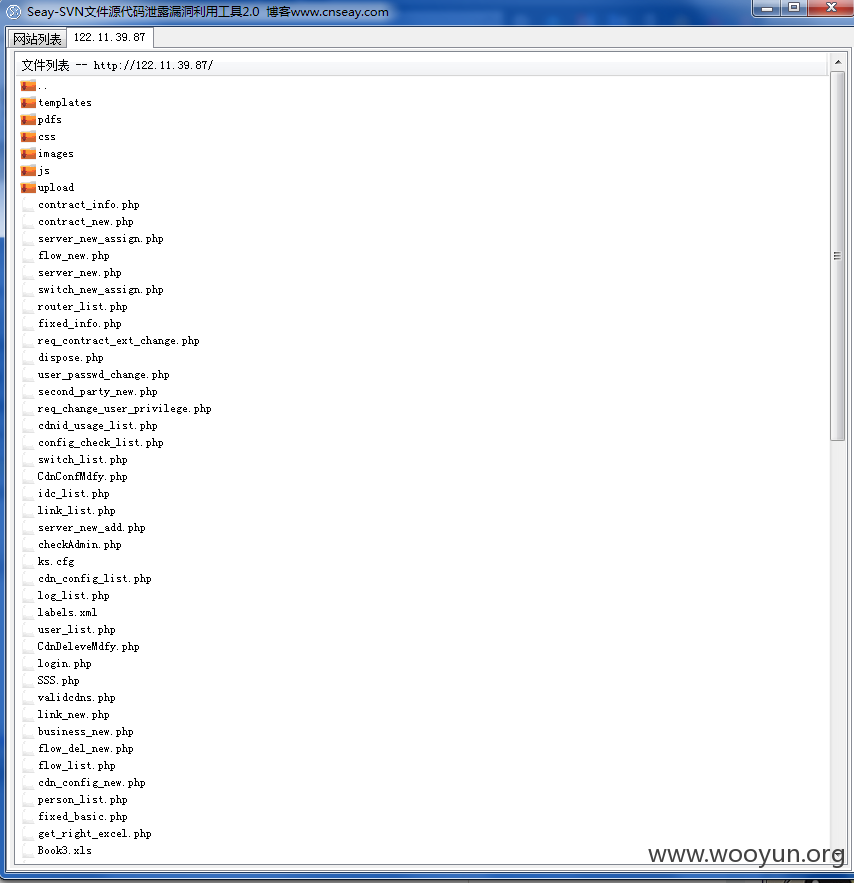
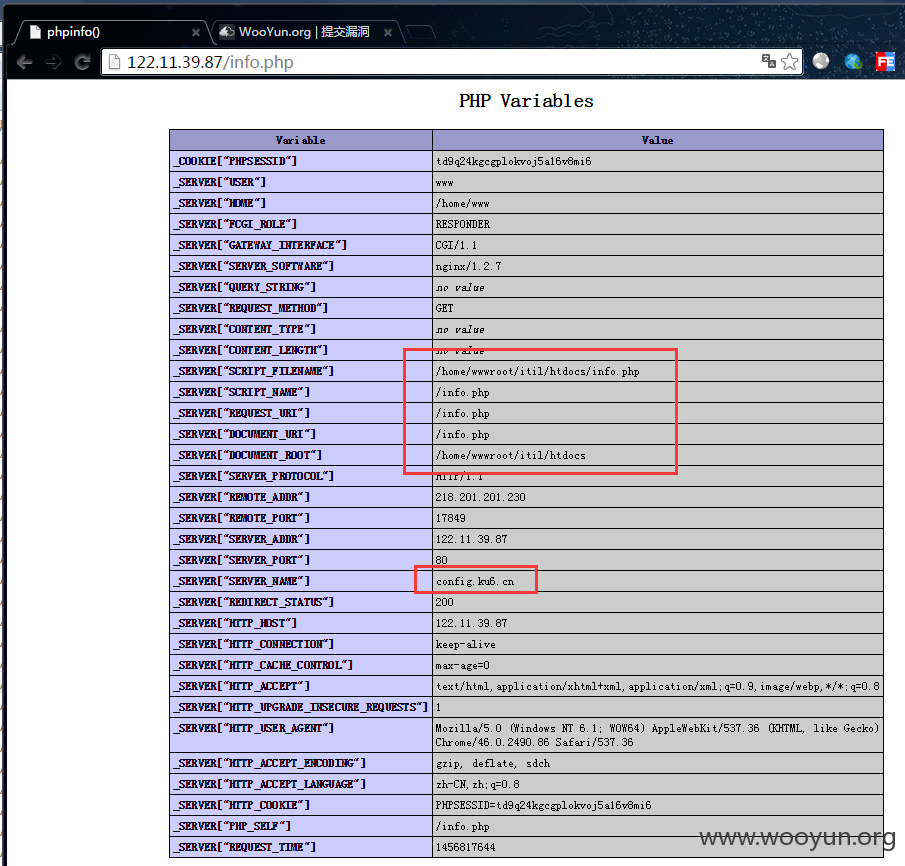
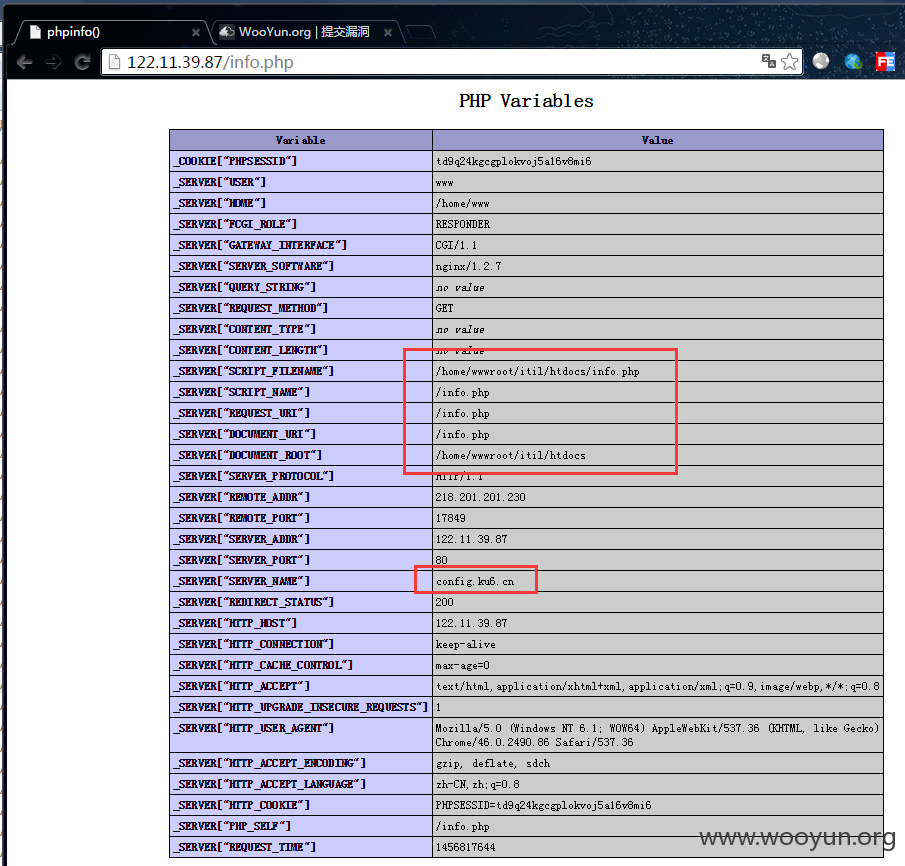
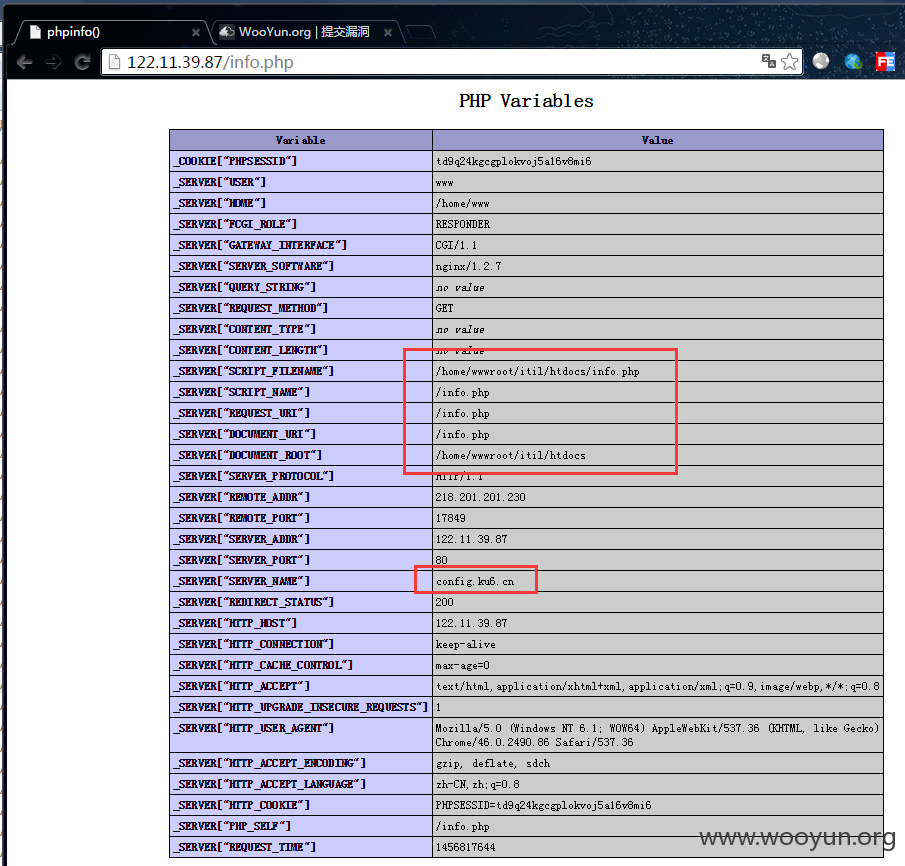
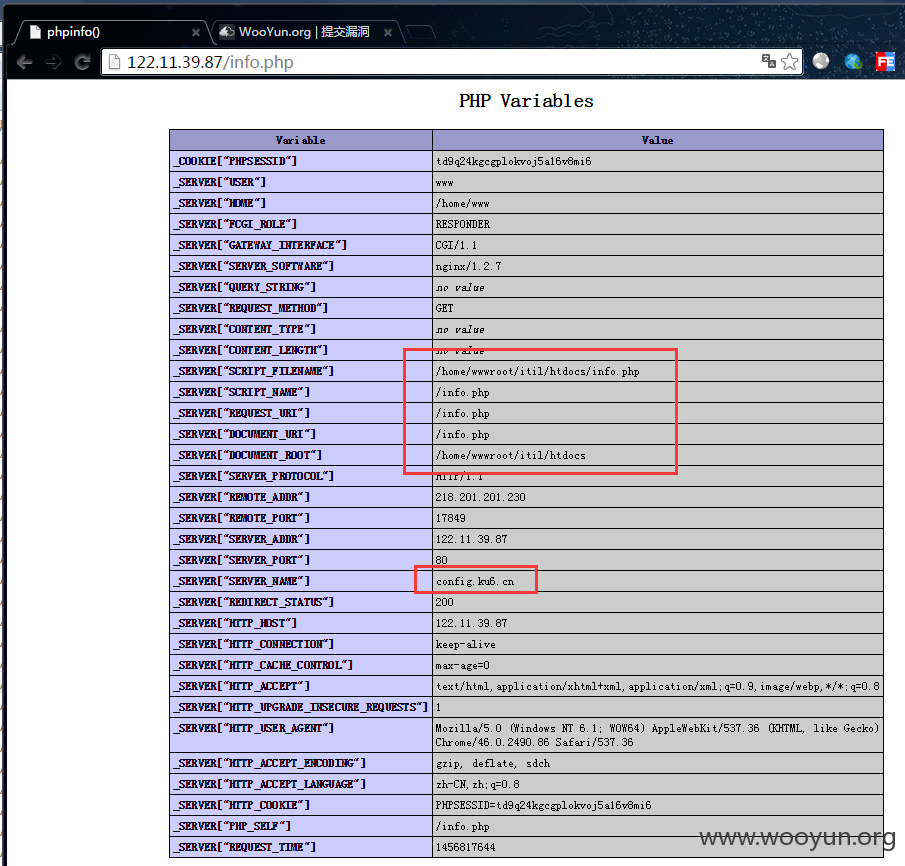
http://122.11.39.87/info.php phpinfo
漏洞证明:
http://122.11.39.87/.svn/entries
http://122.11.39.87/info.php phpinfo
修复方案:
http://122.11.39.87/.svn/entries
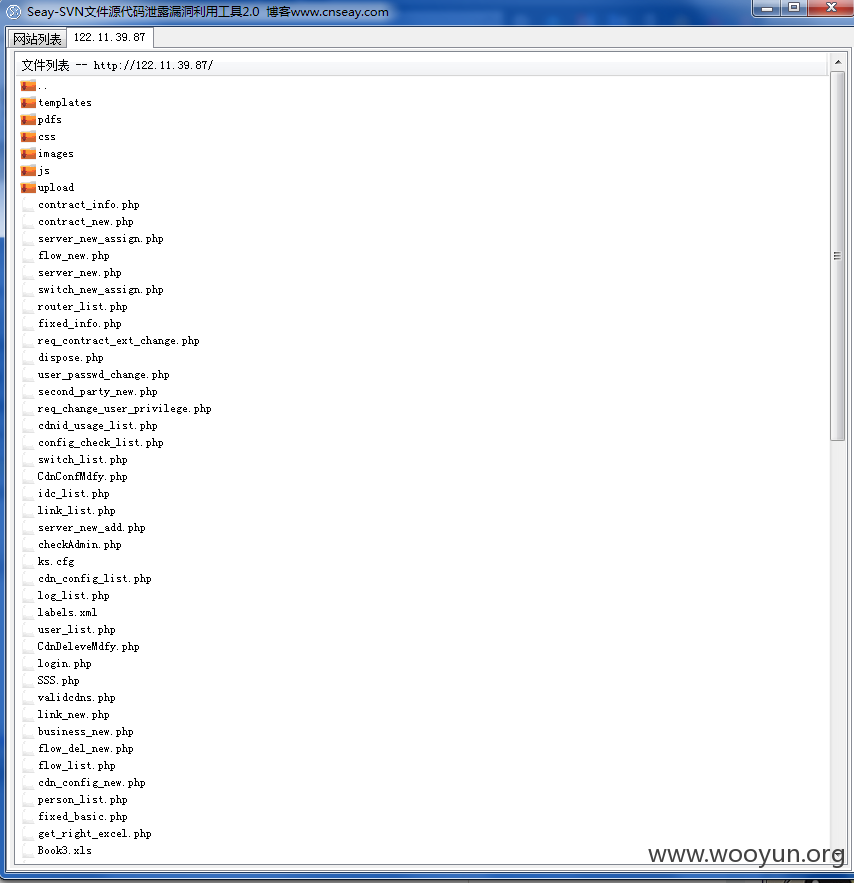
http://122.11.39.87/info.php phpinfo
>
漏洞回应
厂商回应:
危害等级:无影响厂商忽略
忽略时间:2016-03-06 17:00
厂商回复:
漏洞Rank:4 (WooYun评价)
最新状态:
暂无